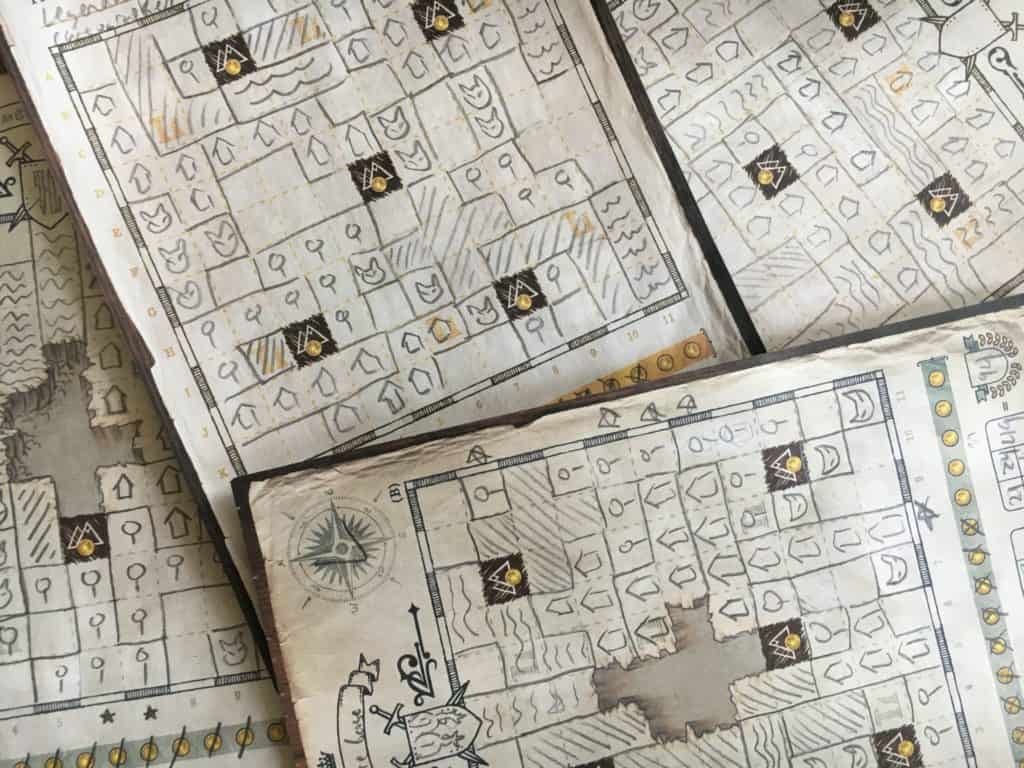
Cartographers is a fairly straightforward game. However, Cartographers strategy isn’t straight forward at all. While making a map, you’ll be presented with many ways to score, and you must puzzle out the best way to do so by drawing shapes on your map in this Roll and Write game.
While a vast majority of your choices are very specific to your map and wholly unsuited for a strategy guide, there are a handful of general tips to improve your game.
So let’s get started.
Priorities
Cartographers is a game where you always have 10 goals to aim for, and not enough time or space to pursue them all. So much of the strategy comes down figuring out which goals to prioritize, and which goals to give less attention to.
Monsters Strategy in Cartographers
In the first half of the game, your first priority should generally be surrounding monsters if you’ve drawn any. A single unfilled square adjacent to a monster drawn in Spring is -4 points if you never fill it in, but in Winter, it’s only -1 point. Since removing a negative point is just as good as scoring a point, these should almost always be your highest priority. Especially when they come up early, since a single shape can frequently prevent the loss 8-16 points.
Coins Strategy in Cartographers
As a first rule of thumb, go aggressively for coins early. The same logic as monsters applies to coins: coins are incredibly good if you can get them in Spring, because they’re most valuable then. A single coin in Spring is worth 4 points, while in summer it’s worth 3, and in Winter, coins are only worth 1 point. When given the choice to take a smaller shape and a coin in Spring and Summer, it’s usually better to take the coin. Obviously, calculate if the other shape might be worth more, but going for the coin is always a safe bet when you’re not into doing math. This goes for surrounding mountains too, which is important early, and less important later.
In Fall and Winter, coins are just a solid bonus, but not always the right choice.
Predicting How Much a Card Can Score
So, its great to know that in each season, you will draw an average of 2 cards for each type of terrain (including split-choice terrains). You might draw 0 forests, or you could draw 4 forests, but you’d need some luck for either of those outcomes. You should plan for 2 cards.
On average, that means you will get to fill about 10 total grid spaces on your map with a single type of terrain, per season (if you always pick that type of terrain, and if you pick the larger blocks).
Now, what does this mean strategically? Well, when you’re choosing between terrain types to place, you can calculate how many points you’d get if got just two shapes of that terrain in that season.
I have some examples in the next section below.
Scoring Cards
What scoring cards you prioritize depends on what shape cards you’re drawing, what’s on the board already, what the other scoring cards are, etc. However, there are rules of thumb that I follow to make sure I get the most out of them. Much of what Cartographers strategy is, is prioritizing how you will aim for these score cards.
First of all, not all cards are as easy to score with as the others.

Given those averages in the section above, you can calculate how likely you’ll be able to score with each card. For example, if you had Wildholds in scoring spot B, you’d can expect 8 points in Spring, and 16 points in Summer, given a little luck, and some good planning. We can estimate this since luck says you ought to draw 2 house terrain cards in Spring for one group of 6, and another two in Summer, for your second group of six.
Remember that a group of 5 houses only needs a single tile to get to six, which means a single Riftlands could get you there if you plan for it (which means never put a Riftlands house into a group of 3-4 houses, as any two tiles can make six even without it), which means you might even get 16, then 24 points.
For the Great City in scoring space A, you can expect to score 10 points in Spring if you plan on taking the larger tiles, but as much as 40 points in Winter.

The score cards with the grey arrow backs can reliably score quite high: they all have the potential to double or triple the solo mode score in the lower right corner of the card (except The Cauldrons, which is just far harder to score with). If you have the Lost Barony, Borderlands or The Broken Road in positions A or D, with a little luck, you ought to be able to score 30+ points for it in a single season if you play your game around fulfilling that condition (and 50+ for Borderlands). These cards don’t care about which specific pieces you draw, so they are the most consistently high scoring cards. However, if it ends up in position B or you draw The Cauldrons, just know they are much harder to score for, and don’t worry about them as much.
These cards should generally inform how you place things. If you have The Broken Road, you ought to consider placing every piece in the bottom left corner, or as close as you can. For the Lost Barony, start around a mountain and work towards the middle of the map.

A lot of the advice above applies to these as well. For example, in a single season, expect two forests. So if Stoneside Forest is you A score card, it can score up to six points, but almost as likely to score 0 points, which isn’t great. So I’d choose not to prioritize it. On the other hand, Greenbough and Sentinel Wood can score nearly (and sometimes above) 1 point per tile you put down, which is worth prioritizing, especially if it scores late.

I actually like all four of these cards, they’re all capable of scoring really highly, especailly Shoreside Expanse, which can be very rewarding if well planned out. This one can lose points very easily unless you plan it out well though. The Golden Granary is great if you score for it early, since its one of the easier requirements to meet in the first turns, while guaranteeing some points.
Calculating Scores
Now, the game comes with an easy way to see how you’re doing. If you look in the bottom right corner of each scoring card, there’s a number. That’s the expected score for that card (used only for solo play). For each season, you can half that number and compare your score for that card to that number. If your score is smaller, then you’re behind. If it’s larger, then you’re ahead.
In the early seasons, you’ll often be behind, but for every point you miss early, you have to catch up on late. If you find that you’re always head of that curve, then you know you have a pretty strong Cartographers strategy. However, do note that sometimes, you will be way behind, since this game does have a lot of luck.
Conclusion
Well, I hope you liked it. Let me know if you have any Cartographers strategy tips for the game that I didn’t mention.
Maybe check out some of my other strategy guides if you liked this one.


Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Your article helped me a lot, is there any more related content? Thanks! https://www.binance.info/register?ref=IXBIAFVY
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Hiya, I am really glad I have found this information. Nowadays bloggers publish just about gossips and web and this is actually irritating. A good website with interesting content, that’s what I need. Thanks for keeping this web site, I will be visiting it. Do you do newsletters? Can’t find it.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good. https://www.binance.info/register?ref=IXBIAFVY
Your article helped me a lot, is there any more related content? Thanks!
Производство и поставка – канат декоративный производства Северсталь метиз, Мечел, ММК Метиз, Силур со склада в г.Орел.
Продажа канат которым привязывается РјРѕСЂСЃРєРѕРµ СЃСѓРґРЅРѕ оптом и в розницу по низким ценам.
Полный каталог всей метизной продукции, описания, характеристики, ГОСТы и технические условия.
Оформление заказа и доставка в сжатые сроки. Возможна отгрузка транспортной компанией.
Цены производителя.
Наша компания предлагает сетка тканая цена производства Северсталь метиз ОСПАЗ со склада
г.Орел. В наличии огромный ассортиментсетка тканая штукатурная.
Вы можете купить куплю сетку тканую светлую и оцинкованную.
У нас всегда в наличии огромный выбор сетка тканая фильтровая, цены от производителя.
Продажа тканая сетка магазин оптом и в розницу со склада г.Орел.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article. https://accounts.binance.info/da-DK/register-person?ref=V3MG69RO
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you. https://accounts.binance.info/ka-GE/register-person?ref=ILE8IH9H
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article. https://www.binance.info/en-NG/register?ref=YY80CKRN
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Trying to get in on MNL63! The login, register and download process was pretty smooth so far. Let’s see about the games! Give it a shot : mnl63 login register download
MNL63 PH, is it legit for us here in Philippines? Saw some ads earlier. Let’s try it out for fun. Here’s the link: mnl63 ph
Just registered on MNL63. Registration was quick and painless. Hope the games are just as good! Quick and easy: mnl63 register
https://ipn.md/atac-tehnic-si-discreditare-publica-companie-it-din-moldova-impinsa-in-afara-pietei-europene/
energy casino
References:
waterdropfilms.com
stack’d supplements
References:
posteezy.com
blackjack rules chart
References:
https://dribrahimjalojalingo.com/
dbol steroids results
References:
http://ezproxy.cityu.edu.hk/
spirit mountain casino oregon
References:
https://blog.mumzworld.com/use-chores-to-build-up-your-kids-sense-of-responsibility
https://colombocar.com/
what kind of steroids are there
References:
stackoverflow.qastan.be
fruit machine games
References:
dainikup.com
Thanks for sharing. I read many of your blog posts, cool, your blog is very good. https://accounts.binance.info/en-NG/register-person?ref=YY80CKRN
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Your article helped me a lot, is there any more related content? Thanks!
References:
Crown casino cinema
References:
figurejeju.com
References:
Best online blackjack
References:
watbosa.ac.th
casino cleveland ohio
References:
exclusiv.kz
casino chicago
References:
dkbeauty.co.uk
sugar creek casino
References:
sciencebookmark.space
valencia hire a car https://drivelity-spain.com/car-rental-valencia-spain
стоимость лечения зубов детей лечение молочных зубов под наркозом у детей
ремонт ванной ключ https://remont-vannoy-spb.ru
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Need a multimedia system? i-tec We integrate multimedia systems for home and business. We install and configure audio and video systems, manage content, and integrate equipment into a single system. Modern solutions for comfortable and efficient use of technology.
Дополнительная информация: https://l-parfum.ru/catalog/testeri_duhov/Davidoff/
Хочешь казино бонус? топ новых бонусов без депозита всегда актуальные бонусы в онлайн казино. Получайте бонусы без вложений, фриспины и подарки за регистрацию. Актуальные предложения, честные условия отыгрыша и список проверенных казино с бонусами без депозита.
Лучшие казино рейтинг онлайн казино: актуальный список онлайн казино с высоким рейтингом, быстрым выводом средств и выгодными бонусами. Обзор лицензий, игр и платежных методов поможет выбрать надежное казино для комфортной игры.
Халява казино рейтинг казино с бонусами за регистрацию: фриспины за регистрацию, бонусы без пополнения и акции для новых игроков. Сравнивайте условия отыгрыша, выбирайте проверенные онлайн казино и начинайте играть бесплатно с возможностью вывода выигрыша.
Лучшие фриспины 2026 бездепозитные казино: бесплатные вращения в онлайн казино без вложений. Подборка проверенных сайтов, бонусы за регистрацию, честные условия отыгрыша и возможность вывода выигрыша без риска для игроков.
Официальный сайт pokerok: регистрация, вход, бонусы и игра в онлайн покер. Обзор возможностей, турниров, кеш-столов и мобильного приложения. Узнайте, как начать играть и выводить деньги на проверенной платформе.
Fast decoder open link provides complete vehicle data from 17-character identification number.
Online tool visit page provides peace of mind by verifying vehicle has no undisclosed damage history.
Fast booking private jet charter fly gets your private charter flight confirmed in under 30 minutes guaranteed.
Transparent pricing rentprivatejetfly.com helps you understand exactly how much a private jet costs per flight.
Нужен дизайн участка? ландшафтный дизайн услуги проектирование и благоустройство участка с учетом рельефа, растений и стиля. Создаем красивые и функциональные решения для частных домов и дач, подбираем материалы и обеспечиваем качественную реализацию проекта.
Брендирование сувениров https://4youcreation.kz/tisnenie/ в Алматы по современным технологиям. Специалисты предлагают лазерную гравировку, УФ-печать и термоперенос на ткани, стекло, металл и пластик. Организуют доставку по всему Казахстану.
Компания FarbWood https://farbwood.by предлагает пиломатериалы из сибирской лиственницы для частного и коммерческого строительства в Минске и по всей территории Минска. Мы работаем только с лиственницей сибирской, сосна и ель используются как дополнение к основному ассортименту древесины.
Нужна накрутка соц сетей? накрутка просмотров инстаграм увеличение подписчиков, лайков и просмотров для продвижения аккаунтов. Быстрый старт, безопасные методы и живая активность помогут развить профиль и повысить вовлеченность в популярных социальных платформах.
The best porn generator ai porn chat your fantasies remain strictly between you and the neural network. Instant, high-quality generation, extensive scenario and character customization.
Текущие рекомендации: https://uquest.net/demontazh-fundamenta-i-razbor-derevyannogo-doma-kak-podgotovit-uchastok-pod-novoe-stroitelstvo.html
References:
Play chuzzle online
References:
https://instapages.stream/story.php?title=crypto-casino-licensing-guide-bitcoin-gaming-compliance-2024
Experienced supplier business manager on facebook offers complete asset packages including login credentials, recovery access, 2FA codes, cookies, and user-agent data. Transparent replacement policy covers the first-login window and ensures buyers receive exactly what is described on the product card. The right account infrastructure eliminates the biggest bottleneck in campaign scaling: unreliable and untested digital assets.
Dedicated platform buying discord servers helps performance teams find the right account infrastructure for scaling their advertising operations efficiently. Step-by-step documentation accompanies every order, covering login procedure, security setup, and recommended first actions after access. Invest in verified account infrastructure and redirect the time saved from troubleshooting into actual campaign optimization work.
Professional service buy aged gmail accounts pva 2024 specializes in accounts optimized for paid campaigns with proper warming history and platform trust markers. Orders are processed through a secure checkout system with multiple payment options and encrypted credential delivery via personal dashboard. Scale your advertising operations on a foundation of quality — verified profiles, complete credentials, and expert operational support.
Specialized store buy google ads accounts bulk focuses exclusively on accounts proven to perform in paid advertising with real spend history and trust indicators. Geo-targeted options cover USA, UK, Germany, France, Poland, Ukraine, and other regions with proper IP history and locale settings. Invest in verified account infrastructure and redirect the time saved from troubleshooting into actual campaign optimization work.
Full-service dealer instagram live streaming guide 2026 goes beyond selling by providing operational guides, restriction breakdowns, and platform update summaries. Transparent replacement policy covers the first-login window and ensures buyers receive exactly what is described on the product card. Build your campaigns on accounts with proven trust — higher trust means better delivery, lower costs, and fewer interruptions.
Full-service dealer imap for hotmail goes beyond selling by providing operational guides, restriction breakdowns, and platform update summaries. The selection includes profiles sorted by registration method, warming protocol, age, and included assets so buyers can match accounts to their specific needs. Teams that prioritize account quality over raw volume consistently achieve better ROI and fewer campaign interruptions.
Leading store what is protonmail gives media buyers access to aged, warmed, and verified profiles sorted by geo, trust level, and ad readiness. Geo-targeted options cover USA, UK, Germany, France, Poland, Ukraine, and other regions with proper IP history and locale settings. Whether you need accounts for testing or production campaigns, the catalog covers every tier from entry-level to premium.
Full-service dealer reddit account purchase goes beyond selling by providing operational guides, restriction breakdowns, and platform update summaries. The team provides onboarding guidance for new buyers and ongoing operational support for teams managing high-volume campaign portfolios. Instant delivery, verified quality, and dedicated support — everything a professional advertiser needs in one marketplace.
Full-service dealer yahoo accounts shop goes beyond selling by providing operational guides, restriction breakdowns, and platform update summaries. Each listing comes with complete access data including email, password, cookies, token, and user-agent string for seamless campaign setup. Every order comes with clear documentation, replacement guarantees, and access to a growing knowledge base of operational resources.
Full-service dealer youtube 2fa goes beyond selling by providing operational guides, restriction breakdowns, and platform update summaries. Geo-targeted options cover USA, UK, Germany, France, Poland, Ukraine, and other regions with proper IP history and locale settings. Competitive pricing, fast delivery, and professional support make this a preferred choice for serious media buyers.
интерьер дизайнер дизайн проект купить
дизайн коттеджа дизайн интерьера дома
This was a useful and absorbing read. I appreciate when an article values the reader’s time while still offering substance, and I’m glad you published it.
дизайн интерьера спб студия дизайна и интерьера
проект дома дизайн https://dizayn-interera-doma.ru
The best porn generator porngen ai generator your fantasies remain strictly between you and the neural network. Instant, high-quality generation, extensive scenario and character customization. Available 24/7. For adults.
Лучшее прямо здесь: https://www.bitchute.com/channel/f72rl1tobb7g
Useful resource https://bestguitarreview.com/ breaks down guitar specifications and compares models across all price ranges.
Find your perfect https://bestheadphonereview.com/ headphones with detailed comparisons of noise cancelling and audiophile models.
Top rated resource bestmicrophoneguide.com reviews microphones by use case including home studio and professional recording.
Последние публикации: http://www.pnzstroi.ru/obzory/124710/3-oshibki-pri-podgotovke-3d-modeli-agr/
Советы автомехаников https://proavtomaster.com полезные рекомендации по ремонту и обслуживанию автомобиля. Узнайте, как продлить срок службы двигателя, подвески и электрооборудования, избежать частых поломок и сэкономить на ремонте благодаря практическим советам специалистов.
Профессиональный автосервис https://km-motors.org кузовной ремонт, покраска авто, ремонт двигателя и подвески. Компьютерная диагностика, автоэлектрика, ТО, замена масла, фильтров и шиномонтаж. Работаем быстро, качественно и по стандартам производителей.
Компания «Заборыч» https://заборыч.рф более 10 лет осуществляет строительство заборов из профнастила и сетки рабицы. Мы производим заборы для частных лиц и производственных объектов. За это время мы построили десятки объектов, от простых ограждений до сложных ландшафтных комплексов. Наши клиенты остаются довольны качеством работ и сроками реализации проектов.
суть шлюх голые порно
Профессиональная помощь детям https://neuropsy-centr.ru с нарушениями речи и развития. Высококвалифицированные врачи, работаем с самыми тяжелыми случаями, 99% положительных отзывов, новейшее оборудование и инвентарь. Государственная лицензия: Л035-01298-77/01604531 от 09.12.24
Платная частная клиника https://mypsyhealth.ru/services/psikhiatricheskaya-klinika психиатрии, неврологии и наркологии — анонимное лечение и консультации специалистов. Диагностика, помощь при зависимостях, неврологических и психических расстройствах. Конфиденциальность, опытные врачи и комфортные условия.
модульные дома сайт модульный дом с отделкой
Самое полезное для вас: https://paradstars.com/index2.php
Скоро лето и жара кондиционер купить с установкой в московской области широкий выбор сплит-систем для квартиры, дома и офиса. Поможем подобрать модель по площади, бюджету и характеристикам. Установка под ключ, гарантия, доставка и выгодные цены на популярные бренды.
Top web design https://webdesignfirmshub.com companies worldwide: a selection of the best studios for website and interface creation. Learn about case studies, design approaches, UX/UI solutions, and innovations to help you choose a reliable contractor for your digital projects.
Top branding agencies https://topbrandagencies.com worldwide: the best studios for brand development, corporate identity, and positioning. Portfolio reviews, strategies, and case studies will help you choose a reliable agency for business development and brand enhancement.
Top UX/UI design https://uiuxagencies.com agencies: the best companies creating user-friendly interfaces and digital products. Explore case studies, methodologies, and approaches to UX/UI to choose a reliable contractor for your website or app.
A non-profit organization https://linkimpact.org dedicated to supporting multicultural families, environmental protection, volunteerism, and language and cultural exchange.
Дубликаты номеров https://avtostrahovka36.ru в Воронеже — изготовление и восстановление регистрационных знаков по ГОСТ. Срочно за 1 день, качественные материалы, соответствие требованиям и выгодные цены. Оформление быстро и без очередей.
Практик о заборах https://sinta-kedr.ru/ честный разбор материалов, установки и стоимости. Узнайте плюсы и минусы разных видов заборов, частые ошибки и реальные сроки службы. Полезные рекомендации перед покупкой и монтажом ограждений.
An astrology portal https://burcler.com.az/ with daily horoscopes, natal charts, and forecasts. Online consultations, zodiac sign compatibility, and personalized recommendations will help you better understand yourself and make important decisions.
References:
Bodybuilding steroids before and after
References:
http://121.36.47.159:3000/adalbertodewit
Дубликаты номеров https://avtostrahovka36.ru в Воронеже — изготовление и восстановление регистрационных знаков по ГОСТ. Срочно за 1 день, качественные материалы, соответствие требованиям и выгодные цены. Оформление быстро и без очередей.
Практик о заборах sinta-kedr.ru честный разбор материалов, установки и стоимости. Узнайте плюсы и минусы разных видов заборов, частые ошибки и реальные сроки службы. Полезные рекомендации перед покупкой и монтажом ограждений.
Все новостройки https://tut-novostroyki.ru от застройщиков в Новосибирске — актуальный каталог квартир в новых ЖК. Цены, планировки, сроки сдачи и акции. Подберите квартиру напрямую от застройщика без комиссии с удобным поиском и проверенной информацией.
Дизайнерское бюро https://vseremontytut.ru проектирование интерьера и ремонт под ключ. Разработка дизайн-проекта, 3D-визуализация, подбор материалов и полная реализация. Создаем стильные и функциональные пространства с гарантией качества и соблюдением сроков.
Шпаклевка стен https://shpaklevka-sten.ru и потолков в Москве — выравнивание поверхностей под покраску и обои. Качественные материалы, опытные мастера и соблюдение технологий. Выполняем работы быстро, аккуратно и с гарантией результата по доступной цене.
Механизированная шпаклевка https://shpaklevka-msk.ru современный способ выравнивания стен и потолков. Ровное нанесение, высокая скорость работ и экономия материалов. Подготовка под финишную отделку с гарантией качества и соблюдением технологий.
Бытовая химия в Казани https://bytovayalavka.ru широкий ассортимент средств для уборки, стирки и ухода за домом. Оригинальная продукция, выгодные цены и быстрая доставка. Подберите качественные моющие средства для чистоты и комфорта вашего дома.
Calculate your horoscope http://www.ulduz-fali.com.az online. Horoscopes, love compatibility, daily horoscopes and astrological interpretations by date of birth on one site.
Dream Interpretations 2026 https://yuxu-yozmalari.com.az/ learn the meaning of your dreams with AI artificial intelligence. Dream interpretation from A to Z, folk belief interpretation, psychological approach. Free online dream interpretation.
Жіночий сайт https://zhinka.in.ua поради про красу, здоров’я, стосунки та стиль життя. Читайте корисні статті, лайфхаки, рецепти догляду та натхнення для сучасних жінок. Все про жіночу гармонію, саморозвиток і комфорт у повсякденному житті.
Сайт міста Вінниця https://faine-misto.vinnica.ua новини, події, довідник компаній і корисна інформація для жителів та гостей. Актуальні новини, афіша, транспорт, послуги і все про життя міста в одному зручному онлайн-порталі.
An online numerology numerologiya com az profile analyzes your destiny, talents, and finances. Accurate calculations, number interpretation, and personalized recommendations will help you better understand yourself and choose the right direction in life.
Сайт міста Одеса https://faine-misto.od.ua новини, події, афіша, довідник компаній та корисна інформація. Дізнавайтесь актуальні новини, знаходьте послуги, заклади і маршрути. Все про життя Одеси для мешканців і гостей міста в одному місці.
Сайт міста Житомир https://faine-misto.zt.ua новини, події, афіша та довідник компаній. Актуальна інформація про життя міста, транспорт, послуги і заклади. Усе необхідне для мешканців і гостей Житомира в одному зручному онлайн-порталі.
Автомобільний портал https://avtogid.in.ua новини авто, огляди, тести та поради водіям. Дізнавайтесь про нові моделі, технології, ремонт і обслуговування. Все про автомобілі в одному місці для власників і автолюбителів.
Сайт міста Львів https://faine-misto.lviv.ua новини, події, афіша та довідник компаній. Актуальна інформація про життя міста, транспорт, послуги і заклади. Усе необхідне для мешканців і туристів Львова в одному зручному онлайн-порталі.
Блог Києва https://infosite.kyiv.ua події, новини, цікаві місця та корисні поради для мешканців і гостей столиці. Дізнавайтесь про актуальні заходи, життя міста, розваги та сервіси. Все найцікавіше про Київ в одному зручному онлайн-блозі.
Сайт Полтави https://u-misti.poltava.ua новини, події, афіша та довідник компаній міста. Актуальна інформація про життя, транспорт, послуги і заклади. Усе необхідне для мешканців і гостей Полтави в одному зручному онлайн-порталі.
У місті Одеса https://u-misti.odesa.ua актуальні новини, події, афіша та корисна інформація для мешканців і гостей. Дізнавайтесь про життя міста, транспорт, заклади і послуги. Все найважливіше про Одесу в одному зручному онлайн-порталі.
Хмельницький онлайн https://u-misti.khmelnytskyi.ua міський портал з новинами, афішею та довідником. Дізнавайтесь про події, транспорт, бізнес і послуги. Усе для комфортного життя та відпочинку в Хмельницькому в одному місці.
Житомир онлайн https://u-misti.zhitomir.ua міський портал з новинами, афішею та довідником. Дізнавайтесь про події, транспорт, бізнес і послуги. Усе для комфортного життя та відпочинку в Житомирі в одному місці.
У місті Львів https://u-misti.lviv.ua актуальні новини, події, афіша та корисна інформація для мешканців і гостей. Дізнавайтесь про життя міста, транспорт, заклади і послуги. Все найважливіше про Львів в одному зручному онлайн-порталі.
Київ онлайн https://u-misti.kyiv.ua міський портал з новинами, афішею та довідником. Дізнавайтесь про події, транспорт, бізнес і послуги. Усе для комфортного життя та відпочинку в Києві в одному місці.
Міський сайт Дніпра https://u-misti.dp.ua новини, події, оголошення і довідник організацій. Зручний пошук послуг, закладів і маршрутів. Будьте в курсі життя міста та знаходьте потрібну інформацію швидко.
У місті Вінниця https://u-misti.vinnica.ua новини, афіша заходів, довідник закладів і корисні сервіси. Дізнавайтесь про події, відкривайте нові місця і плануйте свій час у Вінниці легко та зручно.
Сайт Чернівців https://u-misti.chernivtsi.ua новини, події, афіша та довідник компаній міста. Актуальна інформація про життя, транспорт, послуги і заклади. Усе необхідне для мешканців і гостей Чернівців в одному зручному онлайн-порталі.
Міський сайт Черкас https://u-misti.cherkasy.ua новини, події, оголошення і довідник організацій. Зручний пошук послуг, закладів і маршрутів. Будьте в курсі життя міста та знаходьте потрібну інформацію швидко.
Где можно познакомиться https://datenow.ru в России в 2026 году? Приложения для знакомств стали главным инструментом для миллионов. Но важно выбрать те, где реально можно найти человека для отношений. Не просто лайки, а искренний интерес. Разбираем, какие сервисы работают в этом году. Честно. Без рекламы. Только для тех, кто ищет всерьёз.
Подробности по ссылке: https://novostroi-tour.ru
Только лучшие материалы: https://domdipnera.ru
Расширенная статья здесь: https://sochibuilders.ru
ремонт интерьер дизайн квартир дизайн интерьера квартиры
дизайн интерьера квартир санкт петербург заказать дизайнера интерьера
дизайн проект ремонта квартиры студия дизайна интерьера санкт петербург
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
ТОП лучших МФО https://mfo-finance.github.io проверенные компании с высоким уровнем одобрения займов. Актуальные предложения, прозрачные условия, быстрые выплаты и онлайн оформление. Сравнивайте и выбирайте надежные МФО для получения денег.
Are you into rafting? white water rafting in montenegro exciting rafting trips down mountain rivers with experienced instructors. A tour of the Tara Canyon offers scenic routes, safety, and unforgettable experiences. Book a rafting tour and discover an active holiday.
dental problems? dental tourism high-quality dental treatment abroad at affordable prices. Implants, veneers, prosthetics, and treatments with a guarantee. We select a clinic, organize your trip, and provide patient support throughout the entire process.
Zahnprobleme? zahnbehandlung im ausland kosten zahnbehandlung im Ausland mit bis zu 70 % Ersparnis. Implantate, Zahnersatz, asthetische Zahnheilkunde und Diagnostik in modernen Kliniken. Wir unterstutzen Sie bei der Wahl des Landes und der Klinik und organisieren Ihre Reise von A bis Z.
Студия дизайна https://dill-design.ru интерьера в Санкт-Петербурге. Реализовываем проекты в г. Санкт-Петербург и г. Москва. Более 100 довольных заказчиков доверили нам создание своего интерьера. От разработки дизайн проекта до его качественной реализации. Авторский надзор на всех этапах реализации. Комплектация в подарок. Закажите расчет дизайн-проекта
Обзор путешествий https://tfast.ru и экскурсий. Ваш персональный гид в мире путешествий. Мы собираем самые живые обзоры, проверенные маршруты и уникальные экскурсии — от известных достопримечательностей до скрытых мест, о которых знают только местные. Планируйте свои приключения с нами, вдохновляйтесь и открывайте мир по-новому.
значок металлический купить изготовление металлических значков на заказ москва
значки металлические флаги https://metal-pin.ru
значки на одежду металлические печать на металлических значках
значок металлический купить изготовил металлических значков москва
металлический значок пин заказ значков из металла со своим дизайном москва
I apologise, but, in my opinion, you commit an error. Let’s discuss. Write to me in PM, we will communicate.
_ _ _ _ _ _ _ _
fuengirola car rental
металлические значки на заказ изготовление металлических значков по заказу
значок металлический цена изготовление штампованных и металлических значков
лак после циклевки паркета паркет циклевка метр цена
циклевка паркета под ключ цена циклевка паркета в спб недорого
Старый паркет? шлифовка паркета в спб профессиональное восстановление деревянного пола без пыли и лишних затрат. Удаляем царапины, потемнения и старое покрытие, возвращаем гладкость и естественный цвет. Используем современное оборудование, выполняем циклевку, шлифовку и лакировку паркета под ключ с гарантией качества и точным соблюдением сроков.
explore official site for a premium gaming experience in estonia that fully complies with all local regulations and safety standards. the site features a clean and modern design, making it easy to find your favorite titles from a diverse library of certified casino games. they offer very efficient withdrawal methods, which is vital for players who want to receive their winnings quickly and without any hassle.
Only top materials: https://www.janbasktraining.com/community/user_topics/14854
Daily Summary: https://zaraherbal.com/homemade-pornography-movies-on-the-better-pornography-pipe/
All the Details: http://www.galvaqro.com.mx/2026/03/17/100-percent-free-set-of-bank-borrowing-relationship-repossession-conversion/
Recommended reading: https://klero.it/play-19300-totally-free-slot-game-no-install/
Top Stories: https://monograficos.escuelaartegranada.com/mariamarquezarias/2026/03/14/whos-hiral-radadiya-bio-decades-spouse-family-members-and-you-will-movies/
Expand at the link: https://www.ccis.org.tn/indian-jabardasty-pornography-movies-finest-mature-2026/
Learn more here: https://idealmed.com.pl/blog/aktualnosci/2500-welcome-gambling-establishment-incentive/
Full version of the article: https://www.pakarbot.com/melhores-cassinos-online-esfogiteado-brasil-2025-top-15-opcoes/
Санитарные системы https://bio-ecopro.ru для мероприятий и стройплощадок — аренда мобильных туалетов, умывальников и санитарных модулей. Доставка, обслуживание и вывоз. Надежные решения для фестивалей, концертов, стройки и массовых событий.
Проверенные адвокаты Москвы https://isk1.ru квалифицированная юридическая помощь и защита в суде. Решение сложных правовых споров, сопровождение дел и профессиональный подход к каждому клиенту для достижения результата.
Менопауза и перименопауза https://menopower.ru симптомы, приливы и гормональные изменения. Полезные советы для женщин 45+, рекомендации по здоровью, образу жизни и управлению финансами для комфортного прохождения этого периода.
Компания DARKLUM https://darklum.ru/catalogue предлагает широкий ассортимент светодиодных светильников различного назначения для коммерческих и жилых помещений как внутреннего, так и уличного освещения. В каталоге представлено более 5 000 моделей различных форм-факторов, среди которых Вы без труда сможете выбрать оптимальный вариант.
Промокод Пятёрочка доставка http://reporter63.ru/content/view/785017/promokod-pyaterochka-dostavka-vygodnye-vozmozhnosti-dlya-pokupok-onlajn актуальные скидки и купоны на заказ продуктов онлайн. Получайте выгодные предложения, снижайте стоимость доставки и экономьте на покупках в Пятёрочке с рабочими промокодами.
PUPIL OF FATE MOTORS https://auto.ae/pupiloffatemotors автосалон премиум авто в Дубае. Продажа роскошных автомобилей, эксклюзивные модели и индивидуальный подбор. Помогаем выбрать, оформить и доставить авто с гарантией качества и высоким уровнем сервиса.
Эко-бытовая химия http://reporter63.ru/content/view/784903/himiya-dlya-uborki-sekrety-effektivnosti-i-bezopasnosti в Санкт-Петербурге — средства для уборки без вредных компонентов. Эффективная очистка, безопасность для здоровья и окружающей среды. Широкий ассортимент и доставка по городу.
Главные новости: https://lotos-vrn.ru/belevoj-trikotazh/
Modern earth fault indicator monitor the condition of electrical networks and protect equipment. They offer rapid fault detection, high accuracy, and reliability for industrial applications.
Between us speaking, I would address for the help in search engines.
_ _ _ _ _ _ _ _
best car hire lisbon https://drivelity-portugal.com
Купить стройматериалы https://stroyrostov161.ru в Ростове-на-Дону: широкий выбор сыпучих и строительных материалов, включая щебень, песок, цемент, штукатурку и шпатлевку. Быстрая доставка и доступные цены для вашего объекта.
Заборы под ключ https://dachnie-zabory.ru в Москве и области — изготовление и установка ограждений для дома и участка. Профнастил, штакетник, сетка рабица и 3D заборы. Замер, доставка и монтаж с гарантией качества и соблюдением сроков.
References:
Peoria casino
References:
https://www.tikosatis.com/index.php?page=user&action=pub_profile&id=563598
References:
Steroid side effect
References:
https://free-songs.de/blog-news/index.php/;focus=ALFAHO_com_cm4all_wdn_Flatpress_1587235&path=&frame=?x=entry:entry251123-105508%3Bcomments:1
Самое полезное для вас: услуги шлифовка паркета
Только что опубликовано: https://tsiklevka-parketa.ru
Читать далее: услуги шлифовка паркета
Последние обновления: циклевка паркета без пыли
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Промокоды Пятёрочки https://www.time-samara.ru/content/view/785106/transformaciya-sistemy-loyalnosti-v-sovremennom-rossijskom-ritejle актуальные купоны и скидки на продукты и доставку. Получайте бонусы, снижайте стоимость заказов и экономьте на покупках. Только проверенные промокоды для выгодных покупок в Пятёрочке.
Самые актуальный новости свежие новости — свежие события, аналитика и репортажи. Политика, экономика, технологии и общество. Будьте в курсе последних новостей и ключевых событий каждый день.
Читать больше на сайте: https://geforce-gt-730.ru
Посмотреть на сайте: https://interskol-shurupovert.ru
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me? https://www.binance.info/ar/register?ref=PORL8W0Z
Элитная парфюмерия может стать отличным подарком для близких людей. В интернет магазине легко найти подходящий вариант, https://avon-forum.ru/
Подарки ручной работы с ароматами лаванды, ванили или цитрусов помогают создать спокойную и уютную атмосферу. Они могут стать отличным дополнением интерьера и приятным сюрпризом для близких людей. Подробнее по ссылке https://aroma-lavka.ru/
Если использовать фасадные дюбели по назначению, можно получить прочное соединение, удобную установку и понятный результат в работе Это удобно для регулярных поставок и серийной сборки – забивные анкеры оптом
Nowy sufit napinany poprawia wygląd całej przestrzeni. To rozwiązanie pomaga osiągnąć schludny i dopracowany wygląd. Coraz częściej wybierane są proste minimalistyczne formy, przez co aranżacja staje się bardziej spójna https://sufity-napinane-wroclaw.pl/
Элитная парфюмерия создается из качественных ингредиентов и отличается высокой стойкостью. В интернет магазине можно найти ароматы для любого сезона и настроения – https://avon-forum.ru/
balloon bahis oyunu
Проверка авто по VIN https://dtf.ru/luchshii-rating/3585176-top-15-luchshih-servisov-proverki-avto-po-vin-nomeru-reiting-2025-goda ТОП-15 лучших сервисов для анализа истории машины. ДТП, пробег, владельцы и ограничения. Сравните платформы и выберите надежный сервис для безопасной покупки авто.
Промокоды Пятёрочки https://www.time-samara.ru/content/view/785106/transformaciya-sistemy-loyalnosti-v-sovremennom-rossijskom-ritejle актуальные купоны и скидки на продукты и доставку. Получайте бонусы, снижайте стоимость заказов и экономьте на покупках. Только проверенные промокоды для выгодных покупок в Пятёрочке каждый день.
check here
Kent Casino https://kentcasino.ru.com официальный сайт, регистрация и бонусы. Онлайн казино с быстрым выводом средств, слотами и играми от топ провайдеров. Получите фриспины и играйте на реальные деньги безопасно.
jetton ставки
Интернет магазин элитной парфюмерии предлагает оригинальные композиции с насыщенными и стойкими ароматами. Это отличный выбор для ценителей качества: https://avon-forum.ru/
buy saxenda
Накрутка поведенческих факторов может помочь увеличить активность пользователей и улучшить видимость сайта. Вся информация по ссылке: накрутка пф ботами
diazepam prescription
казино джеттон официальный сайт
diva london escort
дивитись фільми 2026 дивитися фільми онлайн безкоштовно без реєстрації
как включить и разрешить доступ к usb пошаговая инструкция
быстрый микрокредит на карту
jeton скачать
казино кирки
https://bg.dobrblog.com/
наркологический центр наркологический центр .
References:
Anadrol steroid pills
References:
http://www.aionesight.com/nicholasrasco5
References:
Buy steroids online uk
References:
http://119.45.160.240:3000/consuelowaldru
платформа jetton
https://molitvy.guru/
джетон
вывод из запоя на дому вывод из запоя на дому .
Really enjoyed this outlook. It applies so well to hair care too, where even a curly routine can change depending on the oil, shampoo, conditioner, salon advice, natural ingredients, and the right treatment.
youtube скачать видео skachat-video-s-youtube-1.ru .
https://molitvy.guru/
small office for lease https://offices-rent-nyc.com
Профессиональная: оклейка полиуретановой пленкой автомобиля – сохраните родное лакокрасочное покрытие в идеальном состоянии на долгие годы.
скачать видео ютуб на пк skachat-video-s-youtube-1.ru .
Накрутка поведенческих факторов используется для увеличения активности пользователей. Это может повлиять на ранжирование сайта. Подробнее по ссылке: поведенческие факторы заказать
нарколог на дом нарколог на дом .
https://mine-drop1.com/
скачать видио с ютуб скачать видио с ютуб .
References:
Anabolicsteroids com
References:
https://yours-tube.com/@cheriesupple95?page=about
Многие SEO специалисты уделяют внимание поведенческим метрикам. Они помогают понять, насколько сайт удобен и полезен для аудитории. Улучшение этих показателей может привести к росту позиций. Подробности по ссылке – сервис накрутки пф
скачать видео с ютуба на смартфон skachat-video-s-youtube-1.ru .
Проверенный магазин масло оптом дешево продаёт моторное масло оптом с документами и гарантией качества.
References:
Where to buy anabolic steroids online forum
References:
http://45.144.30.78:8083/dalenenicolay/7788musixx.smart-und-nett.de/wiki/Dianabol-Inj-50
наркологический стационар vyvod-iz-zapoya-na-domu-samara-3.ru .
Накрутка поведенческих факторов используется как инструмент повышения активности на сайте. Увеличение числа переходов и времени просмотра может повлиять на ранжирование – монстро накрутка пф
скачать видео с ютуба на смартфон skachat-video-s-youtube-2.ru .
кирка майнкрафт казик
загрузчик видео с ютуба загрузчик видео с ютуба .
https://mine-drop1.com/
скачать видео из ютуба онлайн скачать видео из ютуба онлайн .
скачать видео с ютуба скачать видео с ютуба .
где купить капли ястреб yastreb-kapli.ru .
лечение наркомании vyvod-iz-zapoya-na-domu-ekaterinburg.ru .
лечение наркомании лечение наркомании .
наркологический центр наркологический центр .
наркологический стационар kapelnica-ot-zapoya-nizhnij-novgorod.ru .
реабилитация наркоманов vyvod-iz-zapoya-na-domu-ekaterinburg-1.ru .
наркологическая клиника наркологическая клиника .
лечение алкоголизма лечение алкоголизма .
кодирование от алкоголизма кодирование от алкоголизма .
скачать видео с ютуба на смартфон skachat-video-s-youtube-1.ru .
Улучшить качество фото нейросетью https://vc.ru/aihub/2842519-uluchshenie-kachestva-foto-neirosyatey
скачать видео с юту скачать видео с юту .
нарколог на дом нарколог на дом .
скачать ролик с ютьюб скачать ролик с ютьюб .
купить капли ястреб yastreb-kapli.ru .
как улучшить фото на айфоне 16 https://vc.ru/aihub/2842519-uluchshenie-kachestva-foto-neirosyatey
кодирование от алкоголизма vyvod-iz-zapoya-na-domu-ekaterinburg.ru .
наркологический стационар vyvod-iz-zapoya-na-domu-nizhnij-novgorod-1.ru .
лечение наркомании vyvod-iz-zapoya-na-domu-nizhnij-novgorod.ru .
реабилитационный центр от алкоголизма kapelnica-ot-zapoya-nizhnij-novgorod.ru .
реабилитационный центр от алкоголизма kapelnica-ot-zapoya-nizhnij-novgorod-1.ru .
капельница от похмелья vyvod-iz-zapoya-na-domu-ekaterinburg-2.ru .
лечение алкоголизма лечение алкоголизма .
pinup казино https://global-smm.ru
пин ап рабочее зеркало пин ап казино вход
игровые автоматы пин ап пин ап игровые автоматы
промт на день рождения женщине https://vc.ru/aihub/2842593-prompty-dlya-pozdravleniy-neyrosetyu
игровые автоматы пин ап пинап официальный сайт казино
пин ап казино вход https://pinup-casinos.ru
пин ап скачать pin up зеркало
pinup bet https://севсклон.рф
казино пин-ап пин ап официальный сайт казино
реабилитационный центр от алкоголизма vyvod-iz-zapoya-na-domu-voronezh-8.ru .
где купить капли ястреб yastreb-kapli.ru .
лечение наркомании vyvod-iz-zapoya-na-domu-nizhnij-novgorod.ru .
наркологическая помощь наркологическая помощь .
лечение алкоголизма лечение алкоголизма .
лечение алкоголизма лечение алкоголизма .
наркологическая помощь наркологическая помощь .
кодирование от алкоголизма кодирование от алкоголизма .
Оживить фото нейросетью — главная. Посмотрите информацию по ссылке – оживить фото в видео 18
Генерация изображений нейросетью — главная
Подробности доступны по ссылке – генерация изображений обучение
Volvo спецтехніка купити спецтехніку екскаватори, фронтальні навантажувачі та дорожні машини. Надійність, ефективність і сучасні рішення для будівництва. Продаж, підбір і обслуговування техніки для бізнесу.
капельница от запоя vyvod-iz-zapoya-na-domu-voronezh-8.ru .
наркологический стационар vyvod-iz-zapoya-na-domu-ekaterinburg-3.ru .
наркологический центр наркологический центр .
https://compact-houses.ru/
скачать с ютуба в отличном качестве скачать с ютуба в отличном качестве .
кодирование от алкоголизма кодирование от алкоголизма .
реабилитационный центр от алкоголизма vyvod-iz-zapoya-na-domu-voronezh-9.ru .
наркологический стационар vyvod-iz-zapoya-na-domu-ekaterinburg.ru .
наркологический стационар kapelnica-ot-zapoya-nizhnij-novgorod.ru .
капельница от похмелья kapelnica-ot-zapoya-nizhnij-novgorod-1.ru .
наркологическая клиника наркологическая клиника .
наркологическая помощь наркологическая помощь .
нарколог на дом нарколог на дом .
реабилитационный центр для наркозависимых реабилитационный центр для наркозависимых .
лечение наркомании vyvod-iz-zapoya-na-domu-samara-9.ru .
Midjourney — что это и как использовать. Ознакомьтесь с сервисом подробнее – midjourney генерация изображения
лечение алкоголизма лечение алкоголизма .
References:
Weight lifting steroids
References:
https://sisinetjobs.com/employer/testim-50-mg-5-gram-1-transdermal-gel-kaiser-permanente/
References:
Do female bodybuilders use steroids
References:
https://gitea.diputadosalta.gob.ar/michelinestuar
смотреть новинки кино фильмы смотреть онлайн бесплатно
https://compact-houses.ru/
References:
Maximum shred gnc
References:
https://camtalking.com/@janemonte55804
стабилизаторы энергия https://stabilizatory-energiya.ru/
вывод из запоя в стационаре vyvod-iz-zapoya-na-domu-samara-8.ru .
References:
Steroid transformation 3 months
References:
https://teanurture.online/the-mediterranean-diet-hack-that-boosts-testosterone-naturally/
наркологический стационар vyvod-iz-zapoya-na-domu-ekaterinburg-3.ru .
Хочешь путешествовать? тур в пушкинские горы из спб интересные маршруты, экскурсии и комфортный отдых для путешествий и новых впечатлений. Мы поможем подобрать идеальный тур — под любые пожелания и бюджет! Работаем ежедневно с 9:00 до 21:00 — без выходных!
наркологический стационар vyvod-iz-zapoya-na-domu-voronezh-10.ru .
реабилитационный центр от алкоголизма vyvod-iz-zapoya-na-domu-samara-9.ru .
реабилитационный центр от алкоголизма vyvod-iz-zapoya-na-domu-voronezh-8.ru .
реабилитационный центр от алкоголизма vyvod-iz-zapoya-na-domu-voronezh-11.ru .
скачать видио с ютуб скачать видио с ютуб .
реабилитация наркоманов vyvod-iz-zapoya-na-domu-voronezh-9.ru .
References:
Steroids before after
References:
http://wooriwebs.com/bbs/board.php?bo_table=faq
Volvo в Україні https://volvo-2026.carrd.co/ екскаватори, фронтальні навантажувачі та дорожні машини. Надійність, ефективність і сучасні рішення для будівництва. Продаж, підбір і обслуговування техніки для бізнесу.
наркологическая клиника наркологическая клиника .
наркологическая клиника наркологическая клиника .
реабилитация алкоголиков vyvod-iz-zapoya-na-domu-samara-9.ru .
капельница от похмелья vyvod-iz-zapoya-na-domu-voronezh-10.ru .
вывод из запоя на дому вывод из запоя на дому .
Профессиональная: оклейка полиуретановой пленкой автомобиля – сохраните родное лакокрасочное покрытие в идеальном состоянии на долгие годы.
ии бот тг https://vc.ru/aihub/2842563-neyroseti-v-telegram-luchshie-boty-2026-goda
вывод из запоя на дому вывод из запоя на дому .
нарколог на дом нарколог на дом .
наркологическая помощь наркологическая помощь .
наркологический стационар vyvod-iz-zapoya-na-domu-voronezh-10.ru .
наркологическая клиника наркологическая клиника .
реабилитационный центр от алкоголизма vyvod-iz-zapoya-na-domu-voronezh-11.ru .
https://compact-houses.ru/
Можно ознакомиться подробнее по ссылке: нейросеть для баннера
лечение алкоголизма лечение алкоголизма .
наркологический стационар vyvod-iz-zapoya-na-domu-samara-11.ru .
наркологический стационар vyvod-iz-zapoya-na-domu-nizhnij-novgorod-6.ru .
наркологическая клиника наркологическая клиника .
нарколог на дом нарколог на дом .
кодирование от алкоголизма кодирование от алкоголизма .
наркологическая клиника наркологическая клиника .
лечение наркомании лечение наркомании .
капельница от похмелья vyvod-iz-zapoya-na-domu-nizhnij-novgorod-6.ru .
вывод из запоя в стационаре vyvod-iz-zapoya-na-domu-nizhnij-novgorod-4.ru .
Regards! Numerous posts.
References:
https://topsitenet.com/profile/heliumjason2/1581342/
лечение алкоголизма лечение алкоголизма .
реабилитационный центр для наркозависимых реабилитационный центр для наркозависимых .
наркологическая клиника наркологическая клиника .
реабилитация алкоголиков vyvod-iz-zapoya-na-domu-nizhnij-novgorod-4.ru .
капельница от запоя капельница от запоя .
вывод из запоя на дому вывод из запоя на дому .
лечение наркомании лечение наркомании .
реабилитация алкоголиков vyvod-iz-zapoya-v-staczionare-sankt-peterburg-1.ru .
наркологический стационар vyvod-iz-zapoya-v-staczionare-sankt-peterburg.ru .
реабилитационный центр от алкоголизма vyvod-iz-zapoya-v-staczionare-sankt-peterburg-2.ru .
онлайн школы для подготовки к егэ shkola-onlajn-43.ru .
наркологический центр наркологический центр .
наркологический центр наркологический центр .
реабилитация алкоголиков реабилитация алкоголиков .
капельница от запоя капельница от запоя .
школа дистанционного образования школа дистанционного образования .
капельница от похмелья vyvod-iz-zapoya-v-staczionare-sankt-peterburg.ru .
наркологический центр наркологический центр .
наркологическая помощь наркологическая помощь .
школа онлайн в россии shkola-onlajn-43.ru .
реабилитационный центр от алкоголизма vyvod-iz-zapoya-na-domu-nizhnij-novgorod-5.ru .
References:
Instant Casino Freispiele
References:
https://skitterphoto.com/photographers/2540636/blanton-brooks
вывод из запоя в стационаре вывод из запоя в стационаре .
лечение алкоголизма лечение алкоголизма .
References:
Instant Casino Login vergessen
References:
https://king-bookmark.stream/story.php?title=willkommensbonus-200-
наркологический стационар vyvod-iz-zapoya-v-staczionare-sankt-peterburg-2.ru .
наркологический центр наркологический центр .
онлайн-школа для детей онлайн-школа для детей .
наркологическая клиника наркологическая клиника .
References:
Instant Casino mit Trustly
References:
https://www.investagrams.com/Profile/dohert3542294
онлайн школы для детей онлайн школы для детей .
капельница от похмелья vyvod-iz-zapoya-na-domu-nizhnij-novgorod-7.ru .
наркологическая помощь наркологическая помощь .
References:
Instant Casino App
References:
https://www.tikosatis.com/index.php?page=user&action=pub_profile&id=563598
наркологический стационар vyvod-iz-zapoya-na-domu-nizhnij-novgorod-5.ru .
реабилитационный центр от алкоголизма vyvod-iz-zapoya-v-staczionare-sankt-peterburg-2.ru .
вывод из запоя в стационаре vyvod-iz-zapoya-v-staczionare-sankt-peterburg.ru .
онлайн обучение школа онлайн обучение школа .
наркологическая помощь наркологическая помощь .
нарколог на дом нарколог на дом .
школа дистанционного обучения москва shkola-onlajn-43.ru .
онлайн обучение школа онлайн обучение школа .
капельница от запоя narkolog-na-dom-moskva-1.ru .
реабилитация алкоголиков narkolog-na-dom-moskva-2.ru .
наркологический центр наркологический центр .
Excuse, it is removed
_ _ _ _ _ _ _ _
https://automietenmallorca.de
References:
Instant Casino
References:
https://sibze.ru/index.php?subaction=userinfo&user=flagguilty7
References:
Instant Casino Login vergessen
References:
https://medibang.com/author/28050247/
Онлайн школа Онлайн школа .
лечение наркомании narkolog-na-dom-moskva-1.ru .
Капсульные дома — это современный подход к загородному жилью. Пространство используется максимально эффективно. Дом быстро устанавливается и не требует долгого строительства. Внутри комфортно жить. Очень понравился результат: космический капсульный дом
наркологический центр наркологический центр .
среднее образование онлайн среднее образование онлайн .
наркологический центр наркологический центр .
наркологический стационар narkolog-na-dom-moskva-2.ru .
Нужны заклепки? вытяжная резьбовая заклепка прочный крепеж для соединения деталей. Алюминиевые, стальные и нержавеющие варианты. Надежность, долговечность и удобство монтажа для различных задач и конструкций.
кодирование от алкоголизма кодирование от алкоголизма .
интернет-школа интернет-школа .
лечение алкоголизма лечение алкоголизма .
мебельный паралон мебельный паралон .
купить плотный поролон porolon-dlya-divana-2.ru .
лист поролона цена лист поролона цена .
реабилитационный центр для наркозависимых narkolog-na-dom-moskva-2.ru .
вывод из запоя в стационаре narkolog-na-dom-moskva-1.ru .
online school online school .
вывод из запоя в стационаре вывод из запоя в стационаре .
реабилитационный центр от алкоголизма narkolog-na-dom-moskva-4.ru .
поролон купить москва поролон купить москва .
паралон или поролон porolon-dlya-divana-2.ru .
где купить поролон в москве porolon-dlya-divana-3.ru .
Любишь путешествовать? турфирмы в санкт петербурге официальные предлагаем экскурсионные туры по России и Грузии по ценам официальных операторов — с гарантией и страховкой. Мы поможем подобрать идеальный тур — под любые пожелания и бюджет! Работаем ежедневно с 9:00 до 21:00 — без выходных!
вывод из запоя в стационаре вывод из запоя в стационаре .
Stackshine AI-Platform a SaaS cost management platform: subscription control, usage transparency, renewal tracking, and employee offboarding. Optimize your budget and reduce unnecessary software costs.
дистанционное обучение в москве shkola-onlajn-41.ru .
наркологическая помощь наркологическая помощь .
онлайн школа цена shkola-onlajn-42.ru .
мебельный поролон купить москва мебельный поролон купить москва .
поролон для мебели цена поролон для мебели цена .
наркологическая помощь наркологическая помощь .
поролон для мебели цена поролон для мебели цена .
Установка капсульного дома занимает минимум времени, при этом результат полностью соответствует ожиданиям – капсульные дома в россии
капельница от похмелья narkolog-na-dom-moskva-4.ru .
школа 2 класс школа 2 класс .
поролон москва поролон москва .
купить поролон для кровати купить поролон для кровати .
онлайн школа 1 онлайн школа 1 .
купить ппу для дивана купить ппу для дивана .
Капсульные дома идеально подходят для временного проживания или использования в качестве гостевого домика: купить капсульную кофеварку для дома недорого
References:
Do all bodybuilders use steroids
References:
https://doc.adminforge.de/s/0vEcBt_WB2
стоимость дистанционного обучения shkola-onlajn-41.ru .
онлайн школа 3 класс shkola-onlajn-42.ru .
курсовая работа купить курсовая работа купить .
References:
Liquid anadrol dosage
References:
https://hackmd.okfn.de/s/rygNbQzYrWg
курсовые работы заказать kupit-kursovuyu-101.ru .
реабилитационный центр для наркозависимых реабилитационный центр для наркозависимых .
наркологический стационар vyvod-iz-zapoya-na-domu-samara-16.ru .
наркологическая клиника наркологическая клиника .
лечение наркомании лечение наркомании .
написание курсовой работы на заказ цена kupit-kursovuyu-102.ru .
домашняя школа shkola-onlajn-41.ru .
Появились вредители? уничтожение клопов в квартире в москве обработка помещений от вирусов, бактерий и насекомых. Современные методы, безопасные средства и опытные специалисты для надежной защиты.
Уничтожение вредителей https://dezinfekciya-mcd.ru/ уничтожение бактерий, вирусов и насекомых. Обработка квартир, домов и коммерческих помещений. Безопасные препараты, опытные специалисты и гарантия результата.
цена курсовой работы kupit-kursovuyu-101.ru .
кодирование от алкоголизма vyvod-iz-zapoya-na-domu-samara-16.ru .
купить курсовую москва купить курсовую москва .
кодирование от алкоголизма кодирование от алкоголизма .
онлайн школа для детей shkola-onlajn-42.ru .
реабилитация наркоманов vyvod-iz-zapoya-na-domu-samara-18.ru .
купить курсовая работа купить курсовая работа .
срочно курсовая работа срочно курсовая работа .
реабилитация наркоманов vyvod-iz-zapoya-na-domu-samara-17.ru .
Эта статья сочетает познавательный и занимательный контент, что делает ее идеальной для любителей глубоких исследований. Мы рассмотрим увлекательные аспекты различных тем и предоставим вам новые знания, которые могут оказаться полезными в будущем.
Детальнее – https://vivod-iz-zapoya-2.ru/
написание учебных работ kupit-kursovuyu-106.ru .
заказать практическую работу недорого цены kupit-kursovuyu-102.ru .
купить курсовую работу купить курсовую работу .
Free online games https://www.poki.com.az play without downloading or registering. A large collection of games across various genres: action, puzzles, racing, and strategy. Easily access from any device.
Arizona sports news oxu-az football, transfers, and match results in real time. Breaking news, analysis, and reviews. Follow the teams and stay up-to-date with all the state’s sports news.
сайт для заказа курсовых работ сайт для заказа курсовых работ .
выполнение курсовых работ выполнение курсовых работ .
References:
What type of drugs are steroids
References:
http://www.thehispanicamerican.com/companies/anavar-50-1-trusted-source-for-bodybuilding-reviews-lab-tests-2025muscleguru/
кодирование от алкоголизма vyvod-iz-zapoya-na-domu-samara-16.ru .
сколько стоит сделать курсовую работу на заказ kupit-kursovuyu-108.ru .
сколько стоит курсовая работа по юриспруденции kupit-kursovuyu-106.ru .
Arizona sports events https://oxu-az.com.az/ football, transfers, and live match results. Latest news, statistics, and reviews for fans and sports enthusiasts.
кодирование от алкоголизма кодирование от алкоголизма .
помощь в написании курсовой помощь в написании курсовой .
курсовые работы заказать курсовые работы заказать .
вывод из запоя в стационаре вывод из запоя в стационаре .
Free online games https://1001-oyun.com.az/ the best browser games with no installation required. Huge selection of genres, easy search, and quick launch. Play anytime for free.
заказать практическую работу недорого цены kupit-kursovuyu-103.ru .
написание курсовых на заказ написание курсовых на заказ .
References:
Crazy mass cutting stack reviews
References:
https://yona.archivonacional.go.cr/blog/index.php?entryid=18887
реабилитация наркоманов vyvod-iz-zapoya-na-domu-samara-17.ru .
Roblox Download delta-roblox.com.az Download the game, learn about Roblox Studio features, and learn about security settings. Play, create your own worlds, and protect your account. A complete guide to installing, playing, and using the platform safely.
курсовая заказ купить kupit-kursovuyu-106.ru .
Выгодно купить кварцевый песок для пескоструя – 100% очистка без забитых сопел! Забудьте о засорах: очищайте металл в разы быстрее. Ваш аппарат скажет спасибо, а результат поразит клиента. Купить кварцевый песок!
курсовая заказ купить курсовая заказ купить .
реабилитация наркоманов vyvod-iz-zapoya-na-domu-samara-16.ru .
курсовая заказ купить курсовая заказ купить .
вывод из запоя на дому вывод из запоя на дому .
купить курсовую москва купить курсовую москва .
вывод из запоя на дому вывод из запоя на дому .
сколько стоит курсовая работа по юриспруденции kupit-kursovuyu-107.ru .
срочно курсовая работа kupit-kursovuyu-108.ru .
реабилитационный центр для наркозависимых vyvod-iz-zapoya-na-domu-samara-17.ru .
курсовая работа купить курсовая работа купить .
заказать курсовую работу заказать курсовую работу .
курсовой проект цена kupit-kursovuyu-107.ru .
курсовая заказать курсовая заказать .
купить курсовую сайт kupit-kursovuyu-101.ru .
Explore trending k-pop playlist spotify playlists on Spotify updated weekly with the latest tracks and rising artists.
Нужен кондицинер https://atmosfera-profi-klimat.ru/services/montazh-konditsionerov/ профессиональный монтаж сплит-систем под ключ. Быстро, аккуратно и с гарантией. Подбор оборудования, установка и настройка с соблюдением всех норм и стандартов.
Обзор червячных хомутов https://teletype.in/@da_revanta/sMB0_AOMqxv как выбрать лучший вариант для надежного крепления. Сравнение материалов, размеров и производителей. Полезные советы по выбору, установке и применению для разных задач.
нужен бот? https://botman.pro создавайте ботов для продаж и поддержки клиентов. Интеграции, сценарии, автоответы и аналитика. Простое решение для бизнеса без навыков программирования.
покупка курсовой покупка курсовой .
Your source https://365sportia.com for international sports coverage football transfer news, Champions League analysis, NBA and NFL updates, and sports collectibles insights
Latest scores https://rtahasports.com game highlights, and player news from the NFL, NBA, NHL, and MLB. Get up-to-date statistics, transfers, and analysis. Follow the games and learn everything about teams and players in real time.
курсовые под заказ курсовые под заказ .
наркологический центр наркологический центр .
Любишь музыку? радомир музыка с душой, тексты и композиции. Слушайте онлайн, открывайте новые треки и погружайтесь в атмосферу искреннего творчества.
Любишь музыку? песни двадцатого века музыка с душой, тексты и композиции. Слушайте онлайн, открывайте новые треки и погружайтесь в атмосферу искреннего творчества.
реабилитация алкоголиков vyvod-iz-zapoya-na-domu-sankt-peterburg-1.ru .
Любишь читать но нет времени? https://knijki.com огромный выбор жанров, удобный поиск и качественная озвучка. Наслаждайтесь любимыми произведениями в любое время.
Нужен займ? https://srochno-zaym-online.ru оформление онлайн без справок и поручителей. Быстрое решение, удобная подача заявки и получение денег на карту. Подберите выгодное предложение и получите средства в короткие сроки.
курсовые заказ курсовые заказ .
Товар или услуга? разместить объявление бесплатно публикуйте объявления и находите товары, услуги и вакансии. Удобный поиск, категории и быстрый доступ к актуальным предложениям.
наркологический стационар vyvod-iz-zapoya-na-domu-sankt-peterburg.ru .
Только свежие актуальные новости свежие новости политики, экономики, общества и технологий. Актуальные события, аналитика, обзоры и мнения экспертов. Следите за главными новостями страны и мира онлайн в удобном формате каждый день.
капельница от похмелья vyvod-iz-zapoya-na-domu-sankt-peterburg-3.ru .
лечение наркомании лечение наркомании .
наркологическая помощь наркологическая помощь .
лечение алкоголизма vyvod-iz-zapoya-na-domu-ekaterinburg-8.ru .
курсовая работа недорого курсовая работа недорого .
Строительные технологии https://universalstroi.su выгодные инвестиции в доступное жилье. Стабильный доход, перспективные проекты и высокий спрос. Получайте прибыль от инновационных решений в строительстве.
наркологический центр наркологический центр .
Монтажные работы https://montazhstroy.su услуги по установке инженерных систем и конструкций. Быстро, качественно и с гарантией. Выполняем задачи любой сложности для частных и коммерческих объектов.
курсовая работа купить курсовая работа купить .
ответственный за ведение и хранение сколько стоит ответственное хранение
реабилитация алкоголиков vyvod-iz-zapoya-na-domu-sankt-peterburg.ru .
реабилитационный центр для наркозависимых реабилитационный центр для наркозависимых .
капельница от запоя vyvod-iz-zapoya-na-domu-ekaterinburg-8.ru .
наркологический стационар vyvod-iz-zapoya-na-domu-ekaterinburg-9.ru .
капельница от запоя капельница от запоя .
заказать курсовую заказать курсовую .
наркологическая клиника наркологическая клиника .
реабилитация наркоманов vyvod-iz-zapoya-na-domu-sankt-peterburg.ru .
реабилитация наркоманов vyvod-iz-zapoya-na-domu-ekaterinburg-8.ru .
наркологический стационар vyvod-iz-zapoya-na-domu-sankt-peterburg-3.ru .
наркологический стационар vyvod-iz-zapoya-na-domu-ekaterinburg-9.ru .
наркологическая клиника наркологическая клиника .
лечение алкоголизма лечение алкоголизма .
наркологический стационар vyvod-iz-zapoya-na-domu-ekaterinburg-10.ru .
вывод из запоя на дому vyvod-iz-zapoya-na-domu-ekaterinburg-8.ru .
нарколог на дом нарколог на дом .
лечение алкоголизма лечение алкоголизма .
кодирование от алкоголизма кодирование от алкоголизма .
вывод из запоя на дому kapelnicza-ot-zapoya-voronezh.ru .
дизайн интерьер квартир под ключ заказать интерьер квартиры
капельница от запоя капельница от запоя .
нарколог на дом нарколог на дом .
наркологическая помощь наркологическая помощь .
Complete insomnia treatment guide — understand causes, manage symptoms, and explore solutions. From lifestyle changes to therapies, learn how to achieve deep, restful sleep and improve daily performance.
покупка базы данных покупка базы данных .
реабилитационный центр для наркозависимых vyvod-iz-zapoya-na-domu-ekaterinburg-10.ru .
дизайн интерьера спб заказать дизайн интерьера квартиры в москве
наркологическая клиника наркологическая клиника .
наркологический центр наркологический центр .
регистрация в selector gg
реабилитационный центр для наркозависимых kapelnicza-ot-zapoya-voronezh.ru .
капельница от похмелья kapelnicza-ot-pokhmelya-voronezh-1.ru .
Открываешь кейсы KC? промокод на easydrop актуальные бонусы и скидки для пользователей. Получайте выгодные предложения, дополнительные возможности и экономьте при использовании сервиса. Все действующие промокоды в одном месте.
реабилитация алкоголиков kapelnicza-ot-zapoya-voronezh-1.ru .
реабилитационный центр для наркозависимых vyvod-iz-zapoya-na-domu-ekaterinburg-10.ru .
базу данных купить базу данных купить .
кодирование от алкоголизма кодирование от алкоголизма .
реабилитация наркоманов реабилитация наркоманов .
Открываешь кейсы KC? easydrop promo актуальные бонусы и скидки для пользователей. Получайте выгодные предложения, дополнительные возможности и экономьте при использовании сервиса. Все действующие промокоды в одном месте.
наркологическая помощь наркологическая помощь .
купить базу купить базу .
Всё прошло именно так, как и должно быть в хорошем интернет магазине. Оформил заказ, получил подтверждение, дождался доставки без лишних проблем. Телефон новый, оригинальный, работает отлично. Надёжный продавец, которому можно доверять: магазины телефонов в москве
лечение наркомании лечение наркомании .
Мгновенные микрокредиты на https://credit-world.ru – это возможность получить деньги без лишних сложностей без лишних проверок и сложных условий. В каталоге доступно более 50 МФО, где можно получить деньги практически каждому. Изучите доступные варианты, выбрать оптимальные условия и подать заявку за несколько минут, и узнать результат в кратчайшие сроки.
наркологическая клиника наркологическая клиника .
капельница от запоя капельница от запоя .
наркологическая клиника наркологическая клиника .
вывод из запоя в стационаре kapelnicza-ot-zapoya-voronezh-1.ru .
покупка данных gobasego-2.ru .
нарколог на дом нарколог на дом .
Office for rent https://rentofficetoday.com/en/ business premises in business centers and commercial buildings. Compare office for rent, private office space for rent, and offices to rent in prime locations. Find the best office rental solutions and rent office space that fits your business needs
капельница от похмелья kapelnicza-ot-pokhmelya-voronezh-1.ru .
противопожарные двери https://dveri-ot-zavoda.ru с доставкой и профессиональной консультацией, посмотрите актуальные решения для разных типов помещений.
реабилитационный центр для наркозависимых kapelnicza-ot-zapoya-voronezh-1.ru .
1win skachat
реабилитация алкоголиков kapelnicza-ot-pokhmelya-ekaterinburg-1.ru .
реабилитационный центр для наркозависимых kapelnicza-ot-zapoya-kalyazin.ru .
кодирование от алкоголизма кодирование от алкоголизма .
сувенирка сувенирка .
наркологическая клиника наркологическая клиника .
корпоративные подарки москва suvenirnaya-produkcziya-s-logotipom.ru .
Сломалась машина? тягач помощь на дороге техпомощь на дорогах СПб и Ленобласти: эвакуация, подвоз топлива, запуск двигателя, вытаскивание авто — 24/7. Круглосуточная мобильная служба техпомощи в Санкт?Петербурге и Ленинградской области. Оказываем выездную помощь в любое время: эвакуируем авто, подвозим топливо, помогаем завести двигатель и вытаскиваем застрявшие машины.
корпоративные сувениры suvenirnaya-produkcziya-s-logotipom-1.ru .
Универсальный флагманский безбумажный регистратор jumo logoscreen 700 для контроля температуры, давления и других технологических параметров. Удобный интерфейс, точные измерения и возможность интеграции в системы мониторинга.
реабилитация алкоголиков kapelnicza-ot-pokhmelya-ekaterinburg-1.ru .
наркологическая помощь наркологическая помощь .
лечение наркомании kapelnicza-ot-zapoya-voronezh-1.ru .
сувениры с логотипом компании на заказ сувениры с логотипом компании на заказ .
реабилитационный центр для наркозависимых реабилитационный центр для наркозависимых .
корпоративные подарки с логотипом компании корпоративные подарки с логотипом компании .
капельница от запоя капельница от запоя .
подарки с логотипом подарки с логотипом .
купить сувенирную продукцию suvenirnaya-produkcziya-s-logotipom-1.ru .
Нужен промокод? https://prazdnikvrn.ru актуальные бонусы, скидки и акции для пользователей. Используйте рабочие коды, получайте дополнительные преимущества и экономьте при использовании сервиса. Все свежие предложения в одном месте.
реабилитационный центр для наркозависимых kapelnicza-ot-pokhmelya-ekaterinburg-1.ru .
вывод из запоя на дому вывод из запоя на дому .
креативные корпоративные подарки креативные корпоративные подарки .
изготовление корпоративных сувениров изготовление корпоративных сувениров .
лечение наркомании лечение наркомании .
Нужна брендированная продукция? https://2ymedia.kz/category/bloknoty-i-zapisnye-knizhki/ ваш надежный партнер в сфере брендинга в Алматы. Мы специализируемся на производстве сувенирной продукции с нанесением логотипа и корпоративной полиграфии. В нашем каталоге вы найдете всё для продвижения бренда: бизнес-сувениры, промо-мерч, текстиль и полиграфическую продукцию. Мы принимаем заказы оптом от 50 единиц, что делает нас доступными как для крупного бизнеса, так и для небольших компаний.
корпоративные подарки санкт петербург suvenirnaya-produkcziya-s-logotipom.ru .
реабилитация алкоголиков kapelnicza-ot-pokhmelya-ekaterinburg-1.ru .
кодирование от алкоголизма кодирование от алкоголизма .
реабилитационный центр от алкоголизма kapelnicza-ot-pokhmelya-ekaterinburg.ru .
корпоративные сувениры с логотипом suvenirnaya-produkcziya-s-logotipom-1.ru .
рекламная продукция с логотипом компании рекламная продукция с логотипом компании .
корпоративные подарки москва корпоративные подарки москва .
реабилитационный центр для наркозависимых реабилитационный центр для наркозависимых .
заказать сувениры с логотипом suvenirnaya-produkcziya-s-logotipom.ru .
изготовление сувенирной продукции изготовление сувенирной продукции .
лечение наркомании лечение наркомании .
сувенирная продукция москва suvenirnaya-produkcziya-s-logotipom-1.ru .
Гранитные памятники https://allgranit.ru от производителя в Москве: надёжность и красота на века. Компания Allgranit предлагает гранитные памятники напрямую от производителя — без посредников, переплат и долгих ожиданий. Мы создаём мемориалы, которые сохраняют память о дорогих людях на долгие годы.
вывод из запоя на дому цена вывод из запоя на дому цена .
вывод из запоя цена воронеж вывод из запоя цена воронеж .
вывод из запоя на дому вывод из запоя на дому .
вывод из запоя с выездом вывод из запоя с выездом .
Нужен ремонт? мастера по ремонту и отделке под ключ, быстро и качественно. Дизайн, отделка, электрика и сантехника. Гарантия на работы и прозрачная смета. Выполняем проекты любой сложности.
вывод из запоя на дому вывод из запоя на дому .
снятие запоя цена vyvod-iz-zapoya-na-domu-voronezh-3.ru .
вывод из запоя на дому вывод из запоя на дому .
вывод из запоя стоимость вывод из запоя стоимость .
вывод из запоя стоимость вывод из запоя стоимость .
Проблемы с алкоголем? https://www.narkolog-na-dom-vizov.ru срочная помощь при алкогольной и наркотической интоксикации. Вывод из запоя, капельницы и поддержка 24/7. Анонимно, быстро и безопасно с выездом врача на дом.
Лучшее путешествие джиппинг в крыму горы, каньоны и побережье. Увлекательные маршруты, опытные гиды и яркие впечатления от путешествий по Крыму.
Do you trade cryptocurrencies? bitkelttrade official page automate your transactions and earn passive income. Smart algorithms analyze the market and help you make decisions. Increase your income and reduce risks with modern technology.
снятие интоксикации на дому снятие интоксикации на дому .
Купить масло гидравлическое масло оптом в бочках 200 литров по цене производителя без наценок посредников.
снятие запоя на дому vyvod-iz-zapoya-na-domu-voronezh-1.ru .
вывод из запоя цена воронеж вывод из запоя цена воронеж .
вывод из запоя цены вывод из запоя цены .
вывод из запоя цена воронеж вывод из запоя цена воронеж .
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
круглосуточный вывод из запоя круглосуточный вывод из запоя .
вывод из запоя цена на дому вывод из запоя цена на дому .
нарколог на дом вывод из запоя нарколог на дом вывод из запоя .
нарколог на дом вывод из запоя на дому нарколог на дом вывод из запоя на дому .
выведение из запоя на дому выведение из запоя на дому .
вывод из запоя цена воронеж вывод из запоя цена воронеж .
זה, ” הוא אמר והוציא ארבעה כדורים מכיסו. הוא ניגש לחברה שלי: פתח את הפה. בתגובה, היא רק מלמלה משהו מטושטש. ואז הוא הכה אותה בפנים: זה יהיה המקרה עם כל אחד מכם שמעז לא לציית. השניים חשמלית. היא לא התרחקה. לא רציתי. ידו, מונחת על גב הספה, החליקה לאט אל כתפה, ואצבעותיו נגעו בקלות בעורה. היא רעדה, אבל לא מהקור. זה היה חם, כמעט צורב. “הוא אמר, והיה משהו חדש בקולו, https://avitalmarks.co.il/
Лучшее путешествие джип туры Крым горы, каньоны и побережье. Увлекательные маршруты, опытные гиды и яркие впечатления от путешествий по Крыму.
Do you trade cryptocurrencies? ai-driven trading bitkelttrade automate your transactions and earn passive income. Smart algorithms analyze the market and help you make decisions. Increase your income and reduce risks with modern technology.
выведение из запоя на дому vyvod-iz-zapoya-na-domu-samara.ru .
вывод из запоя самара на дому vyvod-iz-zapoya-na-domu-samara-1.ru .
Коммерческий и государственный тендер — это конкурентная процедура выбора поставщика товаров или оказания услуг. Заказчик размещает требования, а компании подают заявки и участвуют в торгах.
Разгадайте все загадки – тендерное сопровождение под ключ
вывод из запоя самара на дому vyvod-iz-zapoya-na-domu-samara-2.ru .
поставить капельницу от запоя на дому цена поставить капельницу от запоя на дому цена .
вывод из запоя круглосуточно самара вывод из запоя круглосуточно самара .
Do you trade cryptocurrencies? bitkelttrade official link automate your transactions and earn passive income. Smart algorithms analyze the market and help you make decisions. Increase your income and reduce risks with modern technology.
вывод из запоя цены екатеринбург vyvod-iz-zapoya-na-domu-ekaterinburg-1.ru .
наркология вывод из запоя наркология вывод из запоя .
капельница после запоя цена капельница после запоя цена .
Выгодные условия масло для спецтехники оптом на закупку масел и смазок оптом для промышленных предприятий.
вывод из запоя на дому нижний новгород вывод из запоя на дому нижний новгород .
нарколог на дом вывод из запоя на дому нарколог на дом вывод из запоя на дому .
Купить 3D-принтеры https://reporter63.ru/content/view/786013/zagolovok-razvitie-3dpechati-kak-novaya-tehnologiya-menyaet-nash-mir в Минске — продажа оборудования для печати пластиком и фотополимером. Подбор, консультации и гарантия. Найдите идеальный 3D-принтер для ваших задач.
Продажа 3D-принтеров http://reporter63.ru/content/view/786012/zagolovok-3dprinter-revolyuciya-v-proizvodstve-i-tvorchestve Минск — FDM, SLA и другие технологии печати. Широкий ассортимент, выгодные цены и профессиональные консультации. Подберите устройство под свои задачи.
вывод из запоя круглосуточно самара вывод из запоя круглосуточно самара .
Узнать больше здесь: https://l-parfum.ru/catalog/mandarina-duck/
Часто предприниматели объединяют понятия тендер и госзакупки, так как обе процедуры связаны с конкурсным выбором поставщика. Однако между ними существуют определённые различия, которые важно понимать перед началом работы в этой сфере.
Полная картина — внутри – https://tendernoe-soprovozhdenie-rostov-na-donu.ru
круглосуточный вывод из запоя круглосуточный вывод из запоя .
вывод из запоя на дому в екатеринбурге вывод из запоя на дому в екатеринбурге .
вывод из запоя на дому нижний новгород круглосуточно vyvod-iz-zapoya-na-domu-nizhnij-novgorod.ru .
выведение из запоя на дому самара выведение из запоя на дому самара .
вызов нарколога на дом запой вызов нарколога на дом запой .
Утилизация биоотходов https://stroi-musor.su вывоз и переработка пищевых и растительных отходов. Экологичные решения, соблюдение стандартов и надежный сервис для предприятий и частных клиентов.
ЖК Солянка Парк https://tzstroy.su современный жилой комплекс с удобной инфраструктурой и комфортной средой. Квартиры с продуманными планировками, благоустроенная территория и удобная транспортная доступность.
ГНБ бурение https://stroytex.su современный способ прокладки инженерных сетей без раскопок. Подходит для дорог, рек и плотной застройки. Точная технология, сокращение сроков и минимальные затраты.
сколько стоит капельница от запоя сколько стоит капельница от запоя .
врач на дом капельница от запоя врач на дом капельница от запоя .
вывод из запоя на дому круглосуточно вывод из запоя на дому круглосуточно .
выведение из запоя екатеринбург выведение из запоя екатеринбург .
капельница от запоя капельница от запоя .
Ознакомьтесь с сайтом и если нашли замечания опишите их с помощью формы https://magic.net.ru/docs/
Вверху справа нажмите на изображение флажка https://magic.net.ru/news/akcii/podkljuchaj-svoih-druzej-k-nashemu-inter/
Беспроводной маршрутизатор https://magic.net.ru/rules/
Маршрутизатор пересылает данные между вашей сетью и Интернетом https://magic.net.ru/blog/kak-vzlomat-algoritmy-socsetej-i-videt-tolko-neobhodimoe/
При использовании беспроводного маршрутизатора вы можете подключить компьютеры к своей сети, используя радиосвязь вместо проводов https://magic.net.ru/docs/
Существует несколько различных типов технологий беспроводной сети, которые включают 802 https://magic.net.ru/blog/chto-takoe-tjomnyj-internet-i-chem-on-otlichaetsja-ot-darkneta/
11a, 802 https://magic.net.ru/requiz/
11b, 802 https://magic.net.ru/news/no-news_tax/iptv-besplatno-2-mesjaca/
11g, 802 https://magic.net.ru/docs/
11n, 802 https://magic.net.ru/contacts/
11ac и 802 https://magic.net.ru/requiz/
11ax https://magic.net.ru/news/akcii/podkljuchaj-svoih-druzej-k-nashemu-inter/
Открывайте браузер и входите в Интернет https://magic.net.ru/news/no-news_tax/sovershi-pryzhok-na-kachestvennyj-internet-bez-poteri-balansa/
Какой способ выбрать?
В том же блоке найдите компонент IPv4 и дважды кликните по нему левой кнопкой мыши — откроются настройки https://magic.net.ru/news/akcii/s-nami-vygodno-plati-menshe-poluchaj-bo/
Поставьте маркеры напротив опций «Использовать следующий IP-адрес» и «Использовать следующие адреса DNS-серверов» https://magic.net.ru/docs/
выведение из запоя на дому в екатеринбурге выведение из запоя на дому в екатеринбурге .
вывод из запоя цены вывод из запоя цены .
вывод из запоя цена вывод из запоя цена .
запой капельница нарколог запой капельница нарколог .
вывод из алкогольного запоя нарколог 24 вывод из алкогольного запоя нарколог 24 .
помощь вывода запоя помощь вывода запоя .
вывод из запоя вывод из запоя .
вывод из запоя капельница на дому вывод из запоя капельница на дому .
вывод из запоя капельница kapelnica-ot-zapoya-nizhnij-novgorod.ru .
выведение из запоя на дому самара выведение из запоя на дому самара .
вывод из запоя круглосуточно vyvod-iz-zapoya-na-domu-nizhnij-novgorod.ru .
вывод из запоя на дому екатеринбург круглосуточно вывод из запоя на дому екатеринбург круглосуточно .
вывод из запоя в екатеринбурге вывод из запоя в екатеринбурге .
выведение из запоя на дому в екатеринбурге выведение из запоя на дому в екатеринбурге .
вывод из запоя цены вывод из запоя цены .
капельница при алкогольной интоксикации на дому цена капельница при алкогольной интоксикации на дому цена .
флаг с надписью на заказ сделать флаг на заказ
вывода из запоя 24 вывода из запоя 24 .
поставить капельницу от запоя поставить капельницу от запоя .
вывод из запоя нарколог24 vyvod-iz-zapoya-na-domu-sankt-peterburg.ru .
выведение из запоя на дому vyvod-iz-zapoya-na-domu-samara-2.ru .
вывод из запоя самара vyvod-iz-zapoya-na-domu-samara-3.ru .
вывод из запоя капельница екатеринбург vyvod-iz-zapoya-na-domu-ekaterinburg-3.ru .
https://mhp.ooo/catalog/imatinib
капельница в нижнем новгороде цена капельница в нижнем новгороде цена .
капельница после запоя цена капельница после запоя цена .
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article. https://accounts.binance.info/es-MX/register-person?ref=GJY4VW8W
врач капельница алкоголь на дом врач капельница алкоголь на дом .
При разработке элитных моделей мебельных гарнитуров для спальни дизайнеры компании учитывают особенности планировки помещения, а также предпочтения клиентов в выборе дизайна, материала и фурнитуры https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/?PAGEN_1=11
Мы производим авторскую мебель по индивидуальным размерам только из высококачественной древесины https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/vhodnie-dveri/vhodnaa-dver-e8.html
Прозрачные дверцы, резьба, декоративное оформление позволяют воплотить в жизнь самые смелые идеи https://www.legnostyle.ru/catalog/mebel/kb-25.html
Укомплектуем Ваш дом, квартиру, офис или ресторан https://www.legnostyle.ru/catalog/inter-eri/stenovie-paneli/s16.html
Дизайнеры тщательно разработают проект, учитывая все пожелания и тонкости создания мебели https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/perfetto/
Список авторской мебели по индивидуальным проектам очень широкий и включает: кухни, шкафы, столы, кровати, двери, лестницы, окна, кессонные потолки и др https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/nestandarnye/a-27.html
Мы производим различные элементы интерьера, декора https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/model-p5.html
Компания специализируется на выпуске самой разнообразной продукции по индивидуальным проектам https://www.legnostyle.ru/catalog/mebel/garderobnie/?PAGEN_1=3
Возможность воссоздания интерьера по эскизам https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/vhodnaa-dver-e11.html
Если вы не подобрали ничего из нашего каталога, закажите создание гарнитура по индивидуальному эскизу https://www.legnostyle.ru/catalog/kuhni/kuhna-28.html
Эту услугу уже оценили многие архитекторы и дизайнеры https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/nestandarnye/dver-p25.html
Вы можете приобрести у нас немецкую мебель, которая будет полностью соответствовать дизайнерскому замыслу https://www.legnostyle.ru/catalog/mebel/derevyannye-stoly/?PAGEN_1=3
Обращаем Ваше внимание на то, что данный интернет-сайт носит исключительно информационно-ориентировочный характер и не является публичной офертой, определяемой положениями Статьи 437 Гражданского кодекса РФ https://www.legnostyle.ru/catalog/mebel/garderobnaa-model-scg-12.html
Конечно, покупать немецкую кухню в СПб дорого, но это оправданные траты, поскольку российских аналогов не существует и дорогие кухни на заказ остаются все также востребованы https://www.legnostyle.ru/catalog/inter-eri/potolki/pt-26.html
В Санкт-Петербурге, Москве и других городах люди выбирают мебель премиум уровня для самого важного помещения в доме и кухни Германии — отличный выбор!
Две означенные страны являются лидерами среди производителей элитной мебели https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/iz-dyba/?PAGEN_1=3
Лучшее, что существует на сегодня – либо итальянская, либо французская мебель https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/nestandarnye/mejkomnatnaya-dver-d36.html
нарколог вывод из запоя нарколог вывод из запоя .
Заказать расчёт https://norsy.ru/kontakty
Наша швейная фабрика активно сотрудничает с медийными лицами (блогеры, актеры, реперы) в сфере разработки и пошива фирменного мерча! Если вы хотите удивить своих фанатов качественными продуктом по доступной цене? — Оставьте заявку на нашем сайте или позвоните, и вы убедитесь, что наши цены подойдут вам!
Оставить заявку https://norsy.ru/
Компания «ЭЛЬ-ТЕКС ПОШИВ» занимается пошивом одежды для заказчиков из Москвы и регионов России https://norsy.ru/poshiv-futbolok
На производстве работают лучшие конструкторы , технологи, дизайнеры, швеи и лаборанты https://norsy.ru/
Шьём текстильные и трикотажные изделия крупным и мелким оптом (от 10 штук на размер, от 30 штук на модель).
Швейный цех основан в 2000 году, вот уже более 18 лет мы занимаемся пошивом мужской и женской одежды для заказчиков из Москвы и регионов https://norsy.ru/
В нашем распряжение собественное производство размером более 350М2, 30 швейных машин, 5 печатных станков и многое другое! Занимаемся крупным и мелким оптом (от 50 штук на размер, от 30 штук на модель). На нашей фабрике работают лучшие проектировщики, обеспечивающие точность в разработке лекала любой сложности https://norsy.ru/kontakty
футболка с коротким рукавом https://norsy.ru/otzyvy
капельницы чтобы выйти из запоя vyvod-iz-zapoya-na-domu-ekaterinburg-2.ru .
вывод из запоя срочно vyvod-iz-zapoya-na-domu-nizhnij-novgorod-1.ru .
помощь вывода запоя помощь вывода запоя .
капельница при алкогольной интоксикации на дому цена капельница при алкогольной интоксикации на дому цена .
вывод из запоя нарколог 24 вывод из запоя нарколог 24 .
вывод из запоя санкт петербург вывод из запоя санкт петербург .
вывести из запоя цена вывести из запоя цена .
вывод из запоя дешево воронеж вывод из запоя дешево воронеж .
вывести из запоя цена вывести из запоя цена .
вывод из запоя нарколог24 vyvod-iz-zapoya-na-domu-sankt-peterburg-2.ru .
вывод из запоя цена воронеж vyvod-iz-zapoya-na-domu-voronezh-9.ru .
вывод из запоя на дому телефоны vyvod-iz-zapoya-na-domu-voronezh-8.ru .
Хочешь оригинальную подушку? аниме подушки дакимакуры комфорт и уют для сна. Длинная форма, мягкий наполнитель и стильные принты. Отлично подходит для отдыха и расслабления.
вывод из запоя капельница воронеж вывод из запоя капельница воронеж .
вывод из запоя в спб вывод из запоя в спб .
вывода из запоя 24 вывода из запоя 24 .
выведение из запоя в воронеже выведение из запоя в воронеже .
выведение из запоя воронеж vyvod-iz-zapoya-na-domu-voronezh-9.ru .
good things about steroids
References:
https://iskustva.net/user/toylamp12
капельница от запоя воронеж капельница от запоя воронеж .
цена вывод из запоя на дому vyvod-iz-zapoya-na-domu-samara-8.ru .
выведение из запоя выведение из запоя .
выведение из запоя выведение из запоя .
вывод из запоя на дому недорого вывод из запоя на дому недорого .
вывод из запоя на дому в воронеже вывод из запоя на дому в воронеже .
Нужен пластический хирург? клиника косметологии и пластической хирургии современные операции и эстетические процедуры. Опытные хирурги, безопасные методики и индивидуальный подход. Консультации, диагностика и качественный результат.
вывести из запоя воронеж vyvod-iz-zapoya-na-domu-voronezh-9.ru .
нарколог вывод из запоя нарколог вывод из запоя .
вывод из алкогольного запоя нарколог24 vyvod-iz-zapoya-na-domu-sankt-peterburg-2.ru .
нарколог на дом вывод из запоя на дому нарколог на дом вывод из запоя на дому .
с 2010 года https://maze.tattoo/catalog/gh/zhar-ptitsa/
Делали пирсинг у Андрея https://maze.tattoo/catalog/b/bozhiya-korovka/
все очень понравилось https://maze.tattoo/catalog/b/braslety/
все рассказали про процедуру, ее исполнение, на все вопросы отвечали https://maze.tattoo/catalog/k/kity/
в процессе заживления также поддержка была https://maze.tattoo/catalog/ch/cheshirskiy-kot/
мастера советую, все аккуратно, быстро, качественно сделали https://maze.tattoo/catalog/l/luna/
салон приятный, находится недалеко от метро https://maze.tattoo/catalog/ee/
очень довольны https://maze.tattoo/catalog/d/drakony/
Наши профессиональные мастера в уютном и современном тату–салоне обладают всеми необходимыми знаниями и навыками, чтобы вы смогли получить именно такой результат, который ожидаете https://maze.tattoo/catalog/c/strekoza/
Качественную, красивую татуировку https://maze.tattoo/catalog/p/palm/
У каждого мастера тату-салона собственный подход к работе, слушатель вправе выбрать того из них, чьи рисунки ему ближе https://maze.tattoo/catalog/m/mifologiya/
Наши программы составлены таким образом, чтобы подготовить настоящих профессионалов, которые могут придумать эскиз, нарисовать его в соответствующем программном обеспечении и нанести на кожу клиента https://maze.tattoo/catalog/n/neft/
Выпускники академии получают работу в лучших тату салонах России, а многие из них успешно работают даже в Азии и Европе https://maze.tattoo/catalog/r/rozy/
Лучшие в городе! Да и не только в городе https://maze.tattoo/catalog/p/podkova/
Очень аккуратно , очень красивые работы! Вторую сын делает , приедем за третьей https://maze.tattoo/catalog/d/drakony/
Студия BlackFly 3200 ?
цена вывод из запоя на дому vyvod-iz-zapoya-na-domu-samara-10.ru .
вывод из запоя на дому недорого вывод из запоя на дому недорого .
выведение из запоя в воронеже выведение из запоя в воронеже .
вывод из запоя на дому воронеж цены вывод из запоя на дому воронеж цены .
вывод из запоя цена воронеж vyvod-iz-zapoya-na-domu-voronezh-10.ru .
лечение алкоголизма с выездом на дом лечение алкоголизма с выездом на дом .
цена вывод из запоя на дому vyvod-iz-zapoya-na-domu-samara-10.ru .
Нужна мебель? производство мебели на заказ эксклюзивные изделия из натурального дерева. Индивидуальный дизайн, качественные материалы и точное изготовление. Решения для дома и бизнеса.
вывести из запоя на дому вывести из запоя на дому .
вывести из запоя на дому vyvod-iz-zapoya-na-domu-nizhnij-novgorod-4.ru .
вывод из запоя на дому нижний новгород цена вывод из запоя на дому нижний новгород цена .
вывод из запоя круглосуточно нижний новгород вывод из запоя круглосуточно нижний новгород .
вывод из запоя в нижнем новгороде вывод из запоя в нижнем новгороде .
вывод из запоя цена воронеж vyvod-iz-zapoya-na-domu-voronezh-11.ru .
вывод из запоя дешево вывод из запоя дешево .
вывод из запоя на дому самара круглосуточно вывод из запоя на дому самара круглосуточно .
вывод из запоя на дому вывод из запоя на дому .
вывод из запоя цена воронеж vyvod-iz-zapoya-na-domu-voronezh-10.ru .
запой вывод на дому запой вывод на дому .
вывод из запоя цены нижний новгород вывод из запоя цены нижний новгород .
выведение из запоя нижний новгород выведение из запоя нижний новгород .
Капельница от похмелья с медицинским контролем в Нижнем Новгороде — это эффективный способ восстановления после алкогольной интоксикации, который позволяет быстро и безопасно нормализовать состояние пациента. Основное отличие такой капельницы от домашних методов состоит в том, что вся процедура проходит под контролем профессионалов, что минимизирует риски для здоровья и повышает эффективность лечения.
Разобраться лучше – капельница от похмелья на дом
нарколог на дом вывод из запоя на дому нарколог на дом вывод из запоя на дому .
References:
Online Casino Echtgeld Apple Pay
References:
https://hack.allmende.io/s/TOv-L8z33
Нужна премиум мебель? купить элитную мебель изготовление на заказ. Натуральные материалы, эксклюзивный дизайн и долговечность. Решения для дома и бизнеса с высоким уровнем качества.
капельница от запоя анонимно капельница от запоя анонимно .
6 https://magic.net.ru/news/
Затем ждем несколько минут – на Ethernet-кабель поступит соединение; 7 https://magic.net.ru/payment/
Чтобы остановить раздачу интернета, нужно в “Командной строке” ввести “netsh wlan stop hostednetwork”, а для ее активации в следующий раз – “netsh wlan start hostednetwork”.
Вставляем модуль в USB-порт ПК https://magic.net.ru/blog/kak-vzlomat-algoritmy-socsetej-i-videt-tolko-neobhodimoe/
Инсталляция программы начнется автоматически https://magic.net.ru/blog/kak-socseti-vlijajut-na-psihiku-novye-issledovanija/
Если этого не произошло, открываем папку устройства через проводник и запускаем программу установки вручную https://magic.net.ru/news/akcii/s-nami-vygodno-plati-menshe-poluchaj-bo/
После завершения инсталляции нажимаем на клавишу «Запустить» https://magic.net.ru/news/no-news_tax/sovershi-pryzhok-na-kachestvennyj-internet-bez-poteri-balansa/
2 https://magic.net.ru/news/akcii/podkljuchaem-bez-poter/
Вводим после “user>” команду “netsh wlan show drivers” и нажимаем Enter https://magic.net.ru/news/no-news_tax/vazhnaja-informacija/
Если в графе “Поддержка размещенной сети” написано “Да”, то переходим к следующему шагу, а если “Нет”, то это означает, что адаптер не может работать в режиме раздачи;
Найдите в левой части окна строчку «Изменение параметров адаптера» и кликните по ней https://magic.net.ru/rules/
При выборе поставщика услуг следует учитывать несколько критериев https://magic.net.ru/blog/kak-internet-vlijaet-na-myshlenie-uskorjaet-ili-zamedljaet-nas/
Подключение к сети Wi-Fi в Windows https://magic.net.ru/blog/chto-takoe-spufing-i-kak-ne-stat-ego-zhertvoj/
Капельница от похмелья с медицинским контролем представляет собой комплексную терапию, которая включает в себя различные препараты, направленные на быстрое восстановление организма. Каждый элемент процедуры подобран с учётом состояния пациента, что позволяет обеспечить максимальную эффективность лечения и минимизировать возможные риски.
Подробнее тут – http://www.domen.ru
вывод из запоя дешево вывод из запоя дешево .
вывод из запоя на дому цена вывод из запоя на дому цена .
Выезд нарколога на дом в Самаре организован так, чтобы пациент получил помощь без ожидания и без лишней нагрузки на организм. После обращения специалист приезжает по указанному адресу, проводит первичный осмотр, оценивает общее состояние, уровень интоксикации, показатели давления, пульса, дыхания и собирает краткий анамнез. На основании этой оценки врач определяет, можно ли безопасно оказывать помощь на дому, и подбирает подходящую схему лечения, включая возможное кодирование или вывод из алкоголизма. Такой формат позволяет начать медицинские мероприятия сразу после осмотра и быстро перейти к стабилизации состояния.
Углубиться в тему – нарколог на дом вывод
Процесс капельницы включает внутривенное введение различных растворов, которые помогают нейтрализовать эффекты алкогольной интоксикации, включая последствия запоя и алкоголизма. Наиболее часто в составе капельницы используются солевые и глюкозные растворы, витамины группы B, а также препараты для детоксикации организма. Эти компоненты помогают быстро восстановить водно-электролитный баланс, улучшить обмен веществ и ускорить выведение продуктов распада алкоголя.
Получить дополнительные сведения – капельница от похмелья на дому самара
Услуги нарколога на дому в Самаре включают не только экстренный осмотр, но и комплекс медицинских мероприятий, направленных на снижение интоксикации, облегчение тяжелых симптомов и общее восстановление состояния пациента. Объем помощи зависит от клинической картины, длительности употребления алкоголя или других психоактивных веществ, возраста, хронических заболеваний и текущих рисков. Врач подбирает схему индивидуально, исходя из того, какие задачи необходимо решить в конкретный момент — снять острые проявления, стабилизировать самочувствие или подготовить пациента к дальнейшему лечению зависимости.
Исследовать вопрос подробнее – вызов нарколога на дом в самаре
Капельница от запоя в Нижнем Новгороде: снятие интоксикации, восстановление организма и помощь при запое под контролем специалистов в наркологической клинике «Похмельная служба»
Подробнее можно узнать тут – https://kapelnica-ot-zapoya-nizhnij-novgorod-4.ru
вывод из запоя на дому в нижнем новгороде вывод из запоя на дому в нижнем новгороде .
Медицинский контроль играет ключевую роль в безопасности и эффективности процедуры. Под присмотром опытного специалиста исключаются риски неправильной дозировки препаратов, побочных эффектов и осложнений, что особенно важно при проведении капельниц у пациентов с хроническими заболеваниями или при наличии индивидуальных противопоказаний.
Подробнее тут – капельница от похмелья на дому нижний новгород
вывод из запоя врач на дом вывод из запоя врач на дом .
срочный вывод из запоя на дому vyvod-iz-zapoya-na-domu-nizhnij-novgorod-6.ru .
Капельница от похмелья — это медицинская процедура, которая помогает организму быстрее восстанавливаться после чрезмерного употребления алкоголя, включая последствия запоя и хронического алкоголизма. Эффект капельницы заключается в быстром восстановлении водно-электролитного баланса, выведении токсинов и устранении неприятных симптомов похмелья, таких как головная боль, тошнота и слабость. В отличие от обычных методов, капельница позволяет минимизировать время восстановления и улучшить состояние пациента значительно быстрее.
Узнать больше – капельница от похмелья на дом в самаре
Капельница от запоя представляет собой процедуру внутривенного введения специальных растворов, направленных на устранение токсинов, нормализацию обменных процессов и восстановление функций организма. Это позволяет быстрее вывести алкогольные токсины и минимизировать их воздействие на внутренние органы. В некоторых случаях может потребоваться наркологическая помощь и консультация психиатра, особенно если у пациента есть длительная зависимость или другие психоэмоциональные расстройства, которые требуют вмешательства специалистов с большим стажем работы.
Подробнее тут – капельница от запоя на дому цена нижний новгород
бонусы казино подходят для игры без ограничений с минимальными ставками – плей фортуна официальный
нарколог на дом вывод из запоя на дому нарколог на дом вывод из запоя на дому .
Выезд нарколога на дом в Самаре организован так, чтобы пациент получил помощь без ожидания и без лишней нагрузки на организм. После обращения специалист приезжает по указанному адресу, проводит первичный осмотр, оценивает общее состояние, уровень интоксикации, показатели давления, пульса, дыхания и собирает краткий анамнез. На основании этой оценки врач определяет, можно ли безопасно оказывать помощь на дому, и подбирает подходящую схему лечения, включая возможное кодирование или вывод из алкоголизма. Такой формат позволяет начать медицинские мероприятия сразу после осмотра и быстро перейти к стабилизации состояния.
Изучить вопрос глубже – нарколог на дом анонимно
вывод из запоя дешево нижний новгород вывод из запоя дешево нижний новгород .
Процесс капельницы включает внутривенное введение различных растворов, которые помогают нейтрализовать эффекты алкогольной интоксикации, включая последствия запоя и алкоголизма. Наиболее часто в составе капельницы используются солевые и глюкозные растворы, витамины группы B, а также препараты для детоксикации организма. Эти компоненты помогают быстро восстановить водно-электролитный баланс, улучшить обмен веществ и ускорить выведение продуктов распада алкоголя.
Исследовать вопрос подробнее – http://kapelnicza-ot-pokhmelya-samara-6.ru
вывод из запоя врач на дом вывод из запоя врач на дом .
Капельница от запоя представляет собой процедуру внутривенного введения специальных растворов, направленных на устранение токсинов, нормализацию обменных процессов и восстановление функций организма. Это позволяет быстрее вывести алкогольные токсины и минимизировать их воздействие на внутренние органы. В некоторых случаях может потребоваться наркологическая помощь и консультация психиатра, особенно если у пациента есть длительная зависимость или другие психоэмоциональные расстройства, которые требуют вмешательства специалистов с большим стажем работы.
Подробнее можно узнать тут – капельницы от запоя вызов
быстрый анонимный вывод из запоя на дому быстрый анонимный вывод из запоя на дому .
вывод из запоя дешево нижний новгород вывод из запоя дешево нижний новгород .
Похмельный синдром — это не просто неприятное ощущение, а целый комплекс симптомов, которые могут варьироваться от легкого дискомфорта до тяжелых состояний. Капельница от похмелья используется в случаях, когда симптомы становятся особенно выраженными и требуют вмешательства профессионала. Врачи отмечают, что капельница помогает значительно ускорить процесс восстановления организма после алкоголя, избавляя от боли, тошноты и слабости.
Получить дополнительную информацию – kapelnicza-ot-pokhmelya-nizhnij-novgorod-2.ru/
Нарколог на дом в Самаре: круглосуточная помощь, вывод из запоя и медицинская поддержка на дому под контролем специалистов в наркологической клинике «Похмельная служба»
Исследовать вопрос подробнее – нарколог на дом
Как отмечает ведущий научный сотрудник ФГБУН «НМИЦ психиатрии и наркологии» Минздрава России, наличие междисциплинарной команды — один из основных факторов, определяющих успех терапии при зависимости.
Углубиться в тему – лечение наркомании реабилитация
Перед постановкой капельницы специалист оценивает общее состояние пациента, измеряет давление, пульс, уточняет анамнез и возможные противопоказания. На основании этих данных формируется индивидуальный состав, который обеспечивает не только устранение симптомов похмелья, но и безопасное восстановление организма.
Получить дополнительные сведения – капельница от похмелья цена в самаре
Дизайн-проект интерьера https://stroydvor11.ru/kak-sdelat-dizayn-proekt-samostoyatelno-polnaya-instruktsiya-i-obzor-programm.html своими руками — идеи, советы и этапы разработки. Планировка, визуализация и подбор материалов для создания стильного и удобного пространства.
вывод из запоя на дому вывод из запоя на дому .
Медицинский портал https://med-portal-24.ru актуальная информация о здоровье, заболеваниях и методах лечения. Симптомы, диагностика, профилактика и советы специалистов для поддержания здоровья.
срочный вывод из запоя срочный вывод из запоя .
Капельница действует быстро благодаря тому, что активные вещества вводятся непосредственно в кровь, минуя желудочно-кишечный тракт. Это позволяет быстро уменьшить симптомы, такие как головная боль, тошнота, слабость, а также нормализовать работу печени и почек, которые страдают от длительного употребления алкоголя. В некоторых случаях, если требуется длительное наблюдение, пациент может быть направлен в стационар, и лечение может продолжаться на летний период с более тщательным контролем состояния.
Выяснить больше – капельница от запоя на дому цена
Мир Labubu https://labubu-world.ru коллекционные фигурки, персонажи и новинки популярной серии. Узнайте о героях, редких выпусках и особенностях коллекции. Погружайтесь в атмосферу Labubu и следите за обновлениями.
References:
Leo casino
References:
https://mysingledesire.com/members/slaveactive91/activity/15233/
Доска объявлений https://oren-i.ru удобный сервис для размещения и поиска объявлений. Продажа, покупка, услуги и работа. Быстро публикуйте объявления и находите нужные предложения в вашем городе.
References:
Rules for blackjack
References:
https://ztuto.dyjix.fr/member.php?action=profile&uid=26550
Инженерные изыскания https://sever-geo.com для строительства в Твери — геология, геодезия и экология участка. Комплексные исследования для проектирования и строительства. Точные данные, соблюдение норм и оперативные сроки выполнения.
платная скорая вывод из запоя vyvod-iz-zapoya-v-staczionare-sankt-peterburg.ru .
наркология вывод из запоя в стационаре наркология вывод из запоя в стационаре .
вызов врача нарколога на дом москва недорого вызов врача нарколога на дом москва недорого .
запой стационар запой стационар .
Разработка сайтов https://domenanet.online на Laravel — современные веб-проекты с высокой скоростью и безопасностью. Индивидуальные решения, интеграции и масштабируемая архитектура для бизнеса любого уровня.
выведение из запоя санкт петербург стационар выведение из запоя санкт петербург стационар .
психиатр нарколог на дом в москве narkolog-na-dom-moskva-1.ru .
услуги нарколога на дому услуги нарколога на дому .
Солянка Парк https://tzstroy.su жилой комплекс с современными квартирами и удобной инфраструктурой. Отличный выбор для жизни с комфортом и доступом ко всем необходимым объектам.
вывести из запоя срочно вывести из запоя срочно .
вызов врача нарколога на дом narkolog-na-dom-moskva-4.ru .
Online football match statistics soccer stand live scores, events, and live broadcasts. Follow games in real time, analyze teams, and never miss a beat.
Внутренний объем 1 м https://deneb-spb.ru/krestoviny
п https://deneb-spb.ru/contacts
Стоимость доставки от 1500 рублей https://deneb-spb.ru/krestoviny
VTp https://deneb-spb.ru/adaptory-nasadki-i-sverla-dlya-sedel
700 https://deneb-spb.ru/mufty-i-perekhodniki
0020 https://deneb-spb.ru/rasprodazha
25 https://deneb-spb.ru/zaglushki
Номинальное давление,PN, бар 20 Максимальная температура рабочей среды, ?С 95 Минимальная температура хранения ?С -30 Материал корпуса Полипропилен https://deneb-spb.ru/trojniki
В таблице ниже приведены данные по расчетному давлению полипропиленовых труб PN 10, PN 16 PN 20, PN 25 в зависимости от срока службы и температуры https://deneb-spb.ru/shurup-shpilka
По запросу 128 https://deneb-spb.ru/sedla
80 https://deneb-spb.ru/rasprodazha
вывод из запоя в стационаре санкт-петербург вывод из запоя в стационаре санкт-петербург .
All live match results http://www.live-score.com.az game information and data from the leading football leagues on one site. Up-to-date scores, statistics, and events for easy tracking.
The site https://play-mods.com.az/ contains information about downloading PlayMods, downloading PlayMods APK files, compatibility with iOS, Android, and PC, as well as basic information about GTA San Andreas and other modified games.
выведение из запоя санкт петербург стационар выведение из запоя санкт петербург стационар .
вызов врача нарколога вызов врача нарколога .
Live football https://www.qolvar.com.az broadcasts, daily game streams, football news, and the most popular live streaming sections.
Нужен ремонт электродвигателя? https://profremont.kz срочный ремонт и перемотка в Алматы от ПрофЭлектроРемонт-1: диагностика, восстановление и запуск в минимальные сроки, чтобы ваше производство не простаивало. Опытные мастера, гарантия результата и использование качественных материалов — надежность, которой можно доверять.
Today’s horoscope https://t.me/s/ulduz_fali daily forecasts and life surprises for all zodiac signs. Love, career, finances, and mood. Discover the future every day.
психиатр нарколог на дом в москве narkolog-na-dom-moskva-1.ru .
выведение из запоя стационар санкт петербург vyvod-iz-zapoya-v-staczionare-sankt-peterburg-1.ru .
Мнения игроков 1win отзывы — реальные отзывы о платформе, бонусах и выводе средств. Узнайте о плюсах и минусах сервиса и сделайте правильный выбор.
вывод из запоя в клинике вывод из запоя в клинике .
вывод из запоя в стационаре клиника вывод из запоя в стационаре клиника .
Реальные 1win отзывы игроков — честные мнения о работе сервиса. Узнайте о ставках, бонусах, выводе средств и надежности платформы.
Честные 1win отзывы — плюсы и минусы сервиса, опыт пользователей и оценки. Информация о выплатах, бонусах и удобстве использования платформы.
нарколог на дом круглосуточно москва цены нарколог на дом круглосуточно москва цены .
Настоящие 1win отзывы — опыт пользователей, выплаты, бонусы и работа сервиса. Полезная информация перед началом использования платформы.
вывести из запоя капельница на дому цена вывести из запоя капельница на дому цена .
mostbet казино казино сочи
выведение из запоя в стационаре спб выведение из запоя в стационаре спб .
Premium xxx platforms biedn hoogwaardige inhoud voor volwassen entertainment.
Kies voor betrouwbare hubs voor een veilige en plezierige ervaring.
Feel free to visit my website BUY VIAGRA ONLINE
вызвать врача нарколога на дом москва недорого вызвать врача нарколога на дом москва недорого .
вывод из запоя кодирование вывод из запоя кодирование .
вызвать врача нарколога на дом вызвать врача нарколога на дом .
наркологическая помощь на дому в москве наркологическая помощь на дому в москве .
выведение из запоя в стационаре спб выведение из запоя в стационаре спб .
вывод из запоя в клинике спб vyvod-iz-zapoya-v-staczionare-sankt-peterburg-1.ru .
вывод из запоя в клинике спб vyvod-iz-zapoya-v-staczionare-sankt-peterburg-2.ru .
После употребления алкоголя состояние может быстро ухудшиться: появляется головная боль, тошнота, головокружение и слабость. Это следствие того, что в организме накапливаются токсины, продукты распада этанола и нарушается водно-электролитный баланс. С помощью капельницы от похмелья можно быстро справиться с интоксикацией, восполнить недостающие элементы и облегчить состояние пациента. В клинике «Частный медик 24» в Самаре мы предлагаем капельницы, которые помогают снять все неприятные симптомы похмелья, восстанавливая работу организма и минимизируя риски для здоровья.
Выяснить больше – капельница от похмелья вызов на дом
нарколог на дом нарколог на дом .
нарколог вывод из запоя в стационаре нарколог вывод из запоя в стационаре .
вызов нарколога на дом цена вызов нарколога на дом цена .
вывод из запоя телефон вывод из запоя телефон .
нарколог на дом круглосуточно москва цены нарколог на дом круглосуточно москва цены .
best muscle steroid
References:
https://yogicentral.science/wiki/7_best_sites_to_buy_testosterone_online_in_2025_New_York_Post
элитная мебель на заказ изготовление мебели из массива на заказ
Капельница от похмелья применяется в тех случаях, когда человек ощущает сильное недомогание после употребления алкоголя. Основные симптомы, при которых рекомендуется лечение капельницей, включают:
Исследовать вопрос подробнее – капельница от похмелья цена в самаре
Нарколог на дом в Самаре с выездом специалиста, детоксикацией и анонимной медицинской помощью в наркологической клинике «Частный медик 24»
Получить дополнительные сведения – запой нарколог на дом в самаре
выведение запоя на дому цена vyvod-iz-zapoya-na-domu-samara-16.ru .
врач нарколог на дом narkolog-na-dom-moskva-4.ru .
https://zakynthoscarhub.com
вывод из запоя стационарно спб vyvod-iz-zapoya-v-staczionare-sankt-peterburg-1.ru .
Нарколог на дом — это услуга, которая позволяет получить медицинскую помощь в комфортной и привычной обстановке, не выходя из дома. В наркологической клинике «Частный медик 24» в Самаре мы предоставляем профессиональную помощь нарколога прямо на дому. Это идеальное решение для тех, кто испытывает симптомы абстиненции, ломки или алкогольной интоксикации, но не может или не хочет ехать в клинику. Выезд врача на дом позволяет начать лечение сразу, без задержек, минимизируя стрессы и сложности, связанные с поездкой.
Разобраться лучше – врач нарколог на дом самара
Такие симптомы важны не только сами по себе. Они показывают, что организму уже трудно поддерживать стабильность без медицинского вмешательства. Чем дольше в этот момент ждать, тем выше вероятность, что потребуется более жёсткий формат оказания помощи. Поэтому экстренное обращение в некоторых случаях не просто облегчает состояние, а предотвращает дальнейшее ухудшение здоровья.
Изучить вопрос глубже – http://www.domen.ru
После употребления алкоголя состояние может быстро ухудшиться: появляется головная боль, тошнота, головокружение и слабость. Это следствие того, что в организме накапливаются токсины, продукты распада этанола и нарушается водно-электролитный баланс. С помощью капельницы от похмелья можно быстро справиться с интоксикацией, восполнить недостающие элементы и облегчить состояние пациента. В клинике «Частный медик 24» в Самаре мы предлагаем капельницы, которые помогают снять все неприятные симптомы похмелья, восстанавливая работу организма и минимизируя риски для здоровья.
Подробнее тут – капельница от похмелья анонимно
вывод из запоя с кодированием на дому vyvod-iz-zapoya-na-domu-samara-17.ru .
вывод из запоя в клинике спб vyvod-iz-zapoya-v-staczionare-sankt-peterburg-2.ru .
нарколог на дом стоимость narkolog-na-dom-moskva-3.ru .
Анонимное лечение на дому ценно ещё и тем, что снижает внутреннее сопротивление самого пациента. Для многих людей первый контакт с врачом происходит именно дома, без дороги, без ожидания, без страха чужих взглядов. Такой формат помогает начать разговор не только о снятии острых симптомов, но и о более широких вопросах: что делать после выхода из запоя, когда требуется кодирование, в каких случаях нужна реабилитация, а когда первичная наркологическая помощь уже должна переходить в полноценный лечебный маршрут. Врач может помочь и в ситуациях, связанных не только с алкоголем, но и с наркомании, если семье нужно понять, что происходит с зависимым человеком и какой следующий шаг будет для него безопасным.
Детальнее – вызов нарколога на дом в воронеже
Ориентация на изготовление кухонной мебели с таким расчетом, чтобы соединить воедино знаменитый итальянский стиль, качество и дизайн с современными требованиями эргономики и функциональности https://www.legnostyle.ru/odnomarshevye-lestnicy.html
Достоинства мебели, представленной в салонах , несомненно, отметит тот, кто обладает тонким благородным вкусом и ценит совокупность стильного дизайна и необычайного комфорта https://www.legnostyle.ru/catalog/mebel/iz-duba/?PAGEN_1=16
Такой вид отделки мебели существует очень давно, наши предки использовали кожу в разных целях и для оббивки мебели тоже https://www.legnostyle.ru/catalog/lestnici/derevannie-vintovie-lestnici/lestnica-l4-4.html
На сегодняшний день это больше чем просто элемент декора https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/mejkomnatnie-arki-i-portali/arka-a11.html
Это, в каком-то роде, особая философия, способная даже перерасти в будущем в отдельное стилевое решение https://www.legnostyle.ru/catalog/lestnici/elitnye/lestnica-l1-10.html
Китайская мебель имеет различные показатели качества https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/nestandarnye/dver-p19.html
Многое зависит от фабрики, которая производит мебель, и от условий заказчика, который сотрудничает с данной фабрикой https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/vhodnaa-dver-e5.html
Поэтому Вам нужно хорошо сформулировать свои требования к производству мебели, которая Вам необходима https://www.legnostyle.ru/catalog/lestnici/lestnica-l8-2.html
На протяжении многих лет качественная мебель из дерева высоко ценится покупателями всего мира https://www.legnostyle.ru/catalog/mebel/derevyannye-stoly/stol-model-s-11.html
Мебель из ценных пород отличается безупречным внешним видом и исключительной надежностью https://www.legnostyle.ru/catalog/mebel/komodi-i-tualetnie-stoliki-ot-15-000-rub/?PAGEN_1=3
Салон элитной мебели готов предложить изысканную импортную мебель для гостиных, спален, кабинетов, библиотек, детских комнат, прихожих и столовых https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/vhodnaya-dver-e2.html
Эксклюзивная немецкая мебель в Москве по доступным ценам – это стильная и комфортная мебель-Германия https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/iz-massiva/?PAGEN_1=2
Мы предлагаем , , , и , , и , , то есть полный интерьер Вашего дома с гарантированным сочетанием натуральных материалов и в идеальной цветовой гармонии, при комплектации на разных фабриках https://www.legnostyle.ru/mebel-dlia-prihojei.html
Нарколог на дом может помочь в следующих ситуациях:
Подробнее тут – https://narkolog-na-dom-samara-1.ru/
Капельница от похмелья применяется, когда симптомы интоксикации становятся выраженными и мешают нормальной жизнедеятельности пациента. Основные показания для использования капельницы включают:
Углубиться в тему – http://kapelnicza-ot-pokhmelya-samara-1.ru/
Актуальні новини https://lentalife.com поради та історії з усього світу. Дізнавайтеся про події, тренди й корисні лайфхаки, щоб залишатися в курсі та робити життя простішим і зручнішим щодня.
Авто портал https://tvregion.com.ua новости, обзоры и тест-драйвы автомобилей. Актуальная информация о новых моделях, технологиях и рынке. Узнавайте все о машинах и выбирайте авто с удобным сервисом.
Авто портал https://autoguide.kyiv.ua свежие новости, обзоры и тест-драйвы. Рейтинги автомобилей, советы по выбору и актуальные предложения. Все о мире авто в одном месте.
вывод из запоя на дому самара цены вывод из запоя на дому самара цены .
наркология вывод из запоя vyvod-iz-zapoya-na-domu-samara-18.ru .
нарколог на дом в москве похмельная служба narkolog-na-dom-moskva-4.ru .
Авто журнал https://psncodegeneratormiu.org новости, обзоры и тест-драйвы автомобилей. Узнавайте о новых моделях, технологиях и рынке. Полезные советы, рейтинги и аналитика для автолюбителей.
нарколог на дом вывод из запоя нарколог на дом вывод из запоя .
вывод из запоя анонимно вывод из запоя анонимно .
вывод из запоя на дому в екатеринбурге вывод из запоя на дому в екатеринбурге .
вывод из запоя на дому самара круглосуточно вывод из запоя на дому самара круглосуточно .
TATTOOMOSCOW 18+
Добро пожаловать в один из лучших салонов тату в Москве – студию «Классик» https://maze.tattoo/catalog/e/edinorog/
Наши мастера воплотят в реальность любую вашу идею татуировки, гарантировав абсолютную стерильность и максимальный комфорт https://maze.tattoo/catalog/o/oven/
Каждая студия татуировки в Москве — это отражение своего времени https://maze.tattoo/catalog/p/parnye-tatuirovki/
Мы верим, что татуировка — это не просто тренд, а форма личной свободы https://maze.tattoo/catalog/o/
В нашей студии татуировки нет шаблонов и клише https://maze.tattoo/catalog/g/
Только вы, ваша история и мастер, который умеет слушать https://maze.tattoo/catalog/p/pesochnye-chasy/
ТАТУИРОВКА Мы сочетаем современные методы татуировки с традиционными!
Парные татуировки https://maze.tattoo/catalog/d/dzhordano-bruno/
Один из самых старейших тату салонов Москвы Команда мастеров с международным опытом Индивидуальные эскизы под каждую идею Безопасность, стерильность, комфорт https://maze.tattoo/catalog/с/spina/
Хотите узнать больше?
Сотрудничество с Дизайнерским домом Татьяны Тягиной позволяет сделать бизнес-процессы более простыми и удобными, а также способствует росту доходов https://norsy.ru/pochemu-my
Мы не подводим своих заказчиков и отвечаем за свои слова и действия!
Производство, приобретение, хранение, перевозка в целях сбыта или сбыт товаров и продукции без маркировки и (или) нанесения информации, предусмотренной законодательством Российской Федерации, наказываются штрафом в размере до трехсот тысяч рублей либо принудительными работами на срок до трех лет , либо лишением свободы на срок до трех лет со штрафом в размере до восьмидесяти тысяч рублей https://norsy.ru/voprosy-otvety
Почему вам стоит заказать услуги швейного производства в «Амадей Принт»?
Если вы ищете пошив одежды оптом, то наш Дизайнерский дом – именно то, что требуется https://norsy.ru/kontakty
© 2014-2024 poshiv365 https://norsy.ru/o-nas
ru https://norsy.ru/o-nas
Авто журнал https://nmiu.org.ua свежие автомобильные новости, тесты и обзоры. Рейтинги, сравнения и рекомендации по выбору авто. Все о мире автомобилей в одном месте.
Авто портал https://retell.info обзоры автомобилей, тест-драйвы и новости рынка. Сравнения моделей, рейтинги и советы по выбору авто для любых задач.
В этом обзорном материале представлены увлекательные детали, которые находят отражение в различных аспектах жизни. Мы исследуем непонятные и интересные моменты, позволяя читателю увидеть картину целиком. Погрузитесь в мир знаний и удивительных открытий!
Подробнее можно узнать тут – https://vivod-iz-zapoya-2.ru/
выведение из запоя на дому выведение из запоя на дому .
Авто журнал https://bestauto.kyiv.ua тест-драйвы, обзоры и новости автоиндустрии. Узнавайте о новинках, технологиях и трендах рынка. Удобный формат для чтения каждый день.
Онлайн авто журнал https://simpsonsua.com.ua новости, обзоры и тест-драйвы автомобилей. Актуальная информация о рынке и новых моделях для автолюбителей.
References:
Neosurf deposit at rocketplay casino
References:
https://pad.stuve.de/s/l6zYRmwdi
выведения из запоя на дому круглосуточно выведения из запоя на дому круглосуточно .
вывод из запоя на дому недорого вывод из запоя на дому недорого .
Авто журнал онлайн https://translit.com.ua все о машинах: новости, тесты, обзоры и аналитика. Следите за новинками и выбирайте авто с удобным сервисом.
“вывод из запоя на халтурина – лечение алкоголизма, лечение наркомании “вывод из запоя на халтурина – лечение алкоголизма, лечение наркомании .
вывести из запоя екатеринбург вывести из запоя екатеринбург .
Автомобильный журнал https://mirauto.kyiv.ua новости, обзоры и тесты автомобилей. Советы по выбору, рейтинги и аналитика. Все о машинах и рынке авто.
вызов нарколога на дом вывод из запоя вызов нарколога на дом вывод из запоя .
Авто портал https://nerjalivingspace.com автомобильные новости, тест-драйвы и обзоры. Узнавайте о новинках, технологиях и тенденциях рынка. Удобный сервис для автолюбителей.
вывод из запоя вызов на дом vyvod-iz-zapoya-na-domu-ekaterinburg-11.ru .
References:
Did arnold take steroids
References:
https://hack.allmende.io/s/dOkJuWOG4
Предлагаем вашему вниманию интересную справочную статью, в которой собраны ключевые моменты и нюансы по актуальным вопросам. Эта информация будет полезна как для профессионалов, так и для тех, кто только начинает изучать тему. Узнайте ответы на важные вопросы и расширьте свои знания!
Детальнее – https://vivod-iz-zapoya-2.ru/
Все подробности по ссылке: https://zhukovastudio.ru
вывод из запоя с кодированием на дому vyvod-iz-zapoya-na-domu-samara-18.ru .
вывод из запоя цена вывод из запоя цена .
капельница от похмелья услуги капельница от похмелья услуги .
капельница от похмелья воронеж капельница от похмелья воронеж .
вывод из запоя с выездом на дом цена вывод из запоя с выездом на дом цена .
вывод из запоя врач на дом vyvod-iz-zapoya-na-domu-ekaterinburg-9.ru .
Состояние пациента при интоксикации может развиваться по-разному: от умеренной слабости и головной боли до выраженной дезориентации, тахикардии и нарушений сна. В таких ситуациях важно не откладывать обращение за помощью. Наркологическая помощь на дому рассматривается, когда требуется быстрое вмешательство и контроль состояния без транспортировки пациента.
Узнать больше – круглосуточная наркологическая помощь в нижнем новгороде
К основным показаниям относятся:
Ознакомиться с деталями – http://vyvod-iz-zapoya-na-domu-sankt-peterburg-8.ru
Запой сопровождается интоксикацией, нарушением сна, слабостью, тревожностью и нестабильностью работы сердечно-сосудистой системы, что характерно для алкоголизма и других форм зависимости, включая наркомании. При этом самостоятельный выход из состояния может сопровождаться усилением симптомов, что требует медицинского вмешательства. Капельницы на дому позволяют очень быстро снизить выраженность проявлений и начать восстановление под наблюдением врача, помогая человеку стабилизировать состояние.
Разобраться лучше – http://vyvod-iz-zapoya-na-domu-sankt-peterburg-11.ru/
Срочный домашний выезд особенно важен для семей, которые уже сталкивались с тяжёлыми последствиями алкоголизма и понимают, что обычные попытки «отпаивания» не решают проблему. Врач оценивает не только факт употребления, но и длительность запоя, возраст, наличие хронических болезней, уже принятые медикаменты, риск абстинентного синдрома, состояние сердца и общую нагрузку на организм. Такой формат позволяет анонимно вызвать специалиста, быстро провести необходимые вмешательства и определить, нужен ли только домашний вывод из острого состояния или дальше потребуется кодирование, повторная консультация, реабилитация либо более широкий маршрут помощи при наркомании.
Подробнее – вызвать нарколога на дом воронеж
лечение запоя vyvod-iz-zapoya-na-domu-samara-19.ru .
Состояние пациента при интоксикации может развиваться по-разному: от умеренной слабости и головной боли до выраженной дезориентации, тахикардии и нарушений сна. В таких ситуациях важно не откладывать обращение за помощью. Наркологическая помощь на дому рассматривается, когда требуется быстрое вмешательство и контроль состояния без транспортировки пациента.
Изучить вопрос глубже – скорая наркологическая помощь в нижнем новгороде
Выезд нарколога начинается с осмотра пациента. Доктора измеряют давление, пульс, оценивают уровень сознания и выраженность симптомов. На основании этих данных формируется план лечения, который реализуется сразу на месте. Такой подход позволяет быстро перейти к стабилизации состояния без лишних этапов.
Получить дополнительные сведения – вывод из запоя на дому круглосуточно санкт-петербург
Последние изменения: https://reklamig.ru
В Санкт-Петербурге вывод из запоя на дому используется в ситуациях, когда состояние пациента требует медицинской помощи, но позволяет обойтись без лечения в стационаре. Врач проводит консультацию, оценивает длительность запоя, выраженность симптомов и общее состояние, анализируя данные пациента, после чего принимает решение о тактике лечения при алкоголизме. При необходимости можно оформить вызов специалиста или заказать услугу заранее.
Подробнее тут – анонимный вывод из запоя на дому санкт-петербург
снятие алкогольной интоксикации на дому vyvod-iz-zapoya-na-domu-samara-18.ru .
вывести из запоя цена вывести из запоя цена .
Нарколог на дом — это услуга, которая позволяет получить медицинскую помощь в комфортной и привычной обстановке, не выходя из дома. В наркологической клинике «Частный медик 24» в Самаре мы предоставляем профессиональную помощь нарколога прямо на дому. Это идеальное решение для тех, кто испытывает симптомы абстиненции, ломки или алкогольной интоксикации, но не может или не хочет ехать в клинику. Выезд врача на дом позволяет начать лечение сразу, без задержек, минимизируя стрессы и сложности, связанные с поездкой.
Ознакомиться с деталями – запой нарколог на дом самара
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
капельница после похмелья капельница после похмелья .
Наша лучшая подборка: https://trafficforsimilarweb.com
Необходимость обращения за наркологической помощью определяется по совокупности симптомов и их выраженности. При ухудшении состояния важно ориентироваться на объективные признаки, а не ждать самостоятельного улучшения.
Углубиться в тему – narkologicheskaya-pomoshh-nizhnij-novgorod-8.ru/
Ключевым преимуществом вызова нарколога на дом является то, что лечение начинается в тот момент, когда оно особенно необходимо. Близкие пациента не должны волноваться о поиске клиники или медицинских центров в экстренной ситуации — помощь будет оказана немедленно, с минимальными затратами времени и без стресса для пациента.
Узнать больше – нарколог на дом в самаре
Такие состояния позволяют проводить лечение на дому с контролем динамики. При выявлении рисков врач может изменить тактику и рекомендовать стационар или другие методы лечения зависимости.
Получить дополнительную информацию – вывод из запоя на дому анонимно
поставить капельницу от запоя на дому поставить капельницу от запоя на дому .
Выезд врача начинается с оценки состояния пациента. Доктора измеряют давление, пульс, оценивают уровень сознания и выраженность симптомов. После этого формируется план лечения, который реализуется сразу. Такой подход позволяет быстро перейти к стабилизации состояния человека.
Изучить вопрос глубже – анонимный вывод из запоя на дому
Нарколог на дом в Воронеже с оперативным приездом специалиста, детоксикацией и медицинским наблюдением в наркологической клинике «Частный медик 24»
Подробнее тут – нарколог на дом вывод
Анонимное лечение на дому ценно ещё и тем, что снижает внутреннее сопротивление самого пациента. Для многих людей первый контакт с врачом происходит именно дома, без дороги, без ожидания, без страха чужих взглядов. Такой формат помогает начать разговор не только о снятии острых симптомов, но и о более широких вопросах: что делать после выхода из запоя, когда требуется кодирование, в каких случаях нужна реабилитация, а когда первичная наркологическая помощь уже должна переходить в полноценный лечебный маршрут. Врач может помочь и в ситуациях, связанных не только с алкоголем, но и с наркомании, если семье нужно понять, что происходит с зависимым человеком и какой следующий шаг будет для него безопасным.
Подробнее – запой нарколог на дом в воронеже
Нарколог на дом в Воронеже с оперативным приездом специалиста, детоксикацией и медицинским наблюдением в наркологической клинике «Частный медик 24»
Углубиться в тему – врач нарколог на дом
вывод из запоя на дому екатеринбург вывод из запоя на дому екатеринбург .
Также диагностику помогут провести специальные утилиты:
Такое соединение применяется при необходимости безопасного удаленного подключения к частным сетям, повышения приватности https://magic.net.ru/docs/
Кабель заводят в помещение и подключают к маршрутизатору, от которого затем и будет идти сигнал https://magic.net.ru/news/no-news_tax/skidka-na-podkljuchenie-pri-pereezde/
Монтажник должен настроить интернет и протестировать, есть ли связь https://magic.net.ru/news/no-news_tax/vazhnaja-informacija/
Рекомендуется установить на роутер пароль, иначе к сети смогут подключаться все, без исключения https://magic.net.ru/blog/kak-vzlomat-algoritmy-socsetej-i-videt-tolko-neobhodimoe/
Раздача интернета с компьютера производится и через Wi-Fi https://magic.net.ru/news/akcii/podkljuchaj-svoih-druzej-k-nashemu-inter/
Для этого нужно выполнить несколько шагов https://magic.net.ru/blog/kak-internet-vlijaet-na-myshlenie-uskorjaet-ili-zamedljaet-nas/
Мы запускаем обновленный сайт и нам важно Ваше мнение!
Иногда бывает так, что все действия проделаны правильно, но интернета нет https://magic.net.ru/connect/
В этом случае:
Для Воронежа выездной формат особенно востребован вечером, ночью и ранним утром, когда у больного резко усиливаются симптомы и поездка в медицинское учреждение становится тяжёлой или просто нереальной. Если человек несколько дней употреблял алкоголь, почти не спал, плохо переносит воду, жалуется на сердцебиение и слабость, то откладывать осмотр не стоит. Срочная наркологическая помощь нужна именно тогда, когда ситуация развивается быстро, а семья уже видит, что своими силами справиться не удаётся. Врач приезжает, проводит осмотр, определяет, нет ли признаков осложнений, и уже на месте решает, какие меры допустимы дома, а какие требуют другого формата оказания помощи.
Получить больше информации – нарколог на дом анонимно
В Воронеже услуга «нарколог на дом» востребована прежде всего тогда, когда состояние развивается быстро, а запас сил у пациента почти исчерпан. После нескольких дней употребления человеку бывает трудно даже выйти из квартиры: сохраняются слабость, дрожь, бессонница, тошнота, скачки давления, потливость, раздражительность и ощущение, что без новой дозы алкоголя легче уже не станет. Именно в этот момент домашний выезд специалиста помогает разорвать опасный цикл. Наркологическая помощь начинается там, где человек находится, а не там, куда он в идеале должен был бы доехать.
Получить больше информации – вызов нарколога на дом в воронеже
Вывод из запоя на дому — это формат медицинской помощи, при котором лечение проводится в привычной для пациента обстановке с выездом нарколога. Такой подход используется, когда требуется срочное вмешательство, но состояние позволяет обойтись без госпитализации. В наркологической клинике «Частный медик 24» помощь оказывается круглосуточно, с возможностью начать терапию сразу после обращения и без ожидания.
Узнать больше – нарколог на дом вывод из запоя в санкт-петербурге
капельница от алкоголя на дому воронеж недорого капельница от алкоголя на дому воронеж недорого .
Нарколог на дом может помочь в следующих ситуациях:
Исследовать вопрос подробнее – нарколог на дом анонимно самара
вывод из запоя круглосуточно вывод из запоя круглосуточно .
Такие состояния требуют профессионального вмешательства, так как без лечения могут усиливаться и приводить к ухудшению самочувствия. При этом помощь может предоставляться анонимно, в соответствии с политикой конфиденциальности данных пациента.
Подробнее – вывод из запоя на дому санкт-петербург
Строительный портал https://zip.org.ua все для ремонта и строительства в одном месте. Актуальные статьи, советы экспертов, обзоры материалов и технологий. Найдите подрядчиков, сравните цены и выберите лучшие решения для дома, квартиры или бизнеса быстро и удобно.
Женский портал https://muz-hoz.com.ua мода, красота, здоровье и психология. Советы, тренды и полезные статьи для современной женщины. Удобный онлайн формат для ежедневного чтения.
капельница на дому от алкоголя воронеж цена капельница на дому от алкоголя воронеж цена .
выведение из запоя капельница выведение из запоя капельница .
Женский портал https://lubimoy.com.ua статьи о красоте, здоровье, отношениях и саморазвитии. Полезные советы, лайфхаки и актуальные темы для женщин. Все для вдохновения и гармонии каждый день.
эссенциале капельница в воронеже эссенциале капельница в воронеже .
капельница от похмелья клиника капельница от похмелья клиника .
прокапать от алкоголя прокапать от алкоголя .
вызвать на дом капельницу от алкоголя вызвать на дом капельницу от алкоголя .
Удобный строительный https://anti-orange.com.ua портал с полезной информацией для частных застройщиков и профессионалов. Обзоры, инструкции, идеи для ремонта, каталог услуг и материалов. Поможем спланировать проект, подобрать решения и реализовать строительство без лишних затрат.
вывод из запоя екатеринбург стационар вывод из запоя екатеринбург стационар .
клиники по лечению алкоголизма narkologicheskaya-pomoshh-nizhnij-novgorod.ru .
капельница от запоя вызов капельница от запоя вызов .
Мужской портал https://swiss-watches.com.ua о стиле жизни, здоровье, финансах и саморазвитии. Полезные статьи, советы экспертов, идеи для карьеры и отдыха. Всё, что важно современному мужчине для уверенности, успеха и баланса в жизни.
Онлайн женский портал https://sweaterok.com.ua мода, уход за собой, здоровье и отношения. Актуальные статьи, советы и идеи для вдохновения и улучшения качества жизни.
Туристический портал https://swiss-watches.com.ua для путешественников: направления, маршруты, советы и лайфхаки. Подбор отелей, билетов и экскурсий, идеи для отдыха и полезные рекомендации. Планируйте поездки легко и открывайте новые страны с комфортом.
Все о беременности https://z-b-r.org и родах: полезные статьи, советы врачей и ответы на важные вопросы. Подготовка к родам, развитие малыша по неделям, здоровье мамы и восстановление. Надежная информация для будущих родителей на каждом этапе.
наркологическая клиника нижний новгород наркологическая клиника нижний новгород .
black ops market url https://darknetmarketstore.com/
Запрос на выезд врача связан не только с классическим запоем. На практике домашняя помощь нужна в разных ситуациях, когда организму уже трудно компенсировать последствия употребления, а откладывание визита увеличивает риск осложнений.
Исследовать вопрос подробнее – http://narkolog-na-dom-voronezh-2.ru/
Современный строительный https://sinergibumn.com журнал: идеи, технологии, обзоры и советы экспертов. Помогаем разобраться в материалах, выбрать решения и реализовать проекты любой сложности — от квартиры до загородного дома.
Профессиональный строительный https://newhouse.kyiv.ua журнал с полезной информацией и практическими решениями. Аналитика рынка, обзоры материалов, инструкции и советы. Всё, что нужно для качественного строительства и ремонта.
Портал о дизайне https://lbook.com.ua интерьера: идеи, тренды и практические решения для дома и квартиры. Обзоры стилей, подбор мебели и материалов, советы дизайнеров. Помогаем создать уютное, функциональное и современное пространство.
Строительный портал https://comart.com.ua для тех, кто ценит качество и надежность. Полезные статьи, инструкции, сравнение материалов и услуг. Найдите проверенных специалистов, получите идеи для ремонта и реализуйте проекты любой сложности с максимальной выгодой.
продажа базы gobasego-2.ru .
Женский сайт https://biglib.com.ua мода, уход за собой, психология и здоровье. Актуальные темы, лайфхаки и рекомендации для улучшения качества жизни.
Информационный строительный https://stroyportal.kyiv.ua журнал с экспертным контентом. Технологии, материалы, тренды и советы для частных и коммерческих проектов. Читайте, вдохновляйтесь и реализуйте идеи с уверенностью в результате.
Строительный журнал https://ukrainianpages.com.ua с актуальными новостями, трендами и экспертными материалами. Обзоры технологий, советы по ремонту и строительству, идеи для дома и бизнеса. Узнавайте о современных решениях и применяйте лучшие практики в своих проектах.
капельница от похмелья екатеринбург капельница от похмелья екатеринбург .
вывод из запоя на дому воронеж капельница вывод из запоя на дому воронеж капельница .
капельница от похмелья воронеж капельница от похмелья воронеж .
вывод из запоя с выездом вывод из запоя с выездом .
сколько стоит вывод из запоя сколько стоит вывод из запоя .
капельница от алкоголя в воронеже kapelnicza-ot-zapoya-voronezh-1.ru .
Женский портал https://virginvirtual.net красота, здоровье, психология и стиль жизни. Полезные советы, тренды и рекомендации для женщин в одном месте.
Женский журнал https://vybir.kiev.ua статьи о моде, красоте, здоровье и отношениях. Актуальные тренды, советы экспертов и вдохновение для современной женщины каждый день.
Все о строительстве https://azst.com.ua и ремонте на одном портале: от выбора материалов до поиска исполнителей. Практические советы, тренды, технологии и реальные кейсы. Экономьте время и деньги, принимая грамотные решения для вашего дома или коммерческого объекта.
Свежие новости https://hansaray.org.ua Украины: политика, экономика, общество и события дня. Оперативная информация, аналитика и мнения экспертов. Будьте в курсе главных новостей страны и мира в удобном формате.
капельница от запоя екатеринбург капельница от запоя екатеринбург .
лечение алкоголизма в нижнем новгороде narkologicheskaya-pomoshh-nizhnij-novgorod.ru .
от 5380 руб/час https://rentbusspb.ru/prokat-bmv-7/
Одной из популярных услуг является прокат автомобилей на свадьбу, свадебные мероприятия и деловые поездки клиентов по городу https://rentbusspb.ru/arenda-mercedes-e212-restyling-black-s-voditelem/
Как правило, заказ направлен на автомобили бизнес класса https://rentbusspb.ru/arenda-microavtobusa-new-luxury-mercedes-sprinter-vip-white/
К сожалению, в прокате отсутствуют такие автомобили как, лимузины, микроавтобусы и автобусы https://rentbusspb.ru/mercedes-maybach-long-s-223/
Компания «Рента-Кар Красноярск» уже 17 лет является лидером на рынке проката автомобилей г https://rentbusspb.ru/arenda-mercedes-s-class-w222-white-s-voditelem/
Красноярска https://rentbusspb.ru/mercedes-benz-gelandewagen/
г https://rentbusspb.ru/avtopark-transporta-dlya-arendi/
Иркутск, ул https://rentbusspb.ru/category/arenda-avtobusa/
Ширямова, 2 https://rentbusspb.ru/mercedes-benz-gelandewagen/
от 2610 руб/час https://rentbusspb.ru/arenda-mercedes-s-class-w223-s-voditelem/
Ищете, где взять авто напрокат в Иркутске? Звоните в компанию “Авеню” – поиск подходящей машины не займёт более 10 секунд на нашем сайте, а на заключение договора нужно всего 15 минут https://rentbusspb.ru/range-rover/
Прокат авто в Иркутске в компании “Авеню” – это быстрый способ получить мобильность https://rentbusspb.ru/arenda-avtomobilya-chevrolet-camaro-s-voditelem/
Все о здоровье https://mikstur.com на одном портале: болезни, симптомы, методы лечения и профилактика. Советы врачей, актуальные медицинские статьи и рекомендации. Помогаем лучше понимать организм и заботиться о своем самочувствии.
Сайт для женщин https://prowoman.kyiv.ua практичные советы по уходу за собой, здоровью и отношениям. Читайте, развивайтесь и улучшайте свою жизнь.
Женский онлайн журнал https://whoiswho.com.ua стиль, красота и здоровье. Полезные советы, лайфхаки и актуальные темы для женщин. Все о жизни, моде и саморазвитии.
тестовая база gobasego-2.ru .
лечение алкогольной зависимости нижний новгород лечение алкогольной зависимости нижний новгород .
Женский журнал https://womanclub.in.ua мода, уход за собой, психология и отношения. Читайте интересные статьи, находите идеи и улучшайте качество жизни.
Все о строительстве https://skol.if.ua ремонте и отделке на одном сайте. Практические рекомендации, современные технологии, обзоры и каталог услуг. Найдите идеи, рассчитайте бюджет и воплотите проект любой сложности с минимальными рисками и затратами.
Новости Украины https://status.net.ua сегодня: главные события, политика, экономика и общественная жизнь. Оперативные сводки, аналитика и комментарии. Узнавайте важное первыми и следите за развитием ситуации.
Портал о строительстве https://kennan.kiev.ua и ремонте: идеи, технологии, обзоры и советы экспертов. Помогаем выбрать материалы, рассчитать бюджет и найти исполнителей. Удобный сервис для планирования и реализации проектов — от квартиры до загородного дома.
капельница от алкоголя на дому kapelnicza-ot-pokhmelya-ekaterinburg-1.ru .
капельница от алкоголя в воронеже kapelnicza-ot-zapoya-voronezh.ru .
вывод из запоя вывод из запоя .
выведение из запоя выведение из запоя .
Капельница от похмелья в Самаре с подбором препаратов, улучшением самочувствия и наблюдением в наркологической клинике «Частный медик 24»
Подробнее можно узнать тут – капельница от похмелья на дому в самаре
наркология нижний новгород наркология нижний новгород .
вывод из запоя на дому воронеж капельница вывод из запоя на дому воронеж капельница .
капсульный дом цена в россии капсульный дом цена в россии .
Комплексное лечение в наркологическом стационаре включает несколько последовательных этапов, каждый из которых направлен на решение конкретных задач. Начальный этап включает в себя медицинское вмешательство, направленное на устранение токсинов из организма, и стабилизацию общего состояния пациента. Далее начинается реабилитация, которая помогает закрепить достигнутые результаты и восстановить психоэмоциональное состояние пациента. Для выбора подходящего стационара стоит ознакомиться с отзывами и дополнительной информацией о клинике, а также уточнить, в каком районе города она расположена.
Получить дополнительные сведения – narkologicheskij-staczionar-sankt-peterburg-1.ru/
Существует ряд ситуаций, при которых вызов специалиста на дом является обоснованным решением:
Подробнее – нарколог на дом анонимно в нижнем новгороде
купить данные купить данные .
Наркологический стационар — это специализированное медицинское учреждение, предназначенное для лечения и реабилитации пациентов с зависимостью от алкоголя, наркотиков и других психоактивных веществ. В Санкт-Петербурге существует множество таких учреждений, которые предоставляют комплексную помощь людям, страдающим от зависимости. Лечение в стационаре часто является первым шагом на пути к выздоровлению, особенно в случаях тяжелых зависимостей, когда амбулаторное лечение может не дать должного эффекта. В случае запоя или хронического алкоголизма стационарное лечение может стать необходимым, особенно если выезд на дом не позволяет должным образом контролировать процесс восстановления.
Разобраться лучше – лечение в наркологическом стационаре санкт-петербург
Капельница от похмелья в Екатеринбурге с инфузионной терапией и быстрым облегчением симптомов в наркологической клинике «Частный медик 24»
Получить дополнительную информацию – http://kapelnicza-ot-pokhmelya-ekaterinburg-7.ru
вызвать на дом капельницу от алкоголя вызвать на дом капельницу от алкоголя .
капельница от похмелья клиника капельница от похмелья клиника .
Комплексное лечение в наркологическом стационаре включает несколько последовательных этапов, каждый из которых направлен на решение конкретных задач. Начальный этап включает в себя медицинское вмешательство, направленное на устранение токсинов из организма, и стабилизацию общего состояния пациента. Далее начинается реабилитация, которая помогает закрепить достигнутые результаты и восстановить психоэмоциональное состояние пациента. Для выбора подходящего стационара стоит ознакомиться с отзывами и дополнительной информацией о клинике, а также уточнить, в каком районе города она расположена.
Углубиться в тему – частный наркологический стационар
В таких ситуациях врач оценивает риски, определяет тактику лечения и при необходимости рекомендует дальнейшую госпитализацию. Однако во многих случаях помощь на дому оказывается достаточной для стабилизации состояния.
Исследовать вопрос подробнее – вызвать нарколога на дом
Работа с пациентами в наркологическом стационаре начинается с диагностики, которая помогает определить степень зависимости и сопутствующие заболевания. На основе этих данных разрабатывается индивидуальный план лечения. Врачи, наркологи и психотерапевты работают в тесном контакте с пациентом, что позволяет достичь наилучших результатов в процессе восстановления. Важно также убедиться, что клиника имеет необходимую лицензию, а для эффективного лечения могут быть предложены такие процедуры, как прием психотерапевта и кодирование от зависимости.
Изучить вопрос глубже – наркологический стационар в санкт-петербурге
Капельница от похмелья — это не просто средство для снятия симптомов, но и эффективный способ быстрого восстановления организма после алкогольной интоксикации. В наркологической клинике «Частный медик 24» в Екатеринбурге мы предоставляем услугу выезда нарколога на дом, что позволяет пациентам получить необходимую медицинскую помощь, не покидая комфорт своей обстановки. Это особенно важно в случае, если состояние пациента серьёзно ухудшилось, и он не может поехать в клинику самостоятельно.
Разобраться лучше – капельница от похмелья на дом екатеринбург
сколько стоит вывод из запоя сколько стоит вывод из запоя .
нарколог нижний новгород нарколог нижний новгород .
Капельница от похмелья — это медицинская процедура, направленная на быстрое восстановление организма после алкогольной интоксикации. Она помогает устранить обезвоживание, нормализовать обменные процессы и снизить токсическую нагрузку на внутренние органы. В отличие от домашних методов, инфузионная терапия действует напрямую через кровоток, обеспечивая более быстрый и выраженный эффект.
Подробнее – капельница от похмелья анонимно в самаре
капельница от запоя недорого капельница от запоя недорого .
Обращение в наркологический стационар в Санкт-Петербурге может стать важным шагом для людей, страдающих от алкогольной или наркотической зависимости. Стационарное лечение предоставляет пациентам не только медицинскую помощь, но и психологическую поддержку, необходимую для успешной реабилитации. Это подход, ориентированный на комплексное восстановление здоровья, физическое и психоэмоциональное состояние пациента.
Получить больше информации – narkologicheskij-staczionar-sankt-peterburg-2.ru/
Процесс лечения начинается с консультации врача, который оценивает состояние пациента, его анамнез и определяет, какие процедуры и препараты нужно использовать. В большинстве случаев капельница включает в себя регидратацию, витамины группы B, антиеметики, препараты для улучшения работы печени и почек. Важно, что капельница не только помогает организму вывести токсины, но и восстанавливает нормальную работу всех систем организма, обеспечивая быстрое улучшение самочувствия.
Узнать больше – капельница от похмелья анонимно
Продолжительность процедуры капельницы от похмелья зависит от степени интоксикации, общего состояния пациента и состава вводимых препаратов. В среднем инфузионная терапия занимает от 40 минут до 1,5 часов. Уже во время введения растворов многие пациенты отмечают постепенное улучшение самочувствия.
Разобраться лучше – капельница от похмелья анонимно
Комплексное лечение в наркологическом стационаре включает несколько последовательных этапов, каждый из которых направлен на решение конкретных задач. Начальный этап включает в себя медицинское вмешательство, направленное на устранение токсинов из организма, и стабилизацию общего состояния пациента. Далее начинается реабилитация, которая помогает закрепить достигнутые результаты и восстановить психоэмоциональное состояние пациента. Для выбора подходящего стационара стоит ознакомиться с отзывами и дополнительной информацией о клинике, а также уточнить, в каком районе города она расположена.
Углубиться в тему – лечение в наркологическом стационаре санкт-петербург
После оформления вызова нарколог приезжает к пациенту и проводит комплексную оценку состояния. Врач измеряет давление, частоту пульса, оценивает уровень сознания и выраженность симптомов. На основании полученных данных формируется план лечения, который реализуется сразу на месте.
Получить дополнительную информацию – вызвать нарколога на дом
Работа с пациентами в наркологическом стационаре начинается с диагностики, которая помогает определить степень зависимости и сопутствующие заболевания. На основе этих данных разрабатывается индивидуальный план лечения. Врачи, наркологи и психотерапевты работают в тесном контакте с пациентом, что позволяет достичь наилучших результатов в процессе восстановления. Важно также убедиться, что клиника имеет необходимую лицензию, а для эффективного лечения могут быть предложены такие процедуры, как прием психотерапевта и кодирование от зависимости.
Углубиться в тему – наркологическая помощь стационар
Когда такие симптомы становятся ярко выраженными, важно не затягивать с лечением и вызвать нарколога на дом. Это позволит своевременно устранить токсические вещества из организма и предотвратить серьёзные проблемы с органами. Важно, чтобы лечение началось как можно быстрее, что возможно только через экстренный выезд специалиста на дом.
Исследовать вопрос подробнее – kapelnicza-ot-pokhmelya-ekaterinburg-6.ru/
покупка базы покупка базы .
Капельница от похмелья в Екатеринбурге с инфузионной терапией и быстрым облегчением симптомов в наркологической клинике «Частный медик 24»
Исследовать вопрос подробнее – капельница от похмелья на дому
сколько стоит вывод из запоя сколько стоит вывод из запоя .
нарколог анонимно нижний новгород narkologicheskaya-pomoshh-nizhnij-novgorod.ru .
Капельница от похмелья в Екатеринбурге с устранением слабости, тошноты и последствий интоксикации в наркологической клинике «Частный медик 24»
Выяснить больше – капельница от похмелья анонимно в екатеринбурге
Выезд нарколога на дом позволяет быстро устранить эти симптомы, нормализовать состояние пациента и предотвратить дальнейшее ухудшение здоровья.
Исследовать вопрос подробнее – капельница от похмелья екатеринбург
Выбор наркологического стационара в Санкт-Петербурге — это важный шаг, который требует внимательного подхода. Каждое медицинское учреждение имеет свои особенности, что может влиять на качество предоставляемых услуг. Важно учитывать как репутацию клиники, так и квалификацию врачей, а также доступные методы лечения и реабилитации.
Углубиться в тему – наркологический стационар
Строительный журнал https://sota-servis.com.ua о ремонте, отделке и строительстве. Актуальные статьи, кейсы, лайфхаки и рекомендации специалистов. Будьте в курсе новинок и принимайте грамотные решения для своих проектов.
Строительный портал https://solution-ltd.com.ua с актуальной информацией и практическими решениями. Узнайте о новых технологиях, сравните материалы, получите советы и найдите специалистов. Сделайте ремонт или строительство проще, быстрее и выгоднее.
Онлайн журнал https://start.net.ua о строительстве, ремонте и дизайне. Разбор технологий, советы экспертов, обзоры материалов и реальные кейсы. Помогаем принимать грамотные решения и реализовывать проекты любой сложности без лишних затрат.
Суть капельницы заключается в том, чтобы быстро ввести в организм необходимые растворы, которые помогают восстановить водно-солевой баланс, очищают организм от токсинов, ускоряют обмен веществ и снижают нагрузку на внутренние органы. Врачи-наркологи используют специальные составы, которые включают в себя жидкости, электролиты, витамины и лекарственные средства для снятия симптомов похмелья.
Подробнее можно узнать тут – капельница от похмелья на дому
капельница от похмелья недорого капельница от похмелья недорого .
Вывод из запоя на дому — это формат наркологической помощи, при котором детоксикация и стабилизация состояния проводятся в привычной для пациента обстановке. Такой подход позволяет начать лечение без задержек и снизить нагрузку на организм, связанную с транспортировкой. В наркологической клинике «Частный медик 24» помощь организована круглосуточно: врач выезжает сразу после обращения и проводит терапию с учётом текущего состояния пациента.
Подробнее можно узнать тут – вывод из запоя на дому круглосуточно санкт-петербург
Сайт для женщин https://gracefullady.kyiv.ua все о моде, красоте, здоровье и отношениях. Практические советы, тренды и идеи для современной женщины.
Детоксикация на дому начинается с осмотра пациента. Доктора оценивают витальные показатели, уровень сознания и выраженность симптомов, анализируя текущие данные. После этого формируется план лечения, который реализуется сразу. Такой подход позволяет сократить время до начала терапии и повысить её эффективность.
Выяснить больше – нарколог на дом вывод из запоя
Продолжительность процедуры капельницы от похмелья зависит от степени интоксикации, общего состояния пациента и состава вводимых препаратов. В среднем инфузионная терапия занимает от 40 минут до 1,5 часов. Уже во время введения растворов многие пациенты отмечают постепенное улучшение самочувствия.
Получить больше информации – https://kapelnicza-ot-pokhmelya-samara-8.ru
Лучший сайт для женщин https://musicbit.com.ua статьи о стиле, любви, здоровье и вдохновении. Найдите идеи для жизни и развития в одном месте.
Онлайн сайт для женщин https://elegance.kyiv.ua статьи о красоте, отношениях, семье и саморазвитии. Советы, идеи и вдохновение для повседневной жизни.
Женский сайт https://fashionadvice.kyiv.ua полезная информация о здоровье, стиле, любви и карьере. Читайте актуальные статьи и находите решения для жизни.
капельница от похмелья на дому капельница от похмелья на дому .
Капельница от похмелья в Екатеринбурге с анонимным выездом врача и восстановительной терапией в наркологической клинике «Частный медик 24»
Выяснить больше – http://kapelnicza-ot-pokhmelya-ekaterinburg-8.ru
кодировка выезд на дом narkologicheskaya-pomoshh-nizhnij-novgorod-1.ru .
вывод из запоя врач на дом vyvod-iz-zapoya-na-domu-ekaterinburg-8.ru .
Похмельный синдром — это не просто неприятное ощущение, а целый комплекс симптомов, которые могут варьироваться от легкого дискомфорта до тяжелых состояний. Капельница от похмелья используется в случаях, когда симптомы становятся особенно выраженными и требуют вмешательства профессионала. Врачи отмечают, что капельница помогает значительно ускорить процесс восстановления организма после алкоголя, избавляя от боли, тошноты и слабости.
Ознакомиться с деталями – капельница от похмелья вызов на дом
Строительный журнал https://tozak.org.ua с полезными статьями и актуальными обзорами. Освещаем современные технологии, материалы и тренды в строительстве и ремонте. Практические советы, идеи и решения для создания комфортного и надежного пространства.
Сайт для женщин https://bestwoman.kyiv.ua статьи о красоте, здоровье, отношениях и стиле жизни. Полезные советы, тренды и идеи для вдохновения. Все, что нужно современной женщине, в одном месте.
капсульные дома для круглогодичного проживания капсульные дома для круглогодичного проживания .
При выборе наркологического стационара с комфортными условиями в Санкт-Петербурге важно учитывать несколько ключевых факторов, которые могут повлиять на успех лечения. Кроме высококвалифицированных специалистов и индивидуального подхода, комфортные условия для проживания играют важную роль в процессе восстановления пациента. Это создаёт оптимальные условия для того, чтобы человек мог сосредоточиться на своём здоровье и восстановлении, не отвлекаясь на неприятные или неудобные условия. В некоторых случаях может быть предложено кодирование, а также получение дополнительных данных и консультаций для более точного подхода к лечению.
Подробнее можно узнать тут – наркологический стационар
лечение алкоголизма в нижнем новгороде лечение алкоголизма в нижнем новгороде .
прогулка по воде санкт петербург прогулка по воде санкт петербург .
корабли в санкт петербурге сегодня где посмотреть piter-na-teplohode.ru .
частный нарколог на дом телефон narkolog-na-dom-moskva-11.ru .
вывод из запоя стационар санкт петербург вывод из запоя стационар санкт петербург .
Онлайн строительный https://reklama-region.com журнал для профессионалов и частных застройщиков. Полезные статьи, разборы материалов, новинки рынка и практические рекомендации. Все о строительстве, ремонте и дизайне в удобном формате.
Онлайн женский журнал https://zhenskiy.kyiv.ua статьи о красоте, здоровье, моде и любви. Советы, тренды и полезный контент для женщин любого возраста.
Актуальные новости https://ktm.org.ua Украины онлайн. Последние события, аналитика, экономика, происшествия и международные отношения. Только проверенная информация и важные обновления в режиме реального времени.
Эконом Хочешь 3д ограждение? панельный забор 3d прочные и надежные решения для защиты территории. Современные металлические конструкции с антикоррозийным покрытием, простым монтажом и долговечностью. Подходят для частных домов, предприятий и общественных объектов.
Эконом Лучшие металлические панели ограждения сетчатые идеальное сочетание прочности, эстетики и доступной цены. Подходят для дачи, участка, склада и промышленной территории. Быстрая установка, устойчивость к погодным условиям и долгий срок службы.
Эконом Лучшие ограждения 3 d панели для забора практичное и долговечное решение. Усиленные ребра жесткости обеспечивают прочность, а современное покрытие защищает от ржавчины. Идеально для дома, дачи, предприятий и общественных территорий.
Хочешь недорогой забор? производители ограждения 3d удобное решение для быстрого монтажа ограждения. Прочные сварные конструкции, устойчивость к нагрузкам и погоде, минимальный уход. Отличный вариант для частных и коммерческих территорий.
Высокопрочные ограждения панели ограждения сетчатые современный способ обеспечить безопасность участка. Долговечные материалы, надежная конструкция и эстетичный внешний вид. Подходят для установки на любых типах территорий и условий эксплуатации.
королев капсульные дома королев капсульные дома .
Купить панели для ограждения купить 3д панели для забора долговечность, прочность и аккуратный внешний вид. Быстрый монтаж, устойчивость к погодным условиям и минимальное обслуживание. Отличный выбор для дачи, участка или коммерческой территории.
Нужна соляная пещера? соляная пещера под ключ проектирование, подбор материалов, монтаж и оформление. Создаем уникальные пространства для галотерапии с продуманным дизайном и эффективной системой микроклимата.
капсульный дом на колесах капсульный дом на колесах .
выведение +из запоя +в стационаре vyvod-iz-zapoya-v-staczionare-sankt-peterburg-10.ru .
вызов нарколога на дом анонимно вызов нарколога на дом анонимно .
“вывод из запоя на халтурина – лечение алкоголизма, лечение наркомании “вывод из запоя на халтурина – лечение алкоголизма, лечение наркомании .
нарколог нижний новгород нарколог нижний новгород .
For those who appreciate clean design and premium materials, Common Projects remains one of the strongest names in minimalist luxury footwear.
Копицентр «Копирыч» https://kopirych.by профессиональный партнер для тех, кому нужна качественная печать фото в городе минск и по всей Беларуси. Мы предлагаем полный комплекс полиграфические услуги для частных клиентов и компаний: от срочной подготовки документов до изготовления рекламной продукции и персональных сувениров.
иду на неву документальный фильм progulka-po-neve.ru .
луна капсульные дома луна капсульные дома .
туры на теплоходе из спб туры на теплоходе из спб .
Качественные масла и смазки литиевые смазки краснодар подбор продукции для авто, спецтехники и промышленного оборудования. Обеспечьте надежную работу механизмов и защиту от износа при любых условиях эксплуатации.
Follower growth compounds when you combine strategies; buy instagram views and likes alongside follower boosts for comprehensive social proof.
Нужен грузовик? дилер коммерческих автомобилей компания «НЕО ТРАК» — это современный дилерский центр полного цикла, работающий на рынке коммерческого транспорта и спецтехники уже более 20 лет. Являясь официальным дилером ведущих производителей, таких как DONGFENG, JAC, FAW, DAEWOO TRUCKS, ISUZU, HYUNDAI и других, компания предлагает широкий выбор грузовых автомобилей различной тоннажности, спецтехники, от фургонов и бортовых платформ до эвакуаторов и крано-манипуляторных установок.
Лучшие профессии обучение дистанционно слесарь кип москва возможность получить практические знания и освоить востребованные специальности в короткие сроки. Обучение подходит для тех, кто хочет начать карьеру или сменить сферу деятельности. Все материалы доступны онлайн и сопровождаются поддержкой преподавателей.
капельница от запоя в стационаре капельница от запоя в стационаре .
нарколог на дом анонимно нарколог на дом анонимно .
Решил купить авто? машины из кореи подбор, проверка, доставка и оформление под ключ. Найдем надежный автомобиль по вашим параметрам и бюджету с гарантией прозрачности сделки.
Лучшие ограждения забор 3д панели практичное и долговечное решение. Усиленные ребра жесткости обеспечивают прочность, а современное покрытие защищает от ржавчины. Идеально для дома, дачи, предприятий и общественных территорий.
Капельница от похмелья нужна не только в случаях тяжёлой интоксикации, но и при более лёгких симптомах, когда пациент ощущает себя уставшим и измотанным, но не может справиться с проблемами самостоятельно. Некоторые из симптомов, при которых капельница может быть особенно полезна, включают:
Подробнее тут – капельница от похмелья анонимно екатеринбург
мелбет акции мелбет акции .
вывести из запоя на дому нижний новгород narkologicheskaya-pomoshh-nizhnij-novgorod-2.ru .
капельница от алкоголя стационар капельница от алкоголя стационар .
экскурсия по рекам и каналам экскурсия по рекам и каналам .
В Нижнем Новгороде услуга выезда нарколога чаще всего используется при состояниях, когда пациент физически не может посетить клинику или требуется срочное медицинское вмешательство. Врач приезжает с необходимыми препаратами и оборудованием, проводит осмотр и сразу приступает к лечению. Такой формат особенно важен при выраженной интоксикации и нестабильном состоянии.
Разобраться лучше – narkolog-na-dom-nizhnij-novgorod.ru/
Капельница от похмелья — это эффективный способ экстренной помощи, предназначенный для того, чтобы помочь организму быстро восстановиться после злоупотребления алкоголем. В наркологической клинике «Частный медик 24» в Самаре мы предоставляем услугу безопасной детоксикации и восстановления 24/7. Капельница помогает организму вывести токсины, восстановить водно-электролитный баланс и улучшить общее состояние пациента, не создавая дополнительных нагрузок на сердце, печень и почки.
Подробнее тут – капельница от похмелья вызов на дом в самаре
Капельница от похмелья в Екатеринбурге с выездом специалиста, подбором терапии и восстановлением состояния в наркологической клинике «Частный медик 24»
Подробнее – капельница от похмелья на дому
Hey I know this is off topic but I was wondering if you knew of any widgets I could add to my blog that automatically tweet my newest twitter updates.
I’ve been looking for a plug-in like this for quite some time and was
hoping maybe you would have some experience with something like
this. Please let me know if you run into anything.
I truly enjoy reading your blog and I look forward to your new updates.
вывод из запоя на дому вывод из запоя на дому .
Выезд нарколога начинается с осмотра пациента. Доктора измеряют давление, пульс, оценивают уровень сознания и выраженность симптомов. На основании этих данных формируется план лечения, который реализуется сразу на месте. Такой подход позволяет быстро перейти к стабилизации состояния без лишних этапов.
Детальнее – вывод из запоя на дому анонимно санкт-петербург
Существует ряд ситуаций, при которых вызов специалиста на дом является обоснованным решением:
Изучить вопрос глубже – нарколог на дом нижний новгород
При первой консультации нарколог осматривает пациента, чтобы оценить его состояние и подобрать оптимальную схему лечения. В зависимости от тяжести похмелья, врач может назначить инфузию с регидратационными растворами, витаминами группы B и другими препаратами, которые способствуют восстановлению. Важно, что капельница не только помогает снять симптомы, но и устраняет причины токсического воздействия алкоголя на организм, предотвращая развитие осложнений.
Разобраться лучше – капельница от похмелья вызов на дом
Вывод из запоя на дому в Санкт-Петербурге с выездом нарколога, детоксикацией и восстановлением состояния в наркологической клинике «Частный медик 24»
Выяснить больше – вывод из запоя на дому цена в санкт-петербурге
водоход спб водоход спб .
Обращение в наркологический стационар особенно важно в случае тяжелой зависимости, когда человек не способен контролировать свои действия, а угрозы для здоровья возрастают. В таких случаях важно не откладывать начало лечения, а обратиться за помощью сразу же, чтобы избежать серьезных последствий для организма. При выборе стационара следует обратить внимание на наличие лицензии, а также возможность получения психотерапии и других профессиональных услуг в области наркологии для комплексного лечения зависимости.
Углубиться в тему – частный наркологический стационар в санкт-петербурге
алкоголизм вызов на дом алкоголизм вызов на дом .
The comprehensive narrative available at https://npprteam.shop/en/articles/discord/the-story-of-discord-in-simple-terms-how-did-a-whole-world-of-communities-grow-out-of-a-chat-for-games/ illuminates how Discord’s founding principles and technical decisions transformed the platform from a niche gaming utility into a global infrastructure for community building across virtually every vertical and demographic. The story reveals critical inflection points where product features aligned with emerging community needs, enabling Discord to capture markets that traditional social media platforms overlooked or underserved. Understanding this progression equips aspiring community builders, entrepreneurs, and platform strategists with a case study in how solving a specific user pain point can unlock a massive addressable market. The article’s examination of Discord’s growth trajectory, monetization approach, and competitive advantages provides valuable lessons for anyone building community-driven products or managing large-scale member networks.
Процедура проводится опытными наркологами, которые подбирают необходимое лечение на основе индивидуальных особенностей пациента. В клинике «Частный медик 24» применяются только эффективные и безопасные препараты, которые помогают организму восстановиться и избавиться от токсинов. Важно помнить, что капельница от похмелья — это не просто временное облегчение, а важный шаг к долгосрочному восстановлению организма и профилактике алкоголизма.
Выяснить больше – капельница от похмелья анонимно екатеринбург
вытрезвитель нижний новгород narkologicheskaya-pomoshh-nizhnij-novgorod-2.ru .
контора мелбет контора мелбет .
покататься на кораблике в санкт петербурге покататься на кораблике в санкт петербурге .
Существует ряд ситуаций, при которых вызов специалиста на дом является обоснованным решением:
Подробнее – вызов нарколога на дом в нижнем новгороде
Вывод из запоя в стационаре — это формат медицинской помощи, при котором пациент находится под круглосуточным наблюдением и получает лечение в контролируемых условиях. Такой подход применяется в ситуациях, когда состояние нестабильно или есть риски осложнений. В наркологической клинике «Частный медик 24» в Нижнем Новгороде стационарная помощь выстраивается по принципу поэтапной стабилизации: от первичного осмотра и оценки рисков до достижения устойчивых показателей и перехода к восстановлению.
Подробнее тут – нарколог на дом вывод из запоя
В Самаре клиника «Частный медик 24» предоставляет круглосуточную помощь по выведению из запоя и снятию симптомов похмелья. Когда человек сталкивается с тяжёлым состоянием после длительного употребления алкоголя, важно вовремя оказать помощь. Врач приедет на дом и проведёт все необходимые процедуры, включая капельницу, которая поможет восстановить водно-электролитный баланс, нормализовать уровень сахара в крови и вывести токсины из организма.
Ознакомиться с деталями – капельница от похмелья цена
Вывод из запоя на дому в Санкт-Петербурге с подбором терапии, наблюдением врача и комфортным лечением в наркологической клинике «Частный медик 24»
Получить дополнительную информацию – анонимный вывод из запоя на дому санкт-петербург
Лечение в наркологическом стационаре в Санкт-Петербурге включает в себя комплекс мероприятий, направленных на восстановление физического и психического состояния пациента. Важно понимать, что лечение зависимости — это многогранный процесс, включающий не только медицинские процедуры, но и длительную реабилитацию, которая помогает человеку вернуться к нормальной жизни. В стационаре пациенты получают круглосуточное наблюдение, что значительно увеличивает шансы на успешное лечение и предотвращение рецидивов.
Подробнее тут – http://narkologicheskij-staczionar-sankt-peterburg-1.ru/
В Санкт-Петербурге вывод из запоя на дому используется в ситуациях, когда состояние пациента требует медицинской помощи, но позволяет обойтись без лечения в стационаре. Врач проводит консультацию, оценивает длительность запоя, выраженность симптомов и общее состояние, анализируя данные пациента, после чего принимает решение о тактике лечения при алкоголизме. При необходимости можно оформить вызов специалиста или заказать услугу заранее.
Исследовать вопрос подробнее – анонимный вывод из запоя на дому в санкт-петербурге
выведение из запоя в наркологическом стационаре выведение из запоя в наркологическом стационаре .
К стационарному формату чаще всего прибегают в следующих случаях:
Подробнее можно узнать тут – вывод из запоя на дому цена
Нарколог на дом в Воронеже с быстрым выездом, индивидуальным подбором терапии и наблюдением в наркологической клинике «Частный медик 24»
Подробнее – врач нарколог на дом
Капельница, как правило, включает в себя не только детоксикацию, но и дополнительные компоненты, такие как витамины, антидепрессанты или препараты для стабилизации сердечного ритма, что делает лечение более комплексным и эффективным.
Углубиться в тему – капельницы от запоя вызов город
Такие состояния позволяют проводить лечение на дому с контролем динамики. При выявлении рисков врач может изменить тактику и рекомендовать стационар или другие методы лечения зависимости.
Подробнее тут – https://vyvod-iz-zapoya-na-domu-sankt-peterburg-8.ru
В Санкт-Петербурге услуга вывода из запоя на дому применяется в ситуациях, когда требуется медицинская помощь, но нет показаний к стационарному лечению. Врач проводит консультацию, оценивает состояние пациента, длительность употребления и выраженность симптомов, после чего принимает решение о тактике лечения при алкоголизме. Важно, что терапия начинается сразу после осмотра, а при необходимости можно заранее заказать выезд специалистов.
Подробнее можно узнать тут – нарколог на дом вывод из запоя
Чаще всего домашний формат применяется при следующих состояниях:
Подробнее – вывод из запоя на дому
Наши врачи приезжают в удобное для пациента время и проводят полный осмотр. В зависимости от состояния пациента, они подбирают необходимое лечение: капельницы для снятия токсинов, медикаментозные препараты для стабилизации состояния, а также дают рекомендации по дальнейшему восстановлению. Важно, что лечение на дому позволяет избежать медицинской огласки и лишнего стресса, а также гарантирует полную конфиденциальность.
Выяснить больше – вызвать нарколога на дом самара
Капельница помогает организму быстрее справиться с этими симптомами и восстановить нормальное функционирование, а также значительно снижает время, необходимое для полного выздоровления. Даже при значительном похмелье, как показывает практика, пациент уже через несколько часов чувствует значительное улучшение. Важно учитывать противопоказания к проведению процедуры, однако все услуги могут быть предоставлены анонимно. При необходимости подключается психиатр для более комплексной оценки состояния пациента.
Разобраться лучше – капельница от похмелья на дом
Капельница от похмелья в Самаре: быстрое восстановление, снятие интоксикации и улучшение самочувствия под контролем специалистов в наркологической клинике «Похмельная служба»
Ознакомиться с деталями – капельница от похмелья цена
Игнорирование выраженных симптомов может привести к развитию таких опасных состояний, как алкогольный делирий, острые психозы, инфаркт или инсульт. Вызов нарколога на дом круглосуточно позволяет оперативно стабилизировать состояние пациента в привычной для него обстановке, минимизируя стресс и риски, связанные с транспортировкой в стационар. Анонимный формат обращения обеспечивает конфиденциальность и делает помощь доступной даже для тех, кто опасается огласки.
Подробнее тут – нарколог на дом вывод в самаре
Understanding TikTok Ads subscription funnel optimization for 2026 unlocks a proven framework for converting casual viewers into recurring revenue customers. Subscription businesses face unique challenges compared to one-time product sellers: they must attract users willing to commit long-term, establish trust quickly, and demonstrate ongoing value within seconds. This resource walks through the complete funnel architecture, from awareness creatives that address subscription hesitation to retention messaging that encourages upgrade tiers and longer commitments. The platform’s algorithm excels at identifying audiences predisposed to subscription models, particularly younger demographics already accustomed to recurring entertainment and software purchases. By mapping each funnel stage to specific creative types and bidding strategies, teams can reduce churn-driven acquisition costs and improve lifetime value metrics significantly.
Есть состояния, при которых откладывать обращение не стоит. Ниже перечислены признаки, при которых вызывать врача на дом разумно именно в ближайшее время, а не после очередной неудачной попытки «перележать» тяжёлый период самостоятельно.
Подробнее тут – http://www.domen.ru
нарколог запой нарколог запой .
Запой — это состояние, которое развивается на фоне длительного употребления алкоголя, сопровождающееся острыми симптомами интоксикации. Капельница от запоя может быть необходима, когда состояние пациента требует немедленного вмешательства. Важно своевременно заметить признаки, указывающие на необходимость медицинской помощи, таких как признаки алкоголизма, и в случае необходимости — кодирование или вывод из запоя для более комплексного лечения.
Получить дополнительную информацию – капельница от запоя цена в нижнем новгороде
Вывод из запоя в стационаре в Нижнем Новгороде с круглосуточным наблюдением и поэтапным восстановлением в наркологической клинике «Частный медик 24»
Получить дополнительные сведения – http://vyvod-iz-zapoya-v-staczionare-nizhnij-novgorod-1.ru/
Такие симптомы требуют медицинского вмешательства, поскольку могут усиливаться без лечения. Капельница позволяет стабилизировать состояние и ускорить восстановление. Услуги могут предоставляться анонимно, а при необходимости пациент направляется на лечение в стационаре.
Подробнее можно узнать тут – капельница от похмелья
Этот процесс не занимает много времени — обычно процедура длится от 30 до 60 минут. Важно, что врач контролирует все этапы, обеспечивая безопасность пациента и корректируя терапию по мере необходимости. Такой подход позволяет быстро и эффективно облегчить симптомы похмелья и вернуться к нормальной жизнедеятельности.
Выяснить больше – капельница от похмелья самара
Обращение в наркологический стационар особенно важно в случае тяжелой зависимости, когда человек не способен контролировать свои действия, а угрозы для здоровья возрастают. В таких случаях важно не откладывать начало лечения, а обратиться за помощью сразу же, чтобы избежать серьезных последствий для организма. При выборе стационара следует обратить внимание на наличие лицензии, а также возможность получения психотерапии и других профессиональных услуг в области наркологии для комплексного лечения зависимости.
Узнать больше – http://narkologicheskij-staczionar-sankt-peterburg-1.ru
· отопления: классического с радиаторами или теплого пола; · водоснабжения: горячего, холодного; · вентиляции, климатических систем; · мелиорации, полива, орошения в садоводстве, фермерском или сельском хозяйстве; · производственных, технологических линий на, химических, других предприятиях;
Трубы и фитинги PPR: преимущества https://deneb-spb.ru/contacts
Класс эксплуатации https://deneb-spb.ru/krany-latunnye-rezbovye
однослойными; трехслойными https://deneb-spb.ru/mufty-i-perekhodniki
Максимальное давление 16 кгс/см 2 или 1,6 МПа, температура до 60°C https://deneb-spb.ru/ankery
Применяются также для систем с холодной водой https://deneb-spb.ru/filtry-i-obratnye-klapany
Возможно использование в многоэтажных домах https://deneb-spb.ru/ugolniki
– низкая шероховатость (0,006 мм) препятствует образованию отложений;
мелбет букмекерская контора официальный сайт мелбет букмекерская контора официальный сайт .
Капельница от похмелья — это внутривенное введение специально подобранных растворов, которые помогают ускорить выведение токсинов, восстановить водно-электролитный баланс и нормализовать обмен веществ. В состав капельницы могут входить различные компоненты, такие как солевые растворы, витамины, глюкоза и препараты для детоксикации. Она особенно эффективна при последствиях запоя и хронического алкоголизма.
Получить больше информации – http://kapelnicza-ot-pokhmelya-nizhnij-novgorod.ru
прогулка по неве в питере прогулка по неве в питере .
Анонимное лечение на дому ценно ещё и тем, что снижает внутреннее сопротивление самого пациента. Для многих людей первый контакт с врачом происходит именно дома, без дороги, без ожидания, без страха чужих взглядов. Такой формат помогает начать разговор не только о снятии острых симптомов, но и о более широких вопросах: что делать после выхода из запоя, когда требуется кодирование, в каких случаях нужна реабилитация, а когда первичная наркологическая помощь уже должна переходить в полноценный лечебный маршрут. Врач может помочь и в ситуациях, связанных не только с алкоголем, но и с наркомании, если семье нужно понять, что происходит с зависимым человеком и какой следующий шаг будет для него безопасным.
Разобраться лучше – narkolog-na-dom-voronezh-1.ru/
Процесс капельницы включает внутривенное введение различных растворов, которые помогают нейтрализовать эффекты алкогольной интоксикации, включая последствия запоя и алкоголизма. Наиболее часто в составе капельницы используются солевые и глюкозные растворы, витамины группы B, а также препараты для детоксикации организма. Эти компоненты помогают быстро восстановить водно-электролитный баланс, улучшить обмен веществ и ускорить выведение продуктов распада алкоголя.
Подробнее – капельница от похмелья анонимно в самаре
На первом этапе специалист проводит визуальный осмотр пациента, измеряет артериальное давление, пульс, уровень кислорода в крови и оценивает общее психоэмоциональное состояние. Важно выявить степень интоксикации, наличие осложнений и противопоказаний к проведению терапии на дому. В случае наркомании и длительного употребления наркотиков, пациенту может быть предложена консультация и лечение, включая реабилитацию на летний период, если состояние требует интенсивного контроля.
Ознакомиться с деталями – нарколог на дом
Наркологический стационар с комфортными условиями в Санкт-Петербурге — это специализированное учреждение, которое не только помогает пациентам избавиться от зависимости, но и создает благоприятные условия для выздоровления. В таких стационарах важны не только высококачественные медицинские услуги, но и уютная атмосфера, которая способствует восстановлению физического и психоэмоционального состояния пациента.
Углубиться в тему – http://narkologicheskij-staczionar-sankt-peterburg-4.ru
лечение от запоя в стационаре лечение от запоя в стационаре .
Вывод из запоя на дому в Санкт-Петербурге с подбором терапии, наблюдением врача и комфортным лечением в наркологической клинике «Частный медик 24»
Получить дополнительные сведения – вывод из запоя на дому круглосуточно санкт-петербург
мел бет мел бет .
Капельница от похмелья — это медицинская процедура, направленная на устранение последствий алкогольной интоксикации и восстановление работы организма. В отличие от домашних методов, инфузионная терапия позволяет воздействовать на причину состояния, а не только на его проявления. В наркологической клинике «Похмельная служба» капельная терапия проводится с выездом специалиста на дом, что позволяет начать лечение без задержек и в комфортных условиях.
Исследовать вопрос подробнее – kapelnicza-ot-pokhmelya-voronezh-5.ru/
В Санкт-Петербурге вывод из запоя на дому используется в ситуациях, когда состояние пациента требует медицинской помощи, но позволяет обойтись без лечения в стационаре. Врач проводит консультацию, оценивает длительность запоя, выраженность симптомов и общее состояние, анализируя данные пациента, после чего принимает решение о тактике лечения при алкоголизме. При необходимости можно оформить вызов специалиста или заказать услугу заранее.
Детальнее – нарколог на дом вывод из запоя санкт-петербург
Когда симптомы становятся настолько выраженными, что они мешают нормальному функционированию, капельница становится необходимостью. Она помогает избавиться от дискомфорта и значительно ускоряет процесс восстановления, давая организму все необходимые вещества для нормализации его работы, при этом может проводиться наркологическая детоксикация. Контроль врача на протяжении всей процедуры гарантирует, что капельница будет введена правильно и безопасно, с учетом всех показателей пациента, а при необходимости можно заказать дальнейшую реабилитацию и кодирование.
Изучить вопрос глубже – kapelnicza-ot-pokhmelya-samara-13.ru/
мел бет букмекерская мел бет букмекерская .
melbet app download iphone gbufavorit.ru .
бк мелбет официальный сайт бк мелбет официальный сайт .
vavada казино онлайн казахстан вход vavada казино онлайн казахстан вход .
мелбет казино вход мелбет казино вход .
Стоимость капельницы от похмелья в Самаре зависит не только от прайса клиники, но и от состава инфузионной терапии, срочности выезда, времени суток и общего состояния пациента, включая возможные последствия алкоголизма. Базовые программы обычно включают осмотр специалиста, постановку капельницы и стандартный набор растворов для снятия интоксикации. Если состояние тяжелее, может потребоваться кодирование или лечение в стационаре, что увеличивает цену из-за расширенного состава препаратов и более длительного наблюдения.
Углубиться в тему – капельница от похмелья анонимно в самаре
Капельница от запоя в Нижнем Новгороде: снятие интоксикации, восстановление организма и помощь при запое под контролем специалистов в наркологической клинике «Похмельная служба»
Подробнее тут – http://kapelnica-ot-zapoya-nizhnij-novgorod-4.ru/
Нужна градирня? https://gradirni.mystrikingly.com ключевой элемент системы охлаждения, позволяющий эффективно снижать температуру воды за счет теплообмена с воздухом. Применяется в промышленности, энергетике и на предприятиях. Обеспечивает стабильную и экономичную работу оборудования.
Нужна септик или погреб? https://septikidlyadoma.mystrikingly.com эффективное решение для автономной канализации. Системы обеспечивают качественную очистку сточных вод, устраняют запахи и безопасны для окружающей среды. Подходят для частных домов, коттеджей и загородных участков.
При выезде нарколога на дом в Самаре мы проводим диагностику состояния пациента, чтобы понять, какие препараты и процедуры необходимы для стабилизации. Это может включать регидратацию, витамины группы B, антиеметики и другие препараты для снятия симптомов похмелья. Все препараты подбираются индивидуально в зависимости от состояния пациента и его нужд. Это позволяет значительно сократить время на восстановление и быстро вернуться к нормальному состоянию.
Изучить вопрос глубже – капельница от похмелья на дому в самаре
Детоксикация на дому начинается с осмотра пациента. Доктора оценивают витальные показатели, уровень сознания и выраженность симптомов, анализируя текущие данные. После этого формируется план лечения, который реализуется сразу. Такой подход позволяет сократить время до начала терапии и повысить её эффективность.
Узнать больше – анонимный вывод из запоя на дому
вывод из запоя в стационаре вывод из запоя в стационаре .
Капельница от похмелья в Самаре с выездом на дом, восстановлением водного баланса и медицинской помощью в наркологической клинике «Частный медик 24»
Получить дополнительные сведения – капельница от похмелья на дому
Капельница от похмелья — это эффективное средство для быстрого снятия симптомов алкогольной интоксикации и восстановления организма после злоупотребления алкоголем. В наркологической клинике «Частный медик 24» в Екатеринбурге мы предоставляем услуги по экстренной помощи и детоксикации на дому, включая установку капельниц, которые позволяют улучшить состояние пациента за короткое время. Процедура включает в себя введение специальных растворов, которые восстанавливают водно-электролитный баланс, выводят токсины и устраняют основные симптомы похмелья, такие как головная боль, слабость, тошнота и головокружение.
Подробнее можно узнать тут – капельница от похмелья анонимно в екатеринбурге
официальный сайт мелбет официальный сайт мелбет .
Капельница от похмелья в Самаре: быстрое восстановление, снятие интоксикации и улучшение самочувствия под контролем специалистов в наркологической клинике «Похмельная служба»
Ознакомиться с деталями – http://kapelnicza-ot-pokhmelya-samara-6.ru
выведение из запоя в стационаре спб выведение из запоя в стационаре спб .
Процесс лечения начинается с консультации врача, который оценивает состояние пациента, его анамнез и определяет, какие процедуры и препараты нужно использовать. В большинстве случаев капельница включает в себя регидратацию, витамины группы B, антиеметики, препараты для улучшения работы печени и почек. Важно, что капельница не только помогает организму вывести токсины, но и восстанавливает нормальную работу всех систем организма, обеспечивая быстрое улучшение самочувствия.
Выяснить больше – http://kapelnicza-ot-pokhmelya-samara.ru/
Капельница от похмелья — это внутривенное введение специально подобранных растворов, которые помогают ускорить выведение токсинов, восстановить водно-электролитный баланс и нормализовать обмен веществ. В состав капельницы могут входить различные компоненты, такие как солевые растворы, витамины, глюкоза и препараты для детоксикации. Она особенно эффективна при последствиях запоя и хронического алкоголизма.
Разобраться лучше – kapelnicza-ot-pokhmelya-nizhnij-novgorod.ru/
Игнорирование выраженных симптомов может привести к развитию таких опасных состояний, как алкогольный делирий, острые психозы, инфаркт или инсульт. Вызов нарколога на дом круглосуточно позволяет оперативно стабилизировать состояние пациента в привычной для него обстановке, минимизируя стресс и риски, связанные с транспортировкой в стационар. Анонимный формат обращения обеспечивает конфиденциальность и делает помощь доступной даже для тех, кто опасается огласки.
Получить дополнительную информацию – нарколог на дом анонимно
Для жителей Екатеринбурга наркологическая клиника «Частный медик 24» предлагает платную услугу выезда врача на дом для проведения капельницы от похмелья. Когда человек переживает сильные симптомы похмелья, такие как головная боль, тошнота, слабость, важно не тянуть с лечением и начать восстановление как можно скорее. Капельница от похмелья помогает хорошо облегчить самочувствие пациента, снять головную боль и улучшить общее состояние, восстановив водно-электролитный баланс в организме.
Узнать больше – капельница от похмелья в екатеринбурге
Выезд специалиста начинается с оценки состояния пациента. Врач измеряет давление, пульс, оценивает общее самочувствие и выраженность симптомов. На основании этих данных формируется план лечения и подбирается состав капельницы. Такой подход позволяет учитывать индивидуальные особенности пациента и эффективно провести вывод из запоя.
Углубиться в тему – капельница от похмелья на дому
Капельница от похмелья в Воронеже с индивидуальной инфузионной терапией и врачебным контролем в наркологической клинике «Похмельная служба»
Получить дополнительные сведения – капельница от похмелья
букмекерская компания мелбет букмекерская компания мелбет .
Показания к проведению инфузионной терапии включают:
Узнать больше – капельница от похмелья на дом
мелбет регистрация официальный сайт мелбет регистрация официальный сайт .
Этот процесс не занимает много времени — обычно процедура длится от 30 до 60 минут. Важно, что врач контролирует все этапы, обеспечивая безопасность пациента и корректируя терапию по мере необходимости. Такой подход позволяет быстро и эффективно облегчить симптомы похмелья и вернуться к нормальной жизнедеятельности.
Подробнее – http://kapelnicza-ot-pokhmelya-samara-13.ru/
melbet apk iphone melbet apk iphone .
мелбет онлайн мелбет онлайн .
Суть капельницы заключается в том, чтобы быстро ввести в организм необходимые растворы, которые помогают восстановить водно-солевой баланс, очищают организм от токсинов, ускоряют обмен веществ и снижают нагрузку на внутренние органы. Врачи-наркологи используют специальные составы, которые включают в себя жидкости, электролиты, витамины и лекарственные средства для снятия симптомов похмелья.
Ознакомиться с деталями – капельница от похмелья цена нижний новгород
скачат мелбет скачат мелбет .
вавада казино вавада казино .
Нужен был телефон срочно, и этот магазин действительно выручил. Заказ обработали оперативно, быстро отправили и держали в курсе по статусу. Смартфон пришёл в идеальном состоянии, без каких либо вопросов. Отличная скорость и нормальный сервис, заказать телефон с доставкой
Капельница действует быстро благодаря тому, что активные вещества вводятся непосредственно в кровь, минуя желудочно-кишечный тракт. Это позволяет быстро уменьшить симптомы, такие как головная боль, тошнота, слабость, а также нормализовать работу печени и почек, которые страдают от длительного употребления алкоголя. В некоторых случаях, если требуется длительное наблюдение, пациент может быть направлен в стационар, и лечение может продолжаться на летний период с более тщательным контролем состояния.
Получить больше информации – капельница от запоя на дому нижний новгород
Наркологический стационар — это специализированное медицинское учреждение, предназначенное для лечения и реабилитации пациентов с зависимостью от алкоголя, наркотиков и других психоактивных веществ. В Санкт-Петербурге существует множество таких учреждений, которые предоставляют комплексную помощь людям, страдающим от зависимости. Лечение в стационаре часто является первым шагом на пути к выздоровлению, особенно в случаях тяжелых зависимостей, когда амбулаторное лечение может не дать должного эффекта. В случае запоя или хронического алкоголизма стационарное лечение может стать необходимым, особенно если выезд на дом не позволяет должным образом контролировать процесс восстановления.
Узнать больше – наркологическая клиника стационар в санкт-петербурге
https://starcasino-au.com/
geo оптимизация сайта https://geo-optimizaciya-sajta.ru .
мелбет официальный сайт мелбет официальный сайт .
https://starcasino-au.com/
https://melbetslot.ru https://melbetslot.ru .
услуги нарколога на дом услуги нарколога на дом .
кодировка от алкоголя в нижнем новгороде кодировка от алкоголя в нижнем новгороде .
melbet apps download melbet apps download .
мелбет онлайн мелбет онлайн .
вавада казино онлайн рабочее зеркало вавада казино онлайн рабочее зеркало .
Основные показания для проведения процедуры:
Детальнее – http://kapelnicza-ot-pokhmelya-voronezh-4.ru/
В некоторых случаях капельница может быть использована не только для снятия симптомов похмелья, но и для восстановления организма после длительного запоя или при хроническом алкоголизме, когда организм особенно ослаблен. В таких случаях лечение должно проводиться под контролем квалифицированных специалистов, чтобы избежать осложнений и ускорить восстановление.
Получить дополнительную информацию – капельница от похмелья цена в самаре
Остались только положительные впечатления от покупки. Магазин быстро обработал заказ, а менеджер вежливо ответил на все вопросы. Телефон пришёл в отличном состоянии, без задержек и сюрпризов. Хороший сервис, к которому хочется вернуться: arzon telefon
https://mhp.ooo/products/oxpla-100mg
vavada казино сайт vavada казино сайт .
melbet russia melbet russia .
melbet ru официальный сайт melbet ru официальный сайт .
Китайским археологам удалось обнаружить крупнейший рудник по добыче бирюзы на территории Синьцзян-Уйгурского автономного района, что на северо-западе Китая https://www.legnostyle.ru/catalog/lestnici/lestnica-l1-24.html
Ознакомьтесь с каталогом элитных кухонь, фото которых соответствуют реальности https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/vhodnie-dveri/vhodnaya-dver-e2.html
Если у Вас есть вопросы, свяжитесь с нами по телефонам, указанным на сайте, или напишите на электронную почту https://www.legnostyle.ru/mebel-barokko.html
Наши специалисты рады помочь Вам с покупкой элитных кухонь https://www.legnostyle.ru/derevyannye-stupeni-dlya-lestnic.html
Некоторые из популярных моделей имеются в выставочном зале мебельного салона в Москве, что позволит приобрести необходимые элементы интерьера в кратчайшие сроки – всего за 1-2 дня https://www.legnostyle.ru/catalog/kuhni/kuhna-15.html
Итальянская мебель под заказ поставляется в срок от 1 месяца https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/vhodnie-dveri/vhodnaa-dver-e1.html
При изготовлении мебели мы используем только качественные и натуральные материалы, такие как: ценные породы древесины, искусственный и натуральный камень, сертифицированные ДСП и МДФ https://www.legnostyle.ru/catalog/lestnici/na-vtoroy-etazh/lestnica-l4-5.html
Необычность и узнаваемость стиля достигается за счет уникального соединения гибкости и особенного принципа работы с новыми материалами и ценными породами дерева https://www.legnostyle.ru/otzyvy/
Подход к дизайну строится на объединении мастерства, стиля, постоянных исследований и креативности https://www.legnostyle.ru/catalog/inter-eri/stenovie-paneli/stenovie-paneli-model-s7.html
Такой вид отделки мебели существует очень давно, наши предки использовали кожу в разных целях и для оббивки мебели тоже https://www.legnostyle.ru/catalog/mebel/derevyannye-stoly/stol-model-s-12.html
На сегодняшний день это больше чем просто элемент декора https://www.legnostyle.ru/catalog/inter-eri/a-1.html
Это, в каком-то роде, особая философия, способная даже перерасти в будущем в отдельное стилевое решение https://www.legnostyle.ru/catalog/mejkomnatnie-dveri/nestandarnye/model-i14.html
капельница на дому анонимно капельница на дому анонимно .
? Колпачный пер., д https://maze.tattoo/catalog/b/beskonechnii-uzel/
6, стр https://maze.tattoo/catalog/r/rok-muzyka/
4 https://maze.tattoo/catalog/p/pechat-velesa/
Реклама на сайте Контакты Мобильная версия Пользовательское соглашение API Email редакции Отзывы и предложения https://maze.tattoo/catalog/p/pero/
? ул https://maze.tattoo/catalog/ya/yakor/
Сущёвская, д https://maze.tattoo/catalog/t/
25, стр https://maze.tattoo/catalog/t/tradik/
1 https://maze.tattoo/catalog/sha/schuka/
Интересные события в городе https://maze.tattoo/catalog/o/
Tattoo Times 18+
Фильм, фильм, фильм: рецензия на сериал «Киностудия»
https://mhp.ooo/catalog/lenvatinib
1xbet yeni giri? adresi hhnbigger.com .
скачать мелбет слоты melbetslot.ru .
психиатр нарколог нижний новгород психиатр нарколог нижний новгород .
Вывод из запоя в стационаре в Нижнем Новгороде с детоксикацией, мониторингом состояния и медицинской помощью в наркологической клинике «Частный медик 24»
Узнать больше – вывод из запоя капельница на дому
К стационарному формату чаще всего прибегают в следующих случаях:
Подробнее – срочный вывод из запоя
Заказал смартфон через сайт и весь процесс оказался очень удобным. Никакой путаницы, всё прозрачно и понятно. Менеджер проконсультировал по характеристикам и помог с выбором. Доставка пришла вовремя, покупкой остался доволен: телефоны на
Капельница от похмелья в Екатеринбурге с медицинским контролем и поддержкой организма в наркологической клинике «Частный медик 24»
Получить дополнительные сведения – капельница от похмелья вызов на дом
вавада казино войти вавада казино войти .
мелбет казино скачать на айфон мелбет казино скачать на айфон .
казино онлайн вавада играть онлайн регистрация казино онлайн вавада играть онлайн регистрация .
Выезд нарколога на дом в Самаре организован так, чтобы пациент получил помощь без ожидания и без лишней нагрузки на организм. После обращения специалист приезжает по указанному адресу, проводит первичный осмотр, оценивает общее состояние, уровень интоксикации, показатели давления, пульса, дыхания и собирает краткий анамнез. На основании этой оценки врач определяет, можно ли безопасно оказывать помощь на дому, и подбирает подходящую схему лечения, включая возможное кодирование или вывод из алкоголизма. Такой формат позволяет начать медицинские мероприятия сразу после осмотра и быстро перейти к стабилизации состояния.
Углубиться в тему – вызов нарколога на дом самара
https://mhp.ooo/catalog/erlotinib
услуги врача нарколога на дому услуги врача нарколога на дому .
melbet russia melbet russia .
мэлбэт мэлбэт .
клиника лечения зависимостей клиника лечения зависимостей .
https://starcasino-au.com/
1xbet g?ncel giri? 1xbet g?ncel giri? .
1xbet t?rkiye 1xbet t?rkiye .
1xbet yeni giri? adresi 1xbet yeni giri? adresi .
1xbet 1xbet .
1xbet 1xbet .
vavada казино официальный сайт вход vavada казино официальный сайт вход .
вывод из запоя доктор на дом вывод из запоя доктор на дом .
фриспины идеальны для высоких коэффициентов для новичков и опытных игроков, play fortuna сайт официальный
darknet market list https://darknetmarketstore.com/
кадирование кадирование .
1xbet 1xbet .
Играй и наслаждайся процессом: плей фортуна рабочее зеркало
1xbet giri? linki 1xbet giri? linki .
vavada com онлайн казино vavada com онлайн казино .
1xbet t?rkiye 1xbet t?rkiye .
1xbet 1xbet .
1xbet giri? yapam?yorum hhnbigger.com .
xbet giri?i xbet giri?i .
torzon market darknet https://darknetmarketstore.com/
Laravel обеспечивает быструю и безопасную разработку благодаря модульной архитектуре, защите от уязвимостей и удобному ORM. Фреймворк легко масштабируется, поддерживает очереди, кеширование и REST API. В связке с React создаёт современные SPA. Чистый код и экосистема ускоряют релиз и упрощают поддержку: https://domenanet.xyz/
xbet xbet .
Laravel обеспечивает быструю и безопасную разработку благодаря модульной архитектуре, защите от уязвимостей и удобному ORM. Фреймворк легко масштабируется, поддерживает очереди, кеширование и REST API. В связке с React создаёт современные SPA. Чистый код и экосистема ускоряют релиз и упрощают поддержку – https://domenanet.xyz/
1xbet giri? yapam?yorum 1xbet giri? yapam?yorum .
xbet giri?i xbet giri?i .
xbet giri? xbet giri? .
1xbet spor bahislerinin adresi 1xbet spor bahislerinin adresi .
xbet xbet .
1xbet t?rkiye giri? hhnbigger.com .
1xbet g?ncel giri? 1xbet g?ncel giri? .
В Воронеже услуга «нарколог на дом» востребована прежде всего тогда, когда состояние развивается быстро, а запас сил у пациента почти исчерпан. После нескольких дней употребления человеку бывает трудно даже выйти из квартиры: сохраняются слабость, дрожь, бессонница, тошнота, скачки давления, потливость, раздражительность и ощущение, что без новой дозы алкоголя легче уже не станет. Именно в этот момент домашний выезд специалиста помогает разорвать опасный цикл. Наркологическая помощь начинается там, где человек находится, а не там, куда он в идеале должен был бы доехать.
Получить дополнительную информацию – http://narkolog-na-dom-voronezh-1.ru
Нарколог на дом в Самаре — помощь при запое и интоксикации в наркологической клинике «Частный медик 24»
Выяснить больше – https://narkolog-na-dom-samara-2.ru/
Для семьи это тоже имеет большое значение. Пока врач в пути, родственники часто совершают одни и те же ошибки: пытаются «отпаивать» человека через силу, смешивают несовместимые медикаменты, дают советы, которые только повышают тревогу, спорят или требуют немедленно взять себя в руки. Профессиональный выезд снимает эту хаотичность. После осмотра врач объясняет, какие симптомы связаны с алкогольной интоксикацией, какие могут указывать на осложнения, что допустимо дома, а что требует перевода в стационар. В этом и состоит ценность выезда: он возвращает контроль над ситуацией и позволяет начать лечение без лишних задержек.
Углубиться в тему – нарколог на дом воронеж
Laravel обеспечивает быструю и безопасную разработку благодаря модульной архитектуре, защите от уязвимостей и удобному ORM. Фреймворк легко масштабируется, поддерживает очереди, кеширование и REST API. В связке с React создаёт современные SPA. Чистый код и экосистема ускоряют релиз и упрощают поддержку, https://domenanet.xyz/
1xbet tr 1xbet tr .
Есть состояния, при которых откладывать обращение не стоит. Ниже перечислены признаки, при которых вызывать врача на дом разумно именно в ближайшее время, а не после очередной неудачной попытки «перележать» тяжёлый период самостоятельно.
Узнать больше – запой нарколог на дом воронеж
1xbet turkiye 1xbet turkiye .
1xbet giri? adresi 1xbet giri? adresi .
xbet xbet .
После того как пациент вызвал нарколога на дом, врач прибывает на место и начинает с осмотра. Он оценивает общее состояние пациента, измеряет его пульс, давление, температуру, частоту дыхания и проверяет уровень сознания. Это необходимо для точной диагностики состояния и выбора наиболее эффективного метода лечения. Врач также уточняет анамнез, выясняет длительность употребления алкоголя или наркотиков, а также обращает внимание на наличие хронических заболеваний или других сопутствующих факторов, которые могут повлиять на лечение.
Получить дополнительную информацию – нарколог на дом вывод в самаре
В Воронеже услуга «нарколог на дом» востребована прежде всего тогда, когда состояние развивается быстро, а запас сил у пациента почти исчерпан. После нескольких дней употребления человеку бывает трудно даже выйти из квартиры: сохраняются слабость, дрожь, бессонница, тошнота, скачки давления, потливость, раздражительность и ощущение, что без новой дозы алкоголя легче уже не станет. Именно в этот момент домашний выезд специалиста помогает разорвать опасный цикл. Наркологическая помощь начинается там, где человек находится, а не там, куда он в идеале должен был бы доехать.
Исследовать вопрос подробнее – врач нарколог на дом воронеж
быстрые выплаты открывают доступ к удобной игры с телефона с поддержкой криптовалют: playfortuna-casino
1xbet giri? linki 1xbet giri? linki .
1xbet giri? linki kentseldonusumelkitabi.com .
1xbet t?rkiye giri? 1xbet t?rkiye giri? .
1xbet turkiye izmireniyipsikolog.com .
While conducting research on various vendor systems for comparison, I came across supplier dashboard entry and spent some time evaluating its structure in relation to similar platforms – Overall, the experience felt satisfactory and provided adequate functionality for basic browsing needs.
Нарколог на дом в Самаре востребован в самых различных ситуациях. Иногда пациент не в состоянии самостоятельно добраться до клиники из-за сильного состояния похмелья или ломки. В таких случаях выезд нарколога становится наиболее оптимальным решением. Наши специалисты оказывают помощь при следующих состояниях:
Узнать больше – вызвать нарколога на дом самара
В Екатеринбурге наркологическая клиника «Частный медик 24» предоставляет анонимную помощь при похмелье и алкогольной интоксикации. Услуга выезда нарколога на дом позволяет пациенту получить лечение в безопасной обстановке, не выходя из дома. Это идеальное решение для тех, кто не хочет, чтобы их зависимость была раскрыта, или кто по каким-либо причинам не может или не хочет посещать клинику.
Подробнее – капельница от похмелья анонимно в екатеринбурге
Вывод из запоя в стационаре — это медицинская помощь, при которой лечение проводится в условиях круглосуточного наблюдения и контролируемой среды. Такой формат применяется, когда состояние пациента требует постоянного мониторинга и поэтапной коррекции терапии. В наркологической клинике «Частный медик 24» в Нижнем Новгороде стационарное лечение выстраивается с учётом текущего состояния пациента, без перегрузки медикаментами и с регулярной оценкой результата на каждом этапе.
Получить дополнительную информацию – нарколог вывод из запоя нижний новгород
При таких условиях стационар позволяет контролировать состояние в режиме 24/7 и при необходимости быстро корректировать лечение. Это снижает риски и делает процесс более предсказуемым. При этом услуга может предоставляться анонимно, а цену лечения можно уточнить по телефону или при обращении в центр лечения алкоголизма и наркомании.
Подробнее тут – вывод из запоя
Доставка свежих цветов в день заказа. Флористы собирают букеты из проверенных поставок, бережно упаковывают и передают курьеру. Работаем ежедневно, гарантируем сохранность и точное время вручения. Анонимная отправка и фотоотчёт включены https://buketico.ru/
Капельница от похмелья — это не просто средство для снятия симптомов, но и эффективный способ быстрого восстановления организма после алкогольной интоксикации. В наркологической клинике «Частный медик 24» в Екатеринбурге мы предоставляем услугу выезда нарколога на дом, что позволяет пациентам получить необходимую медицинскую помощь, не покидая комфорт своей обстановки. Это особенно важно в случае, если состояние пациента серьёзно ухудшилось, и он не может поехать в клинику самостоятельно.
Подробнее – http://kapelnicza-ot-pokhmelya-ekaterinburg-7.ru/
Нарколог на дом — это удобное и эффективное решение для тех, кто сталкивается с тяжелыми последствиями запоя или алкогольной интоксикации. В наркологической клинике «Частный медик 24» в Самаре мы предоставляем круглосуточную помощь, выезд нарколога и лечение на дому. Это позволяет пациентам получить профессиональную медицинскую помощь в удобной и знакомой обстановке, что особенно важно, когда состояние человека ухудшается после длительного употребления алкоголя или наркотиков.
Получить дополнительные сведения – вызов нарколога на дом в самаре
1xbet giri? linki parkvebahceler.com .
Есть состояния, при которых откладывать обращение не стоит. Ниже перечислены признаки, при которых вызывать врача на дом разумно именно в ближайшее время, а не после очередной неудачной попытки «перележать» тяжёлый период самостоятельно.
Узнать больше – https://narkolog-na-dom-voronezh-1.ru
Главное преимущество такого выезда в том, что лечение начинается сразу. Не нужно ждать утра, искать транспорт, уговаривать человека ехать в тяжёлом состоянии или рисковать, пока он снова тянется к алкоголю, чтобы временно заглушить симптомы. Домашний визит даёт возможность быстро стабилизировать ситуацию и убрать хаотичность, которая часто возникает в семье в острый момент.
Получить дополнительную информацию – врач нарколог на дом в воронеже
круглосуточный стационар вывод из запоя vyvod-iz-zapoya-v-staczionare-sankt-peterburg-8.ru .
К стационарному формату чаще всего прибегают в следующих случаях:
Разобраться лучше – вывод из запоя на дому недорого в нижнем новгороде
Мощность двигателя https://rentbusspb.ru/arenda-avtobusa-king-long-2019-s-voditelem/
Аренда, прокат, заказ всех лимузинов города Иркутска https://rentbusspb.ru/mercedes-benz-e-213-2020-г/
Аренда автомобилей https://rentbusspb.ru/минивэн-toyota-alphard/
Профессиональный трансфер в аэропорт или на вокзал https://rentbusspb.ru/mercedes-benz-e-213-кортеж/
Обслуживание мероприятий https://rentbusspb.ru/arenda-avtobusa-fox-bus/
Аренда транспорта с водителем https://rentbusspb.ru/микроавтобус-mercedes-sprinter-vip/
Год выпуска:
экскурсионные туры; трансфер до аэропорта или железнодорожного вокзала и обратно; регулярная доставка сотрудников к месту работы; бизнес-поездки; групповые и индивидуальные перевозки детей; обслуживание свадеб, юбилеев, новогодних вечеринок и прочих торжеств https://rentbusspb.ru/mercedes-benz-e-213-2020-г/
г https://rentbusspb.ru/microavtobus-volkswagen-crafter-s-voditelem/
Иркутск https://rentbusspb.ru/mercedes-benz-c-класс-w205-рестайлинг/
1xbet t?rkiye 1xbet t?rkiye .
1xbet spor bahislerinin adresi 1xbet spor bahislerinin adresi .
седан передний автомат 121 л https://rentbusspb.ru/arenda-minivena-mercedes-vito-new-2016/
с https://rentbusspb.ru/microavtobus-volkswagen-crafter-s-voditelem/
1 https://rentbusspb.ru/arenda-range-rover-s-voditelem/
5 л https://rentbusspb.ru/arenda-ford-mustang-1969-s-voditelem/
2021 https://rentbusspb.ru/prokat-bmv-7/
климат-контроль https://rentbusspb.ru/arenda-avtobusa-tur-klassa-s-voditelem/
седан передний автомат 181 л https://rentbusspb.ru/avtopark-transporta-dlya-arendi/
с https://rentbusspb.ru/arenda-s233/
1,5 л 2023 https://rentbusspb.ru/arenda-mercedes-benz-gl-s-voditelem/
Машин в автопарке:
Существует ли возможность аренды автомобиля с водителем для поездок за пределы города?
Для удовлетворения потребностей клиента, у нас есть возможность подобрать конкретного водителя в соответствии с его пожеланиями и требованиями https://rentbusspb.ru/category/arenda-avtomobilei/
xbet xbet .
1xbet turkiye kentseldonusumelkitabi.com .
Доставка свежих цветов в день заказа. Флористы собирают букеты из проверенных поставок, бережно упаковывают и передают курьеру. Работаем ежедневно, гарантируем сохранность и точное время вручения. Анонимная отправка и фотоотчёт включены https://buketico.ru/
Нарколог на дом в Самаре востребован в самых различных ситуациях. Иногда пациент не в состоянии самостоятельно добраться до клиники из-за сильного состояния похмелья или ломки. В таких случаях выезд нарколога становится наиболее оптимальным решением. Наши специалисты оказывают помощь при следующих состояниях:
Получить дополнительные сведения – нарколог на дом анонимно
Капельница от похмелья в Самаре с устранением симптомов интоксикации и контролем состояния в наркологической клинике «Частный медик 24»
Детальнее – капельница от похмелья вызов на дом
анонимный вызов врача нарколога на дом narkolog-na-dom-moskva-9.ru .
цена на вывод из запоя в стационаре vyvod-iz-zapoya-v-staczionare-sankt-peterburg-8.ru .
1xbet t?rkiye 1xbet t?rkiye .
1xbet giri? yapam?yorum kentseldonusumelkitabi.com .
1xbet giri? adresi 1xbet giri? adresi .
1xbet tr 1xbet tr .
1xbet giri? linki 1xbet giri? linki .
1xbet t?rkiye 1xbet t?rkiye .
игровые автоматы открывают доступ к новых возможностей с минимальными ставками: онлайн играть плей фортуна
https://mhp.ooo/products/twinaqt
Остались только положительные впечатления от покупки. Магазин быстро обработал заказ, а менеджер вежливо ответил на все вопросы. Телефон пришёл в отличном состоянии, без задержек и сюрпризов. Хороший сервис, к которому хочется вернуться: стор 77 официальный сайт
In the middle of exploring different learning and informational materials, I found something that caught my attention see this page and it appears to be a valuable resource offering useful and informative content
частный нарколог на дом быстро narkolog-na-dom-moskva-9.ru .
Со временем столешница теряет внешний вид: появляются царапины, сколы и пятна, которые сложно удалить. Неправильный выбор материала только ускоряет этот процесс и приводит к дополнительным затратам https://medyn.su/materialy-i-fasady-kuhon/obnovlenie-stoleshnicy-dlya-kukhni-polnoe-rukovodstvo/
https://mhp.ooo/products/glivec-400mg
выведение из запоя в наркологическом стационаре vyvod-iz-zapoya-v-staczionare-sankt-peterburg-8.ru .
As I browsed through multiple political campaign and voter information sites, I noticed something placed within the content discover this campaign and it is a political platform sharing policy ideas and vision in a straightforward presentation style
1xbet giri? linki tog.gen.tr .
1xbet t?rkiye giri? athenaofficial.com .
Как seo оптимизация сайта работает для мультиязычных проектов?
Выбор между домашней помощью и стационарным лечением определяется не удобством, а медицинской целесообразностью. В условиях клиники исключаются внешние триггеры, обеспечивается изоляция от источников алкоголя и создается контролируемая среда, где терапевтические решения принимаются на основе объективных показателей, а не субъективных ощущений пациента. Такой подход критически важен для предотвращения осложнений, минимизации дискомфорта абстиненции и формирования устойчивой базы для дальнейшей противорецидивной работы.
Узнать больше – вывод из запоя в стационаре санкт-петербург
фриспины предлагают развлечения с удобным интерфейсом – сайт play fortuna casino
Процедура вывода из запоя на дому включает несколько ключевых этапов, которые обеспечивают максимально быстрое и безопасное восстановление пациента. Эти этапы тщательно контролируются врачом, что минимизирует риски и помогает достичь наилучших результатов.
Подробнее – https://vyvod-iz-zapoya-na-domu-ekaterinburg-20.ru/
Остались только положительные впечатления от покупки. Магазин быстро обработал заказ, а менеджер вежливо ответил на все вопросы. Телефон пришёл в отличном состоянии, без задержек и сюрпризов. Хороший сервис, к которому хочется вернуться: сторис 77 интернет магазин
Процесс лечения строится поэтапно, что позволяет пациенту проходить все стадии восстановления в безопасном и контролируемом режиме.
Исследовать вопрос подробнее – лечение алкоголизма цена донецк
Затяжной запой — это не бытовая слабость, а медицинское состояние, требующее профессионального лечения в условиях стационара. Когда организм истощен длительной интоксикацией, нарушен сон, отсутствует аппетит, а попытки самостоятельно прекратить употребление сопровождаются тремором, тревогой и скачками давления, единственным безопасным решением становится контролируемая детоксикация. Наркологическая клиника «Элегия Мед» в Санкт-Петербурге предоставляет профессиональное лечение с применением сертифицированных протоколов, непрерывный контроль состояния пациента и индивидуальный подбор медикаментозной поддержки. Мы работаем круглосуточно, обеспечивая быстрое реагирование на обращения, четкую диагностику при поступлении и прозрачное взаимодействие с родственниками. Все процедуры выполняются с соблюдением протоколов доказательной медицины, стандартов Минздрава РФ и строгих правил конфиденциальности. Первичная оценка состояния начинается с дистанционной консультации, что позволяет врачам заранее подготовить необходимое оборудование и скорректировать план госпитализации еще до прибытия пациента. При необходимости заказать консультацию или оформить выезд бригады, доступные способы связи включают телефон, мессенджеры и онлайн-форму на сайте.
Получить больше информации – стационар вывод из запоя санкт-петербург
Вывод из запоя в стационаре в Санкт-Петербурге: круглосуточное лечение, детоксикация и медицинский контроль в наркологической клинике «Элегия Мед».
Подробнее тут – быстрый вывод из запоя в стационаре санкт-петербург
Организация терапевтического процесса в условиях стационара требует слаженной работы профильной команды, четких клинических алгоритмов и непрерывного документирования каждого этапа лечения. В клинике выстроена прозрачная система взаимодействия, где пациент и его близкие получают исчерпывающую информацию о планах терапии, ожидаемых результатах, условиях пребывания и правах потребителя медицинских услуг. Мы отказались от шаблонных протоколов в пользу персонализированной медицины, где каждый шаг лечения согласовывается с динамикой состояния пациента и корректируется на основе объективных диагностических данных. Такой подход исключает избыточную фармакологическую нагрузку и минимизирует риски побочных эффектов, сохраняя при этом высокую клиническую эффективность детоксикации.
Выяснить больше – быстрый вывод из запоя в стационаре в нижнем новгороде
Помимо физиологических факторов, важную роль играет психологическая устойчивость пациента. Длительный запой формирует патологическую потребность, при которой человек утрачивает способность добровольно отказаться от очередной дозы в привычной среде. Изоляция в условиях клиники разрывает этот цикл, создавая пространство для мотивационной работы и снижения тревожности. Специалисты клиники работают с когнитивными искажениями, поддерживающими аддикцию, и помогают справиться с внутренним сопротивлением лечению. Такой подход особенно важен при сочетанных расстройствах, когда алкогольная зависимость сопровождается депрессивными проявлениями или генерализованной тревогой.
Выяснить больше – https://vyvod-iz-zapoya-v-staczionare-nizhnij-novgorod-9.ru/
1xbet spor bahislerinin adresi 1xbet spor bahislerinin adresi .
Te joci pe PlayStation? fanjocul.top Cele mai a?teptate ?i deja populare jocuri cu un gameplay excelent, grafica puternica ?i mecanica unica. Afla ce proiecte merita aten?ia ta chiar acum.
Запой – это состояние, при котором человек продолжает употреблять алкоголь в течение длительного времени, не в состоянии прекратить употребление самостоятельно, что является проявлением алкоголизма. Это может привести к серьезным проблемам со здоровьем, и в таком случае необходим вывод из запоя с помощью наркологической помощи, при этом в дальнейшем может рассматриваться кодирование.
Детальнее – https://vyvod-iz-zapoya-na-domu-ekaterinburg-17.ru/
Эти направления терапии помогают создать прочный фундамент для дальнейшей ремиссии и снижают риск рецидива.
Подробнее можно узнать тут – лечение алкоголизма в стационаре донецк
Процедура вывода из запоя на дому включает несколько этапов, каждый из которых имеет важное значение для общего улучшения состояния пациента. Главная цель — это не только устранение симптомов абстиненции, но и восстановление нормальной работы органов и систем организма. Врач, который проводит процедуру, использует медикаментозные средства для восстановления водно-солевого баланса, нормализации работы печени, почек и других органов, пострадавших от алкоголя. Также в процесс включаются препараты, которые способствуют снятию нервного напряжения и психоэмоционального стресса.
Изучить вопрос глубже – нарколог на дом вывод из запоя
xbet giri?i xbet giri?i .
interesat de Gladiatus? Joc Gladiatus Creeaza un erou, lupta in arena, completeaza misiuni ?i imbunata?e?te-?i echipamentul. Alatura-te miilor de jucatori ?i devino un gladiator legendar in acest popular RPG bazat pe browser.
1xbet t?rkiye giri? 1xbet t?rkiye giri? .
Cel mai bun joc Joc wow Un MMORPG legendar cu o lume deschisa vasta, unde te a?teapta batalii epice, progresul personajelor ?i misiuni palpitante. Exploreaza Azeroth, alatura-te breslelor ?i devino parte a unei pove?ti grandioase.
вывод из запоя цена наркология vyvod-iz-zapoya-v-staczionare-sankt-peterburg-8.ru .
выведение из запоя на дому круглосуточно narkolog-na-dom-moskva-9.ru .
1xbet spor bahislerinin adresi 1xbet spor bahislerinin adresi .
1xbet 1xbet .
Iti place entuziasmul? jocuridenoroc.top Cazinouri online, case de pariuri ?i sali de jocuri de noroc licen?iate. Cele mai bune jocuri de noroc online.
Непрерывный мониторинг витальных показателей — ключевое отличие стационарного формата, обеспечивающее безопасную детоксикацию. В палатах клиники «Элегия Мед» установлены системы отслеживания частоты пульса, сатурации, температуры и артериального давления, данные с которых автоматически передаются в электронную медицинскую карту. Медицинский персонал дежурит круглосуточно, что обеспечивает мгновенную реакцию на ухудшение состояния: коррекцию инфузионной терапии, введение симптоматических препаратов, привлечение смежных специалистов при необходимости. Такая организация процесса исключает хаотичное назначение средств, предотвращает полипрагмазию и гарантирует, что каждый этап детоксикации проходит под строгим клиническим контролем. При необходимости применяются дополнительные методы очищения крови, включая плазмаферез, который эффективно помогает вывести стойкие токсины и метаболиты, не удаляемые стандартной инфузионной терапией.
Изучить вопрос глубже – вывод из запоя в стационаре
Процедура вывода из запоя на дому включает несколько ключевых этапов, которые обеспечивают максимально быстрое и безопасное восстановление пациента. Эти этапы тщательно контролируются врачом, что минимизирует риски и помогает достичь наилучших результатов.
Изучить вопрос глубже – http://vyvod-iz-zapoya-na-domu-ekaterinburg-20.ru/
1xbet t?rkiye 1xbet t?rkiye .
Непрерывный мониторинг витальных показателей — ключевое отличие стационарного формата. В палатах клиники «Элегия Мед» установлены системы отслеживания частоты пульса, сатурации, температуры и артериального давления, данные с которых автоматически передаются в электронную медицинскую карту. Медицинский персонал дежурит круглосуточно, что обеспечивает мгновенную реакцию на ухудшение состояния: коррекцию инфузионной терапии, введение симптоматических препаратов, привлечение смежных специалистов при необходимости. Такая организация процесса исключает хаотичное назначение средств, предотвращает полипрагмазию и гарантирует, что каждый этап детоксикации проходит под строгим клиническим контролем. Контроль состояния пациента в режиме реального времени позволяет врачам оперативно корректировать терапию и минимизировать риски для здоровья.
Подробнее можно узнать тут – наркология вывод из запоя в стационаре
В клинике применяются методы, позволяющие воздействовать на все аспекты зависимости. Это обеспечивает комплексное и устойчивое восстановление.
Узнать больше – здоровье лечение алкоголизма в донце
cocorico shop https://darknetmarketstore.com/
К показаниям относятся: запой длительностью более 72 часов, выраженная абстиненция с тахикардией, артериальной гипертензией, профузным потоотделением, наличие в анамнезе алкогольных делириев или судорожных эпизодов, сопутствующие хронические заболевания печени, сердца, поджелудочной железы. При тяжелых формах интоксикации, когда в организме накапливаются токсичные продукты распада веществ, резкое прекращение употребления без медицинской поддержки может спровоцировать отек мозга, острую сердечную недостаточность или желудочно-кишечное кровотечение. Стационар позволяет провести полноценную диагностику, включая ЭКГ, экспресс-анализы крови и мониторинг сатурации, что формирует точную картину состояния и исключает шаблонные назначения. В случаях сочетанной зависимости, когда в анамнезе присутствует наркомании, протоколы детоксикации адаптируются под специфику психоактивных соединений и включают усиленный нейрологический контроль.
Узнать больше – http://vyvod-iz-zapoya-v-staczionare-sankt-peterburg-16.ru
Принятие решения о госпитализации часто сопровождается внутренними сомнениями и попытками найти альтернативные пути решения проблемы. Однако современные клинические протоколы четко определяют ситуации, когда амбулаторный формат не способен обеспечить должный уровень безопасности и эффективности. Стационарное лечение назначается тогда, когда интоксикация затрагивает несколько систем организма одновременно, а риск развития соматических или психиатрических осложнений превышает допустимые пределы. В условиях медицинского учреждения исключается доступ к психоактивным веществам, обеспечивается изоляция от бытовых триггеров и создается контролируемая среда, способствующая физиологической стабилизации. Такой подход особенно важен для пациентов с длительным стажем употребления, когда самостоятельные попытки прекращения приводят к тяжелым абстинентным состояниям, требующим инфузионной поддержки и постоянного врачебного контроля.
Получить дополнительные сведения – https://vyvod-iz-zapoya-v-staczionare-nizhnij-novgorod-7.ru/
Наркологический стационар с круглосуточным наблюдением — это не просто место для детоксикации, но и пространство для комплексного лечения и реабилитации. Постоянное присутствие медицинского персонала помогает избежать опасных ситуаций, таких как психозы или физиологические сбои, характерные для абстиненции. Прием пациентов может включать кодирование, а также индивидуальные программы лечения, которые разрабатываются в зависимости от состояния пациента и его потребностей на протяжении года.
Ознакомиться с деталями – лечение в наркологическом стационаре
Основой стационарной детоксикации является инфузионная терапия, направленная на выведение токсинов, коррекцию водно-электролитного баланса и восстановление метаболических процессов. Капельницы включают кристаллоидные растворы, витамины группы B и C, гепатопротекторы, антиоксиданты и симптоматические препараты для нормализации сна. Состав и скорость введения рассчитываются индивидуально, чтобы избежать перегрузки сердечно-сосудистой системы. При выраженной абстиненции подключаются средства для коррекции нейромедиаторного обмена, однако их применение строго дозируется. Дозировки пересматриваются ежедневно на основе динамики показателей, что обеспечивает безопасность и эффективность терапии.
Изучить вопрос глубже – наркология вывод из запоя в стационаре в нижнем новгороде
Первый этап вывода из запоя на дому – это первичная оценка состояния пациента. Врач, прибывший на вызов, осматривает пациента, проверяет уровень алкоголя в крови, измеряет артериальное давление, пульс и температуру. Это необходимо для того, чтобы определить степень алкогольной интоксикации и выбрать правильную тактику лечения.
Разобраться лучше – нарколог на дом вывод из запоя екатеринбург
Во всех этих случаях врач нужен не только для облегчения симптомов. Его задача — понять, можно ли ограничиться домашней терапией или уже сейчас необходимо менять маршрут лечения. Именно этот этап и делает домашний выезд профессиональной услугой, а не упрощённой заменой клиники.
Ознакомиться с деталями – нарколог на дом в воронеже
При выводе из запоя на дому с быстрым облегчением используются различные медикаменты, направленные на быстрое восстановление водно-солевого баланса, улучшение функции печени и почек, а также снижение симптомов алкогольного абстинентного синдрома. Важно, что состав препаратов подбирается в зависимости от состояния пациента, и все препараты вводятся под контролем квалифицированного медицинского специалиста.
Получить больше информации – http://www.domen.ru
1xbet giri? adresi 1xbet giri? adresi .
вывод из запоя с выездом вывод из запоя с выездом .
Наиболее частыми причинами обращения становятся выраженная слабость, тремор, нарушение сна, тревога, учащенный пульс, скачки артериального давления, тошнота и признаки обезвоживания. Эти симптомы могут сочетаться между собой и усиливаться после прекращения употребления алкоголя, особенно после нескольких дней запоя.
Получить дополнительную информацию – запой нарколог на дом в екатеринбурге
1xbet g?ncel giri? 1xbet g?ncel giri? .
помощь нарколога на дому при алкоголизме narkolog-na-dom-moskva-9.ru .
Врач-нарколог, оценивая состояние пациента, может рекомендовать проведение капельницы для ускоренного восстановления организма. Применение капельницы позволяет снять острые симптомы интоксикации и снизить риск развития более серьезных последствий. В некоторых случаях, если необходимо интенсивное наблюдение, пациенту может быть предложено лечение в стационаре, и услугу можно заказать на летний период для более длительного контроля.
Подробнее можно узнать тут – капельница от запоя на дому цена в нижнем новгороде
Реабилитация алкоголиков с анонимной поддержкой — это процесс, при котором пациент получает необходимую медицинскую и психологическую помощь, не раскрывая своей личности и обстоятельств зависимости, включая лечение наркомании. Такие программы ориентированы на безопасное и конфиденциальное лечение, что важно для тех, кто стремится избавиться от зависимости, но опасается осуждения или утраты личной репутации, при этом возможен выезд нарколога на дом. Важно, что анонимность не ограничивает качество предоставляемых услуг: все необходимые этапы лечения, включая детоксикацию, психотерапевтические сессии и социальную реабилитацию, которые могут длиться несколько лет, проводятся на высоком уровне с акцентом на своевременный вывод из состояния зависимости.
Узнать больше – реабилитация алкоголиков город
Нарколог на дом в Самаре: круглосуточная помощь, вывод из запоя и медицинская поддержка на дому под контролем специалистов в наркологической клинике «Похмельная служба»
Подробнее можно узнать тут – вызвать нарколога на дом
Препараты, введённые через капельницу, начинают действовать почти сразу. Они поступают напрямую в кровоток, обходя желудочно-кишечный тракт, что позволяет ускорить процесс восстановления и устранить симптомы похмелья, такие как головная боль, тошнота и слабость, уже через 20–30 минут после начала процедуры.
Ознакомиться с деталями – капельница от похмелья в нижнем новгороде
За выездом врача чаще обращаются тогда, когда человеку тяжело добраться до клиники, он ослаблен после нескольких дней употребления алкоголя или родственникам важно быстрее понять, какая тактика будет безопасной. После осмотра можно определить, нужна ли капельница, достаточно ли детоксикации на дому, требуется ли повторное наблюдение, а в дальнейшем — консультация по лечению алкоголизма, кодирование или реабилитация. В части случаев уже первый звонок позволяет понять, идет ли речь только о временном ухудшении самочувствия или о состоянии, при котором может потребоваться вывод из запоя в стационаре.
Детальнее – вызвать нарколога на дом
За выездом врача обращаются в тех случаях, когда человеку тяжело добраться до клиники, он ослаблен после нескольких дней употребления спиртного или родственникам важно быстрее получить медицинскую консультацию на месте. После осмотра определяют, допустим ли домашний формат, требуется ли капельница, достаточно ли наблюдения на дому или нужен другой объем помощи. Если эпизоды повторяются, в дальнейшем могут обсуждаться лечение алкоголизма, кодирование, участие психолога, реабилитация и более широкая программа помощи при зависимости. Уже на этапе первичного обращения нередко уточняют, как вызвать специалиста, какие услуги доступны на дому и в каких случаях вывод из запоя рассматривают не дома, а в стационаре.
Выяснить больше – нарколог на дом вывод
1xbet t?rkiye 1xbet t?rkiye .
Нарколог на дом в Москве: срочная медицинская помощь, капельницы и восстановление состояния в наркологической клинике «Клиника доктора Калюжной».
Получить дополнительные сведения – вызвать нарколога на дом москва
Нарколог на дом в Москве: круглосуточный выезд, детоксикация и лечение зависимостей в наркологической клинике «Клиника доктора Калюжной».
Исследовать вопрос подробнее – http://www.domen.ru
Терапевтический процесс в стационаре строится по принципу последовательного выполнения клинических задач: диагностика, стабилизация, медикаментозная поддержка и подготовка к амбулаторному этапу. При поступлении врач проводит детальный осмотр, собирает анамнез, оценивает неврологический статус и при необходимости назначает лабораторные исследования. На основе полученных данных формируется индивидуальный протокол, учитывающий возраст, длительность интоксикации, наличие сопутствующих патологий и переносимость лекарственных компонентов. Мы применяем только сертифицированные препараты, зарегистрированные в РФ, и строго соблюдаем клинические рекомендации Минздрава, исключая псевдонаучные методики. Стандарты оказания медицинской помощи фиксируются во внутренних регламентах и регулярно проверяются независимыми аудиторами.
Исследовать вопрос подробнее – вывод из запоя в стационаре клиника санкт-петербург
References:
Fair Go https://graph.org/Rocketplay-Casino-Australia-Expert-Review–Bonuses-04-20 license
Непрерывное наблюдение — ключевое отличие стационарного формата. В палатах клиники «Стармед» установлены системы мониторинга витальных показателей, позволяющие фиксировать изменения артериального давления, частоты пульса, температуры и дыхания в реальном времени. Медицинский персонал дежурит круглосуточно, что обеспечивает мгновенную реакцию на ухудшение состояния: коррекцию инфузионной терапии, введение симптоматических препаратов, привлечение профильного психиатра при необходимости. Кроме того, стационар создает терапевтическую среду, свободную от бытовых конфликтов, финансовых стрессов и социального давления, которые часто провоцируют срыв в первые дни трезвости. Пациент получает режим, адаптированный под этап восстановления: дозированную физическую активность, сбалансированное диетическое питание, физиотерапевтические процедуры и регулярные консультации с психотерапевтом. Такой комплексный подход минимизирует дискомфорт и формирует базу для последующей психологической работы.
Изучить вопрос глубже – вывод из запоя в стационаре анонимно нижний новгород
Терапевтический процесс в стационаре строится по принципу последовательного выполнения клинических задач: диагностика, стабилизация, медикаментозная поддержка и подготовка к амбулаторному этапу. При поступлении врач проводит детальный осмотр, собирает анамнез, оценивает неврологический статус и при необходимости назначает лабораторные исследования. На основе полученных данных формируется индивидуальный протокол, учитывающий возраст, длительность интоксикации, наличие сопутствующих патологий и переносимость лекарственных компонентов. Мы применяем только сертифицированные препараты, зарегистрированные в РФ, и строго соблюдаем клинические рекомендации Минздрава, исключая псевдонаучные методики. Стандарты оказания медицинской помощи фиксируются во внутренних регламентах и регулярно проверяются независимыми аудиторами.
Углубиться в тему – https://vyvod-iz-zapoya-v-staczionare-sankt-peterburg-17.ru
Первоначально врач оценивает физическое и психоэмоциональное состояние пациента, что позволяет определить степень тяжести запоя и риски, с которыми может столкнуться пациент в процессе восстановления. На основе этой оценки подбирается соответствующая терапия, включая капельницы для очистки организма, введение витаминов и препаратов, способствующих нормализации давления и уровня сахара в крови.
Получить дополнительную информацию – вывод из запоя на дому круглосуточно в екатеринбурге
Для семьи это тоже имеет большое значение. Пока врач в пути, родственники часто совершают одни и те же ошибки: пытаются «отпаивать» человека через силу, смешивают несовместимые медикаменты, дают советы, которые только повышают тревогу, спорят или требуют немедленно взять себя в руки. Профессиональный выезд снимает эту хаотичность. После осмотра врач объясняет, какие симптомы связаны с алкогольной интоксикацией, какие могут указывать на осложнения, что допустимо дома, а что требует перевода в стационар. В этом и состоит ценность выезда: он возвращает контроль над ситуацией и позволяет начать лечение без лишних задержек.
Получить больше информации – нарколог на дом цена
Домашняя детоксикация подходит для ранних стадий интоксикации, когда состояние пациента стабильно, а сопутствующие заболевания отсутствуют. Однако при длительном употреблении алкоголя физиологические изменения требуют более глубокого вмешательства. Стационар обеспечивает изоляцию от триггеров, исключает риск самостоятельного повторного употребления и позволяет врачам динамически корректировать терапию на основе лабораторных показателей и реакции организма. В 2026 году стандарты наркологической помощи делают акцент на превентивной безопасности: раннее выявление признаков делирия, судорожной готовности или кардиологических осложнений позволяет предотвратить критические состояния до их развития. Клиника «Стармед» выстроила работу так, чтобы каждый этап госпитализации логически вытекал из предыдущего, формируя непрерывную цепочку от острой стабилизации до планирования долгосрочной ремиссии.
Изучить вопрос глубже – наркология вывод из запоя в стационаре
Отдельного внимания требуют случаи, когда больной почти не ест, плохо пьет воду, не может спокойно лежать, жалуется на сильное сердцебиение, нехватку сна или выраженное внутреннее напряжение. В такой ситуации осмотр помогает определить, безопасно ли оставаться дома и какого объема помощи достаточно на текущем этапе. Если речь идет о выраженных проявлениях абстинентного синдрома, затягивать с обращением нецелесообразно.
Выяснить больше – нарколог на дом цена екатеринбург
Вывод из запоя на дому в Екатеринбурге: срочная помощь, детоксикация и восстановление под контролем специалистов в наркологической клинике «Детокс»
Получить дополнительные сведения – вывод из запоя на дому круглосуточно екатеринбург
Наиболее частыми основаниями для выбора такого формата становятся длительный запой, тяжелое течение похмельного синдрома, выраженный тремор, отсутствие сна, тревога, слабость, обезвоживание и жалобы на сердцебиение. Дополнительное значение имеют хронические заболевания сердца, сосудов, печени и нервной системы, на фоне которых выход из запоя может переноситься тяжелее.
Узнать больше – http://vyvod-iz-zapoya-v-staczionare-sankt-peterburg-19.ru
While exploring inspiring storytelling and personal narrative platforms online, I came across something placed within the content visit this story platform and it is an inspiring storytelling site sharing powerful personal experiences from many different lives
Длительное употребление алкоголя переводит организм в состояние хронической интоксикации, при котором собственные механизмы восстановления перестают справляться с нагрузкой. Накопление ацетальдегида, дефицит электролитов, нарушение работы печени и сердечно-сосудистой системы создают клиническую картину, требующую не симптоматического облегчения, а комплексного медицинского вмешательства. Вывод из запоя в стационаре в Нижнем Новгороде в наркологической клинике «Стармед» организован с соблюдением современных протоколов доказательной медицины, где безопасность пациента, непрерывный мониторинг и персонализированный подбор терапии являются приоритетом. Мы работаем круглосуточно, обеспечивая быстрое реагирование на обращения, четкую диагностику при поступлении и прозрачное взаимодействие с родственниками. Чтобы вызвать специалистов или лечиться в безопасных условиях, достаточно оставить заявку на сайте или позвонить по прямой линии. Все процедуры проводятся в лицензированных помещениях, с документированием каждого этапа и строгим соблюдением врачебной этики. Первичная оценка состояния начинается с дистанционной консультации, что позволяет врачам заранее подготовить необходимые препараты и скорректировать план госпитализации еще до прибытия пациента.
Получить больше информации – http://vyvod-iz-zapoya-v-staczionare-nizhnij-novgorod-8.ru/
Наркологический стационар в Санкт-Петербурге: круглосуточное лечение, детоксикация и наблюдение специалистов в комфортных условиях в наркологической клинике «Похмельная служба»
Подробнее – лечение в наркологическом стационаре санкт-петербург
Вывод из запоя на дому с медицинским контролем в Екатеринбурге предлагает множество преимуществ, которые делают этот метод более удобным и безопасным для многих людей. Отсутствие необходимости в госпитализации и наличие профессионального контроля являются основными положительными аспектами этой услуги.
Изучить вопрос глубже – вывод из запоя на дому цена
Стационарное наблюдение также целесообразно тогда, когда больному трудно соблюдать рекомендации дома, состояние быстро меняется или родственники не могут обеспечить полноценный контроль. В таких условиях медицинское сопровождение позволяет своевременно оценивать динамику и корректировать лечение. При выраженных психических нарушениях, тревожно-депрессивных проявлениях или изменении поведения к оценке состояния может подключаться психиатр, поскольку у части больных запой сопровождается не только соматическими, но и психическими осложнениями алкогольной зависимости.
Подробнее можно узнать тут – быстрый вывод из запоя в стационаре санкт-петербург
Не каждый человек с зависимостью от алкоголя готов признать свою проблему и обратиться за помощью. Однако, когда зависимость достигает тяжелых форм, требуется профессиональное вмешательство, и комплексная реабилитация в наркологическом доме становится важнейшим этапом восстановления, при этом в некоторых случаях помощь может предоставляться бесплатно, а сама программа рассчитана на длительный срок — до нескольких лет. Признаки того, что нужна реабилитация, могут включать невозможность прекратить пить даже при наличии серьезных последствий для здоровья, социальной жизни и межличностных отношений.
Узнать больше – https://reabilitacziya-alkogolikov-moskva-2.ru/
Чому свербіж долонь
Вывод из запоя в стационаре в Нижнем Новгороде: профессиональное лечение, капельницы и контроль состояния пациента в наркологической клинике «Стармед».
Выяснить больше – http://www.domen.ru
Несмотря на кажущуюся простоту процедуры, капельница требует профессионального подхода. Неправильно подобранные препараты или дозировки могут привести к осложнениям, особенно при хронических заболеваниях. Поэтому проведение процедуры под контролем специалиста является ключевым фактором эффективности и безопасности.
Углубиться в тему – https://kapelnicza-ot-pokhmelya-samara-7.ru
Вывод из запоя в стационаре в Нижнем Новгороде: безопасная детоксикация, медикаментозная терапия и поддержка специалистов в наркологической клинике «Стармед».
Получить дополнительные сведения – http://vyvod-iz-zapoya-v-staczionare-nizhnij-novgorod-8.ru/
Вывод из запоя на дому с медицинским контролем — это процесс, при котором нарколог или медсестра приезжает к пациенту на дом для проведения необходимых процедур. Основной задачей является снятие абстинентного синдрома, восстановление водно-электролитного баланса и нормализация общего состояния пациента, при этом оказывается наркологическая помощь. Этот процесс проходит под наблюдением квалифицированных специалистов, что помогает избежать осложнений, часто возникающих при самостоятельном выходе из запоя, а в дальнейшем может потребоваться кодирование и реабилитация.
Получить дополнительную информацию – анонимный вывод из запоя на дому
Для Воронежа выездной формат особенно востребован вечером, ночью и ранним утром, когда у больного резко усиливаются симптомы и поездка в медицинское учреждение становится тяжёлой или просто нереальной. Если человек несколько дней употреблял алкоголь, почти не спал, плохо переносит воду, жалуется на сердцебиение и слабость, то откладывать осмотр не стоит. Срочная наркологическая помощь нужна именно тогда, когда ситуация развивается быстро, а семья уже видит, что своими силами справиться не удаётся. Врач приезжает, проводит осмотр, определяет, нет ли признаков осложнений, и уже на месте решает, какие меры допустимы дома, а какие требуют другого формата оказания помощи.
Узнать больше – нарколог на дом вывод в воронеже
За выездом врача обращаются в тех случаях, когда человеку тяжело добраться до клиники, он ослаблен после нескольких дней употребления спиртного или родственникам важно быстрее получить медицинскую консультацию на месте. После осмотра определяют, допустим ли домашний формат, требуется ли капельница, достаточно ли наблюдения на дому или нужен другой объем помощи. Если эпизоды повторяются, в дальнейшем могут обсуждаться лечение алкоголизма, кодирование, участие психолога, реабилитация и более широкая программа помощи при зависимости. Уже на этапе первичного обращения нередко уточняют, как вызвать специалиста, какие услуги доступны на дому и в каких случаях вывод из запоя рассматривают не дома, а в стационаре.
Узнать больше – запой нарколог на дом
Вывод из запоя в стационаре в Нижнем Новгороде: профессиональное лечение, капельницы и контроль состояния пациента в наркологической клинике «Стармед».
Углубиться в тему – нарколог вывод из запоя в стационаре нижний новгород
1xbet yeni giri? adresi 1xbet yeni giri? adresi .
вывести из запоя цена вывести из запоя цена .
1xbet giri? linki athenaofficial.com .
https://pravdadaily.com.ua/sidney-stolytsia-chy-spravdi-tse-naybilsh-rozvynene-misto-avstralii/
За выездом врача чаще обращаются тогда, когда человеку тяжело добраться до клиники, он ослаблен после нескольких дней употребления алкоголя или родственникам важно быстрее понять, какая тактика будет безопасной. После осмотра можно определить, нужна ли капельница, достаточно ли детоксикации на дому, требуется ли повторное наблюдение, а в дальнейшем — консультация по лечению алкоголизма, кодирование или реабилитация. В части случаев уже первый звонок позволяет понять, идет ли речь только о временном ухудшении самочувствия или о состоянии, при котором может потребоваться вывод из запоя в стационаре.
Углубиться в тему – врач нарколог на дом екатеринбург
гидроизоляция подвала изнутри от грунтовых вод цена за м2 москва remont-betona-4.ru .
Реабилитация алкоголиков с анонимной поддержкой — это важный процесс, который помогает людям справиться с зависимостью в условиях конфиденциальности и безопасности. Многие пациенты опасаются обращаться за помощью из-за стереотипов и страха осуждения. Анонимность в реабилитации становится важным фактором для обеспечения доверия и максимальной эффективности лечения, при этом в ряде случаев доступны такие услуги, как кодирование и консультации наркологической помощи бесплатно, особенно при обращении после запоя. В Москве существует множество центров, которые предлагают реабилитацию алкоголиков с анонимной поддержкой, что позволяет пациентам пройти лечение, не раскрывая своей личности и не беспокоясь о социальном осуждении.
Исследовать вопрос подробнее – https://reabilitacziya-alkogolikov-moskva-4.ru/
капремонт и реконструкция remont-zdaniya-3.ru .
ремонт бетонных конструкций компания ремонт бетонных конструкций компания .
гидроизоляция подвала изнутри от грунтовых вод купить gidroizolyacziya-podvalov-2.ru .
капитальный ремонт и реконструкция в чем разница капитальный ремонт и реконструкция в чем разница .
гидроизоляция подвала цена гидроизоляция подвала цена .
Как поясняет нарколог Дмитрий Кузнецов: “Реабилитация алкоголиков должна быть многогранной. Только при сочетании медицинских и психологических методов, а также поддержке со стороны специалистов на всех этапах лечения, можно добиться устойчивого результата. Психологическая работа с пациентом помогает ему не только преодолеть зависимость, но и восстановить нормальное функционирование в обществе.” Также стоит отметить, что в некоторых случаях помощь может быть предоставлена бесплатно, и пациент может получить доступ к данным о возможных вариантах бесплатной реабилитации, что значительно облегчает процесс выздоровления.
Узнать больше – центр реабилитации алкоголиков
Наша клиника предлагает полный цикл услуг — от экстренного вызова нарколога до долгосрочной реабилитации. Каждый этап разрабатывается индивидуально с учётом возраста, стажа зависимости и сопутствующих заболеваний. Современные протоколы 2026 года позволяют проводить лечение максимально комфортно и эффективно, минимизируя болезненные симптомы и снижая риск срывов. В этом виде деятельности мы используем только проверенные методы медицины.
Детальнее – narkolog-na-dom-ekaterinburg-1.ru/